The output is below and router B, the ASUS router, was connected to LAN 4 when the commands were run. The ASUS router has its default configuration where it tries to obtain an IP via DHCP. Although I assume it is not important, the ASUS LAN IP is 192.168.150.x and the OpenWRT tries to give it a WAN IP in 192.168.200.x.
root@OpenWrt:~# uci export network; uci export dhcp; uci export firewall;
package network
config interface 'loopback'
option ifname 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'xyz:xyz:xyz::/48'
config interface 'lan'
option type 'bridge'
option ifname 'eth1.1'
option proto 'static'
option ipaddr '192.168.1.1'
option netmask '255.255.255.0'
option ip6assign '60'
config interface 'wan'
option ifname 'eth0.2'
option proto 'dhcp'
list dns '1.1.1.1'
list dns '1.0.0.1'
option peerdns '0'
config interface 'wan6'
option ifname 'eth0.2'
option proto 'dhcpv6'
list dns '1.1.1.1'
list dns '1.0.0.1'
option reqprefix 'auto'
option reqaddress 'try'
option peerdns '0'
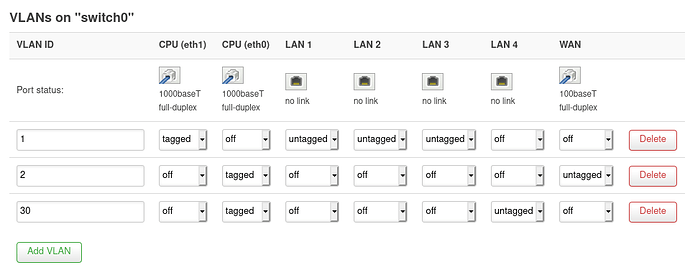
config switch
option name 'switch0'
option reset '1'
option enable_vlan '1'
config switch_vlan
option device 'switch0'
option vlan '1'
option vid '1'
option ports '4 3 2 0t'
config switch_vlan
option device 'switch0'
option vlan '2'
option ports '6t 1'
option vid '2'
config interface 'guest'
option proto 'static'
option ipaddr '192.168.100.1'
option netmask '255.255.255.0'
config switch_vlan
option device 'switch0'
option vlan '3'
option vid '30'
option ports '5 0t'
config interface 'isolated_if4'
option ifname 'eth0.30'
option proto 'static'
option ipaddr '192.168.200.1'
option netmask '255.255.255.0'
package dhcp
config dnsmasq
option domainneeded '1'
option boguspriv '1'
option filterwin2k '0'
option localise_queries '1'
option rebind_protection '1'
option rebind_localhost '1'
option local '/lan/'
option domain 'lan'
option expandhosts '1'
option nonegcache '0'
option authoritative '1'
option readethers '1'
option leasefile '/tmp/dhcp.leases'
option resolvfile '/tmp/resolv.conf.auto'
option nonwildcard '1'
option localservice '1'
config dhcp 'lan'
option interface 'lan'
option start '100'
option limit '150'
option leasetime '12h'
option dhcpv6 'server'
option ra 'server'
config dhcp 'wan'
option interface 'wan'
option ignore '1'
config odhcpd 'odhcpd'
option maindhcp '0'
option leasefile '/tmp/hosts/odhcpd'
option leasetrigger '/usr/sbin/odhcpd-update'
option loglevel '4'
config dhcp 'guest'
option start '100'
option limit '150'
option interface 'guest'
option leasetime '6h'
config dhcp 'isolated_if4'
option start '100'
option leasetime '12h'
option limit '150'
option interface 'isolated_if4'
package firewall
config defaults
option syn_flood '1'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
config zone
option name 'lan'
list network 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
config zone
option name 'wan'
list network 'wan'
list network 'wan6'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
config forwarding
option src 'lan'
option dest 'wan'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
option enabled '0'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option src_ip 'fc00::/6'
option dest_ip 'fc00::/6'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config include
option path '/etc/firewall.user'
config zone
option network 'guest'
option forward 'REJECT'
option name 'guest'
option output 'ACCEPT'
option input 'REJECT'
config forwarding
option dest 'wan'
option src 'guest'
config rule
option dest_port '53'
option src 'guest'
option name 'Guest DNS'
option target 'ACCEPT'
config rule
option src 'guest'
option target 'ACCEPT'
list proto 'udp'
option name 'Guest DHCP'
option dest_port '67-68'
config forwarding
option dest 'wan'
option src 'isolated_4'
config rule
option dest_port '53'
option src 'isolated_4'
option name 'Isolated port 4 DNS'
option target 'ACCEPT'
config rule
option dest_port '67-68'
option src 'isolated_4'
option name 'Isolated port 4 DHCP'
option target 'ACCEPT'
list proto 'udp'
config zone
option name 'isolated_4'
option forward 'REJECT'
option network 'isolated_4 isolated_if4'
option output 'ACCEPT'
option input 'REJECT'
root@OpenWrt:~# iptables-save -c;
# Generated by iptables-save v1.8.3 on Sat May 23
*nat
:PREROUTING ACCEPT [129:15273]
:INPUT ACCEPT [57:3837]
:OUTPUT ACCEPT [81:6171]
:POSTROUTING ACCEPT [8:884]
:postrouting_guest_rule - [0:0]
:postrouting_isolated_4_rule - [0:0]
:postrouting_lan_rule - [0:0]
:postrouting_rule - [0:0]
:postrouting_wan_rule - [0:0]
:prerouting_guest_rule - [0:0]
:prerouting_isolated_4_rule - [0:0]
:prerouting_lan_rule - [0:0]
:prerouting_rule - [0:0]
:prerouting_wan_rule - [0:0]
:zone_guest_postrouting - [0:0]
:zone_guest_prerouting - [0:0]
:zone_isolated_4_postrouting - [0:0]
:zone_isolated_4_prerouting - [0:0]
:zone_lan_postrouting - [0:0]
:zone_lan_prerouting - [0:0]
:zone_wan_postrouting - [0:0]
:zone_wan_prerouting - [0:0]
[129:15273] -A PREROUTING -m comment --comment "!fw3: Custom prerouting rule chain" -j prerouting_rule
[76:6401] -A PREROUTING -i br-lan -m comment --comment "!fw3" -j zone_lan_prerouting
[53:8872] -A PREROUTING -i eth0.2 -m comment --comment "!fw3" -j zone_wan_prerouting
[0:0] -A PREROUTING -i wlan1-1 -m comment --comment "!fw3" -j zone_guest_prerouting
[0:0] -A PREROUTING -i eth0.30 -m comment --comment "!fw3" -j zone_isolated_4_prerouting
[118:7871] -A POSTROUTING -m comment --comment "!fw3: Custom postrouting rule chain" -j postrouting_rule
[2:376] -A POSTROUTING -o br-lan -m comment --comment "!fw3" -j zone_lan_postrouting
[110:6987] -A POSTROUTING -o eth0.2 -m comment --comment "!fw3" -j zone_wan_postrouting
[0:0] -A POSTROUTING -o wlan1-1 -m comment --comment "!fw3" -j zone_guest_postrouting
[0:0] -A POSTROUTING -o eth0.30 -m comment --comment "!fw3" -j zone_isolated_4_postrouting
[0:0] -A zone_guest_postrouting -m comment --comment "!fw3: Custom guest postrouting rule chain" -j postrouting_guest_rule
[0:0] -A zone_guest_prerouting -m comment --comment "!fw3: Custom guest prerouting rule chain" -j prerouting_guest_rule
[0:0] -A zone_isolated_4_postrouting -m comment --comment "!fw3: Custom isolated_4 postrouting rule chain" -j postrouting_isolated_4_rule
[0:0] -A zone_isolated_4_prerouting -m comment --comment "!fw3: Custom isolated_4 prerouting rule chain" -j prerouting_isolated_4_rule
[2:376] -A zone_lan_postrouting -m comment --comment "!fw3: Custom lan postrouting rule chain" -j postrouting_lan_rule
[76:6401] -A zone_lan_prerouting -m comment --comment "!fw3: Custom lan prerouting rule chain" -j prerouting_lan_rule
[110:6987] -A zone_wan_postrouting -m comment --comment "!fw3: Custom wan postrouting rule chain" -j postrouting_wan_rule
[110:6987] -A zone_wan_postrouting -m comment --comment "!fw3" -j MASQUERADE
[53:8872] -A zone_wan_prerouting -m comment --comment "!fw3: Custom wan prerouting rule chain" -j prerouting_wan_rule
COMMIT
# Completed on Sat May 23
# Generated by iptables-save v1.8.3 on Sat May 23
*mangle
:PREROUTING ACCEPT [1828:221344]
:INPUT ACCEPT [1456:128628]
:FORWARD ACCEPT [364:90812]
:OUTPUT ACCEPT [1956:477574]
:POSTROUTING ACCEPT [2286:567026]
[11:660] -A FORWARD -o eth0.2 -p tcp -m tcp --tcp-flags SYN,RST SYN -m comment --comment "!fw3: Zone wan MTU fixing" -j TCPMSS --clamp-mss-to-pmtu
COMMIT
# Completed on Sat May 23
# Generated by iptables-save v1.8.3 on Sat May 23
*filter
:INPUT ACCEPT [0:0]
:FORWARD DROP [0:0]
:OUTPUT ACCEPT [0:0]
:forwarding_guest_rule - [0:0]
:forwarding_isolated_4_rule - [0:0]
:forwarding_lan_rule - [0:0]
:forwarding_rule - [0:0]
:forwarding_wan_rule - [0:0]
:input_guest_rule - [0:0]
:input_isolated_4_rule - [0:0]
:input_lan_rule - [0:0]
:input_rule - [0:0]
:input_wan_rule - [0:0]
:output_guest_rule - [0:0]
:output_isolated_4_rule - [0:0]
:output_lan_rule - [0:0]
:output_rule - [0:0]
:output_wan_rule - [0:0]
:reject - [0:0]
:syn_flood - [0:0]
:zone_guest_dest_ACCEPT - [0:0]
:zone_guest_dest_REJECT - [0:0]
:zone_guest_forward - [0:0]
:zone_guest_input - [0:0]
:zone_guest_output - [0:0]
:zone_guest_src_REJECT - [0:0]
:zone_isolated_4_dest_ACCEPT - [0:0]
:zone_isolated_4_dest_REJECT - [0:0]
:zone_isolated_4_forward - [0:0]
:zone_isolated_4_input - [0:0]
:zone_isolated_4_output - [0:0]
:zone_isolated_4_src_REJECT - [0:0]
:zone_lan_dest_ACCEPT - [0:0]
:zone_lan_forward - [0:0]
:zone_lan_input - [0:0]
:zone_lan_output - [0:0]
:zone_lan_src_ACCEPT - [0:0]
:zone_wan_dest_ACCEPT - [0:0]
:zone_wan_dest_REJECT - [0:0]
:zone_wan_forward - [0:0]
:zone_wan_input - [0:0]
:zone_wan_output - [0:0]
:zone_wan_src_REJECT - [0:0]
[46:4781] -A INPUT -i lo -m comment --comment "!fw3" -j ACCEPT
[1412:123951] -A INPUT -m comment --comment "!fw3: Custom input rule chain" -j input_rule
[1231:106459] -A INPUT -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
[40:2072] -A INPUT -p tcp -m tcp --tcp-flags FIN,SYN,RST,ACK SYN -m comment --comment "!fw3" -j syn_flood
[85:6179] -A INPUT -i br-lan -m comment --comment "!fw3" -j zone_lan_input
[96:11313] -A INPUT -i eth0.2 -m comment --comment "!fw3" -j zone_wan_input
[0:0] -A INPUT -i wlan1-1 -m comment --comment "!fw3" -j zone_guest_input
[0:0] -A INPUT -i eth0.30 -m comment --comment "!fw3" -j zone_isolated_4_input
[364:90812] -A FORWARD -m comment --comment "!fw3: Custom forwarding rule chain" -j forwarding_rule
[353:90152] -A FORWARD -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
[11:660] -A FORWARD -i br-lan -m comment --comment "!fw3" -j zone_lan_forward
[0:0] -A FORWARD -i eth0.2 -m comment --comment "!fw3" -j zone_wan_forward
[0:0] -A FORWARD -i wlan1-1 -m comment --comment "!fw3" -j zone_guest_forward
[0:0] -A FORWARD -i eth0.30 -m comment --comment "!fw3" -j zone_isolated_4_forward
[0:0] -A FORWARD -m comment --comment "!fw3" -j reject
[46:4781] -A OUTPUT -o lo -m comment --comment "!fw3" -j ACCEPT
[1912:474065] -A OUTPUT -m comment --comment "!fw3: Custom output rule chain" -j output_rule
[1801:466381] -A OUTPUT -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
[4:1037] -A OUTPUT -o br-lan -m comment --comment "!fw3" -j zone_lan_output
[107:6647] -A OUTPUT -o eth0.2 -m comment --comment "!fw3" -j zone_wan_output
[0:0] -A OUTPUT -o wlan1-1 -m comment --comment "!fw3" -j zone_guest_output
[0:0] -A OUTPUT -o eth0.30 -m comment --comment "!fw3" -j zone_isolated_4_output
[68:6605] -A reject -p tcp -m comment --comment "!fw3" -j REJECT --reject-with tcp-reset
[28:4708] -A reject -m comment --comment "!fw3" -j REJECT --reject-with icmp-port-unreachable
[40:2072] -A syn_flood -p tcp -m tcp --tcp-flags FIN,SYN,RST,ACK SYN -m limit --limit 25/sec --limit-burst 50 -m comment --comment "!fw3" -j RETURN
[0:0] -A syn_flood -m comment --comment "!fw3" -j DROP
[0:0] -A zone_guest_dest_ACCEPT -o wlan1-1 -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_guest_dest_REJECT -o wlan1-1 -m comment --comment "!fw3" -j reject
[0:0] -A zone_guest_forward -m comment --comment "!fw3: Custom guest forwarding rule chain" -j forwarding_guest_rule
[0:0] -A zone_guest_forward -m comment --comment "!fw3: Zone guest to wan forwarding policy" -j zone_wan_dest_ACCEPT
[0:0] -A zone_guest_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[0:0] -A zone_guest_forward -m comment --comment "!fw3" -j zone_guest_dest_REJECT
[0:0] -A zone_guest_input -m comment --comment "!fw3: Custom guest input rule chain" -j input_guest_rule
[0:0] -A zone_guest_input -p tcp -m tcp --dport 53 -m comment --comment "!fw3: Guest DNS" -j ACCEPT
[0:0] -A zone_guest_input -p udp -m udp --dport 53 -m comment --comment "!fw3: Guest DNS" -j ACCEPT
[0:0] -A zone_guest_input -p udp -m udp --dport 67:68 -m comment --comment "!fw3: Guest DHCP" -j ACCEPT
[0:0] -A zone_guest_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[0:0] -A zone_guest_input -m comment --comment "!fw3" -j zone_guest_src_REJECT
[0:0] -A zone_guest_output -m comment --comment "!fw3: Custom guest output rule chain" -j output_guest_rule
[0:0] -A zone_guest_output -m comment --comment "!fw3" -j zone_guest_dest_ACCEPT
[0:0] -A zone_guest_src_REJECT -i wlan1-1 -m comment --comment "!fw3" -j reject
[0:0] -A zone_isolated_4_dest_ACCEPT -o eth0.30 -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_isolated_4_dest_REJECT -o eth0.30 -m comment --comment "!fw3" -j reject
[0:0] -A zone_isolated_4_forward -m comment --comment "!fw3: Custom isolated_4 forwarding rule chain" -j forwarding_isolated_4_rule
[0:0] -A zone_isolated_4_forward -m comment --comment "!fw3: Zone isolated_4 to wan forwarding policy" -j zone_wan_dest_ACCEPT
[0:0] -A zone_isolated_4_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[0:0] -A zone_isolated_4_forward -m comment --comment "!fw3" -j zone_isolated_4_dest_REJECT
[0:0] -A zone_isolated_4_input -m comment --comment "!fw3: Custom isolated_4 input rule chain" -j input_isolated_4_rule
[0:0] -A zone_isolated_4_input -p tcp -m tcp --dport 53 -m comment --comment "!fw3: Isolated port 4 DNS" -j ACCEPT
[0:0] -A zone_isolated_4_input -p udp -m udp --dport 53 -m comment --comment "!fw3: Isolated port 4 DNS" -j ACCEPT
[0:0] -A zone_isolated_4_input -p udp -m udp --dport 67:68 -m comment --comment "!fw3: Isolated port 4 DHCP" -j ACCEPT
[0:0] -A zone_isolated_4_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[0:0] -A zone_isolated_4_input -m comment --comment "!fw3" -j zone_isolated_4_src_REJECT
[0:0] -A zone_isolated_4_output -m comment --comment "!fw3: Custom isolated_4 output rule chain" -j output_isolated_4_rule
[0:0] -A zone_isolated_4_output -m comment --comment "!fw3" -j zone_isolated_4_dest_ACCEPT
[0:0] -A zone_isolated_4_src_REJECT -i eth0.30 -m comment --comment "!fw3" -j reject
[4:1037] -A zone_lan_dest_ACCEPT -o br-lan -m comment --comment "!fw3" -j ACCEPT
[11:660] -A zone_lan_forward -m comment --comment "!fw3: Custom lan forwarding rule chain" -j forwarding_lan_rule
[11:660] -A zone_lan_forward -m comment --comment "!fw3: Zone lan to wan forwarding policy" -j zone_wan_dest_ACCEPT
[0:0] -A zone_lan_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[0:0] -A zone_lan_forward -m comment --comment "!fw3" -j zone_lan_dest_ACCEPT
[85:6179] -A zone_lan_input -m comment --comment "!fw3: Custom lan input rule chain" -j input_lan_rule
[0:0] -A zone_lan_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[85:6179] -A zone_lan_input -m comment --comment "!fw3" -j zone_lan_src_ACCEPT
[4:1037] -A zone_lan_output -m comment --comment "!fw3: Custom lan output rule chain" -j output_lan_rule
[4:1037] -A zone_lan_output -m comment --comment "!fw3" -j zone_lan_dest_ACCEPT
[85:6179] -A zone_lan_src_ACCEPT -i br-lan -m conntrack --ctstate NEW,UNTRACKED -m comment --comment "!fw3" -j ACCEPT
[34:1360] -A zone_wan_dest_ACCEPT -o eth0.2 -m conntrack --ctstate INVALID -m comment --comment "!fw3: Prevent NAT leakage" -j DROP
[84:5947] -A zone_wan_dest_ACCEPT -o eth0.2 -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_wan_dest_REJECT -o eth0.2 -m comment --comment "!fw3" -j reject
[0:0] -A zone_wan_forward -m comment --comment "!fw3: Custom wan forwarding rule chain" -j forwarding_wan_rule
[0:0] -A zone_wan_forward -p esp -m comment --comment "!fw3: Allow-IPSec-ESP" -j zone_lan_dest_ACCEPT
[0:0] -A zone_wan_forward -p udp -m udp --dport 500 -m comment --comment "!fw3: Allow-ISAKMP" -j zone_lan_dest_ACCEPT
[0:0] -A zone_wan_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[0:0] -A zone_wan_forward -m comment --comment "!fw3" -j zone_wan_dest_REJECT
[96:11313] -A zone_wan_input -m comment --comment "!fw3: Custom wan input rule chain" -j input_wan_rule
[0:0] -A zone_wan_input -p udp -m udp --dport 68 -m comment --comment "!fw3: Allow-DHCP-Renew" -j ACCEPT
[0:0] -A zone_wan_input -p igmp -m comment --comment "!fw3: Allow-IGMP" -j ACCEPT
[0:0] -A zone_wan_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[96:11313] -A zone_wan_input -m comment --comment "!fw3" -j zone_wan_src_REJECT
[107:6647] -A zone_wan_output -m comment --comment "!fw3: Custom wan output rule chain" -j output_wan_rule
[107:6647] -A zone_wan_output -m comment --comment "!fw3" -j zone_wan_dest_ACCEPT
[96:11313] -A zone_wan_src_REJECT -i eth0.2 -m comment --comment "!fw3" -j reject
COMMIT
# Completed on Sat May 23
Not sure if ip -s link provided the expected output because it also printed the options information so I'm providing ip link too (without the -s option).
root@OpenWrt:~# ip link; ip -s link; ip -4 addr; ip -4 ro li tab all; ip -4 ru
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP qlen 1000
link/ether xyz:xyz:xyz:xyz:xyz:xyz brd ff:ff:ff:ff:ff:ff
3: eth1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP qlen 1000
link/ether xyz:xyz:xyz:xyz:xyz:xyz brd ff:ff:ff:ff:ff:ff
7: br-lan: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP qlen 1000
link/ether xyz:xyz:xyz:xyz:xyz:xyz brd ff:ff:ff:ff:ff:ff
8: eth1.1@eth1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue master br-lan state UP qlen 1000
link/ether xyz:xyz:xyz:xyz:xyz:xyz brd ff:ff:ff:ff:ff:ff
9: eth0.30@eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP qlen 1000
link/ether xyz:xyz:xyz:xyz:xyz:xyz brd ff:ff:ff:ff:ff:ff
10: eth0.2@eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP qlen 1000
link/ether xyz:xyz:xyz:xyz:xyz:xyz brd ff:ff:ff:ff:ff:ff
11: wlan1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue master br-lan state UP qlen 1000
link/ether xyz:xyz:xyz:xyz:xyz:xyz brd ff:ff:ff:ff:ff:ff
12: wlan0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue master br-lan state UP qlen 1000
link/ether xyz:xyz:xyz:xyz:xyz:xyz brd ff:ff:ff:ff:ff:ff
13: wlan1-1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP qlen 1000
link/ether xyz:xyz:xyz:xyz:xyz:xyz brd ff:ff:ff:ff:ff:ff
BusyBox v1.30.1 () multi-call binary.
Usage: ip [OPTIONS] address|route|link|neigh|rule [ARGS]
OPTIONS := -f[amily] inet|inet6|link | -o[neline]
ip addr add|del IFADDR dev IFACE | show|flush [dev IFACE] [to PREFIX]
ip route list|flush|add|del|change|append|replace|test ROUTE
ip link set IFACE [up|down] [arp on|off] [multicast on|off]
[promisc on|off] [mtu NUM] [name NAME] [qlen NUM] [address MAC]
[master IFACE | nomaster]
ip neigh show|flush [to PREFIX] [dev DEV] [nud STATE]
ip rule [list] | add|del SELECTOR ACTION
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1000
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
7: br-lan: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP qlen 1000
inet 192.168.1.1/24 brd 192.168.1.255 scope global br-lan
valid_lft forever preferred_lft forever
9: eth0.30@eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP qlen 1000
inet 192.168.200.1/24 brd 192.168.200.255 scope global eth0.30
valid_lft forever preferred_lft forever
10: eth0.2@eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP qlen 1000
inet xyz.xyz.xyz.xyz/24 brd xyz.xyz.xyz.xyz scope global eth0.2
valid_lft forever preferred_lft forever
13: wlan1-1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP qlen 1000
inet 192.168.100.1/24 brd 192.168.100.255 scope global wlan1-1
valid_lft forever preferred_lft forever
default via xyz.xyz.xyz.xyz dev eth0.2 src xyz.xyz.xyz.xyz
xyz.xyz.xyz.xyz/24 dev eth0.2 scope link src xyz.xyz.xyz.xyz
192.168.1.0/24 dev br-lan scope link src 192.168.1.1
192.168.100.0/24 dev wlan1-1 scope link src 192.168.100.1
192.168.200.0/24 dev eth0.30 scope link src 192.168.200.1
broadcast xyz.xyz.xyz.xyz dev eth0.2 table local scope link src xyz.xyz.xyz.xyz
local xyz.xyz.xyz.xyz dev eth0.2 table local scope host src xyz.xyz.xyz.xyz
broadcast xyz.xyz.xyz.xyz dev eth0.2 table local scope link src xyz.xyz.xyz.xyz
broadcast 127.0.0.0 dev lo table local scope link src 127.0.0.1
local 127.0.0.0/8 dev lo table local scope host src 127.0.0.1
local 127.0.0.1 dev lo table local scope host src 127.0.0.1
broadcast 127.255.255.255 dev lo table local scope link src 127.0.0.1
broadcast 192.168.1.0 dev br-lan table local scope link src 192.168.1.1
local 192.168.1.1 dev br-lan table local scope host src 192.168.1.1
broadcast 192.168.1.255 dev br-lan table local scope link src 192.168.1.1
broadcast 192.168.100.0 dev wlan1-1 table local scope link src 192.168.100.1
local 192.168.100.1 dev wlan1-1 table local scope host src 192.168.100.1
broadcast 192.168.100.255 dev wlan1-1 table local scope link src 192.168.100.1
broadcast 192.168.200.0 dev eth0.30 table local scope link src 192.168.200.1
local 192.168.200.1 dev eth0.30 table local scope host src 192.168.200.1
broadcast 192.168.200.255 dev eth0.30 table local scope link src 192.168.200.1
0: from all lookup local
32766: from all lookup main
32767: from all lookup default
root@OpenWrt:~# swconfig dev switch0 show
Global attributes:
enable_vlan: 1
ar8xxx_mib_poll_interval: 0
ar8xxx_mib_type: 0
enable_mirror_rx: 0
enable_mirror_tx: 0
mirror_monitor_port: 0
mirror_source_port: 0
arl_age_time: 300
arl_table: address resolution table
Port 0: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 0: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 1: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 5: MAC xyz:xyz:xyz:xyz:xyz:xyz
Port 6: MAC xyz:xyz:xyz:xyz:xyz:xyz
igmp_snooping: 0
igmp_v3: 0
Port 0:
mib: ???
enable_eee: ???
igmp_snooping: 0
vlan_prio: 0
pvid: 0
link: port:0 link:up speed:1000baseT full-duplex txflow rxflow
Port 1:
mib: ???
enable_eee: 0
igmp_snooping: 0
vlan_prio: 0
pvid: 2
link: port:1 link:up speed:1000baseT full-duplex txflow rxflow eee100 eee1000 auto
Port 2:
mib: ???
enable_eee: 0
igmp_snooping: 0
vlan_prio: 0
pvid: 1
link: port:2 link:down
Port 3:
mib: ???
enable_eee: 0
igmp_snooping: 0
vlan_prio: 0
pvid: 1
link: port:3 link:down
Port 4:
mib: ???
enable_eee: 0
igmp_snooping: 0
vlan_prio: 0
pvid: 1
link: port:4 link:down
Port 5:
mib: ???
enable_eee: 0
igmp_snooping: 0
vlan_prio: 0
pvid: 3
link: port:5 link:up speed:100baseT full-duplex txflow rxflow eee100 auto
Port 6:
mib: ???
enable_eee: ???
igmp_snooping: 0
vlan_prio: 0
pvid: 0
link: port:6 link:up speed:1000baseT full-duplex txflow rxflow
VLAN 1:
vid: 1
ports: 0t 2 3 4
VLAN 2:
vid: 2
ports: 1 6t
VLAN 3:
vid: 30
ports: 0t 5