I recently got a Raspberry Pi after learning so much about Linux through implementing OpenWRT projects throughout this pandemic. I don't know if I have ever enjoyed anything this much, thank you OpenWRT!
Anyways, I've managed to migrate most of my projects I had on my WRT32x [OpenWRT firmware] to my Raspberry Pi 4. However one program in particular, Wireguard, is giving me a headache and I can't figure out why the hell its not port forwarding -- even though I know I'm port forwarding correctly because I have successfully forwarded 9091 for Transmission-web off of the pi and it works. However, I continue to get a "Connection refused" when testing my Wireguard port [default wg0 port 51820] on https://canyouseeme.org/ .
I used the PiVPN install script for Raspberry Pi, which seemed to install it with no errors:
curl -L https://install.pivpn.io | bash
I believe I know what the issue is, but I don't know how to make the change. When I was trying to get Flood (a Torrent npm linux program) to port forward on the pi, I noticed that if it was running on [0.0.0.0:3000], it could not be seen from my LAN network or the outside. For it to work, I found it needed to be ran on the LAN interface which is [10.1.1.155:3000] -- I have never encountered something like this, but that is what fixed it. I believe I should be doing the same for Wireguard, how would I modify the server to start on [10.1.1.155:51820] vs the current [0.0.0.0:51820]?
I set a static DHCP address on my pi and my PiVPN debug shows it (see below), but when I run netstat it is running on [0.0.0.0:51820].
What am I doing wrong? Am I correct about the LAN interface it should be running on? If so, how do I change it so Wireguard server starts on LAN interface [10.1.1.155] and not [0.0.0.0]? I have searched the internet for a solid 24 hours now -- I wanted to fix this myself lol. Any help is appreciated.
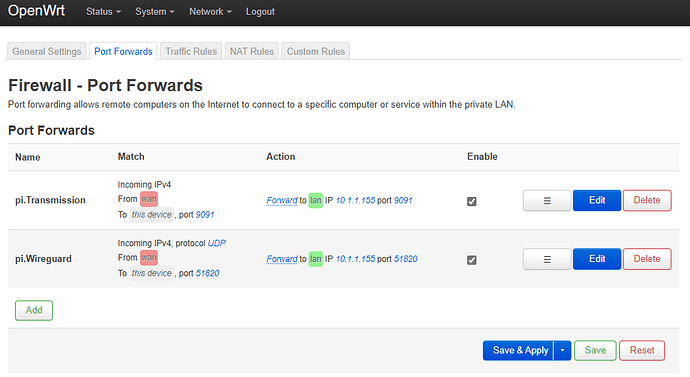
OpenWRT LuCI > Firewall > Port Forward:
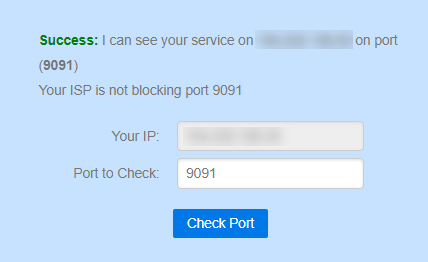
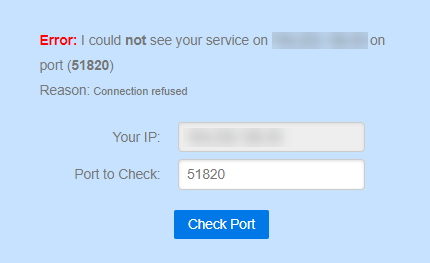
https://canyouseeme.org results:
Transmission (Success):
Wireguard (Fail):
Netstat results (editted by reducing amount of active connections):
pi@raspberrypi:~ $ netstat -l
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State
tcp 0 0 0.0.0.0:9091 0.0.0.0:* LISTEN
>udp 0 0 0.0.0.0:51820 0.0.0.0:*<
udp 0 0 0.0.0.0:ipp 0.0.0.0:*
udp 0 0 10.1.1.255:netbios-ns 0.0.0.0:*
udp 0 0 raspberrypi.:netbios-ns 0.0.0.0:*
udp 0 0 0.0.0.0:netbios-ns 0.0.0.0:*
udp 0 0 10.1.1.255:netbios-dgm 0.0.0.0:*
udp 0 0 raspberrypi:netbios-dgm 0.0.0.0:*
udp 0 0 0.0.0.0:netbios-dgm 0.0.0.0:*
udp 0 0 0.0.0.0:32410 0.0.0.0:*
udp 0 0 0.0.0.0:32412 0.0.0.0:*
udp 0 0 0.0.0.0:32413 0.0.0.0:*
udp 0 0 0.0.0.0:32414 0.0.0.0:*
udp 0 0 0.0.0.0:31413 0.0.0.0:*
udp 0 0 raspberrypi.lan:39656 0.0.0.0:*
udp 0 0 0.0.0.0:mdns 0.0.0.0:*
udp 0 0 raspberrypi.lan:39160 0.0.0.0:*
udp 0 0 raspberrypi.lan:46431 0.0.0.0:*
udp 0 0 239.255.255.250:1900 0.0.0.0:*
udp 0 0 0.0.0.0:1901 0.0.0.0:*
udp 0 0 raspberrypi.lan:57741 0.0.0.0:*
udp 0 0 0.0.0.0:40368 0.0.0.0:*
udp 0 0 localhost:60353 0.0.0.0:*
udp 0 0 localhost:44531 0.0.0.0:*
udp 0 0 10.6.0.1:53244 0.0.0.0:*
udp6 0 0 [::]:35867 [::]:*
udp6 0 0 [::]:dhcpv6-client [::]:*
>udp6 0 0 [::]:51820 [::]:*<
udp6 0 0 [::]:mdns [::]:*
udp6 0 0 [::]:59234 [::]:*
raw6 0 0 [::]:ipv6-icmp [::]:*
Here is my PiVPN debug:
pi@raspberrypi:~ $ pivpn -d
::: Generating Debug Output
:::: PiVPN debug ::::
=============================================
:::: Latest commit ::::
commit d7771c251418fa443869397d46f93c5b0c197558
Author: 4s3ti <4s3ti@protonmail.com>
Date: Sat Feb 6 23:04:11 2021 +0100
Merge branch test into master
fixes #1234
ci/cd fixes and improvements
=============================================
:::: Installation settings ::::
PLAT=Raspbian
OSCN=buster
USING_UFW=0
IPv4dev=eth0
dhcpReserv=1
IPv4addr=10.1.1.155/24
IPv4gw=10.1.1.1
install_user=pi
install_home=/home/pi
VPN=wireguard
pivpnPORT=51820
pivpnDNS1=9.9.9.9
pivpnDNS2=149.112.112.112
pivpnHOST=REDACTED
INPUT_CHAIN_EDITED=0
FORWARD_CHAIN_EDITED=0
pivpnPROTO=udp
pivpnDEV=wg0
pivpnNET=10.6.0.0
subnetClass=24
ALLOWED_IPS="0.0.0.0/0, ::0/0"
UNATTUPG=1
INSTALLED_PACKAGES=(dnsutils iptables-persistent wireguard-tools wireguard-dkms qrencode unattended-upgrades)
=============================================
:::: Server configuration shown below ::::
[Interface]
PrivateKey = server_priv
Address = 10.6.0.1/24
ListenPort = 51820
=============================================
:::: Client configuration shown below ::::
::: There are no clients yet
=============================================
:::: Recursive list of files in ::::
:::: /etc/wireguard shown below ::::
/etc/wireguard:
configs
keys
wg0.conf
/etc/wireguard/configs:
clients.txt
/etc/wireguard/keys:
server_priv
server_pub
=============================================
:::: Self check ::::
:: [OK] IP forwarding is enabled
:: [OK] Iptables MASQUERADE rule set
:: [OK] WireGuard is running
:: [OK] WireGuard is enabled (it will automatically start on reboot)
:: [OK] WireGuard is listening on port 51820/udp
=============================================
:::: Having trouble connecting? Take a look at the FAQ:
:::: https://github.com/pivpn/pivpn/wiki/FAQ
=============================================
:::: WARNING: This script should have automatically masked sensitive ::::
:::: information, however, still make sure that PrivateKey, PublicKey ::::
:::: and PresharedKey are masked before reporting an issue. An example key ::::
:::: that you should NOT see in this log looks like this: ::::
:::: YIAoJVsdIeyvXfGGDDadHh6AxsMRymZTnnzZoAb9cxRe ::::
=============================================
:::: Debug complete ::::
:::
::: Debug output completed above.
::: Copy saved to /tmp/debug.log
:::