Hi,
My network setup is like this:
- Main router: Ubiquiti EdgeRouter X (provide DHCP, VLan, etc...)
- Use it as AP: TP-Link Archer C2600
(flashed to LuCI openwrt-19.07 branch (git-20.136.49537-fb2f363) / OpenWrt 19.07.3 r11063-85e04e9f46)
My goal is to:
- Main Secure Network for all my PC and laptops on VLAN1(default) on 192.168.111.x
- IOT Network for all smart devices on VLAN115 on 192.168.115.x
- Guest Network on VLAN116 on 192.168.116.x
- have some some traffic forward to allow Main Secure Network to recognize Chromecast and Smart Switches on the IOT Network, like mDNS
What I have done so far:
- I created VLAN115 on EdgeRouter
I followed this post:
https://xdeb.org/post/2020/02/28/unifi-edgerouter-guest-iot-vlan/
IOT switch0.115 vlan on 192.168.115.x
DNS Forwarding: Interface
switch0
switch0.115
mDNS repeater configuration
switch0
switch0.115
I haven't set up VLAN116 for Guest yet. I can use VLAN115 for testing both IOT and Guest Network for now.
- I unchecked this on OpenWRT
Authoritative
This is the only DHCP in the local network
-
I deleted WAN and WAN6 interfaces which came default
-
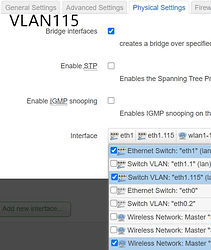
I created Interface WIFI_IOT
Protocol DHCP client
but with no its own DHCP capability
- I created two SSIDs under 11bgn radio for testing.
- IOT (Network: lan, wifi_iot)
- Guest (lan)
I did these two differently so that I can test which one works.
Both SSIDs work now and can connect to the internet, but get 192.168.111.x IPs.
The problem that I have
- I don't know how to make devices connected to SSID-IOT automatically get VLAN115 and being assigned 192.168.115.x by the DHCP on my main EdgeRouter.
- After getting VLAN working, what firewall rule should I create? on EdgeRouter or on OpenWRT?
Attached some config files that I found under /etc/config
DHCP config
config dnsmasq
option domainneeded '1'
option localise_queries '1'
option rebind_protection '1'
option rebind_localhost '1'
option local '/lan/'
option domain 'lan'
option expandhosts '1'
option readethers '1'
option leasefile '/tmp/dhcp.leases'
option resolvfile '/tmp/resolv.conf.auto'
option localservice '1'
option enable_tftp '1'
config dhcp 'lan'
option interface 'lan'
option dhcpv6 'server'
option ra 'server'
option ra_management '1'
option ignore '1'
config dhcp 'wan'
option interface 'wan'
option ignore '1'
config odhcpd 'odhcpd'
option maindhcp '0'
option leasefile '/tmp/hosts/odhcpd'
option leasetrigger '/usr/sbin/odhcpd-update'
option loglevel '4'
Network Config
config interface 'loopback'
option ifname 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'XXX::/48'
config interface 'lan'
option type 'bridge'
option ifname 'eth1.1'
option proto 'static'
option netmask '255.255.255.0'
option ip6assign '60'
option gateway '192.168.111.1'
option ipaddr '192.168.111.2'
list dns '192.168.111.1'
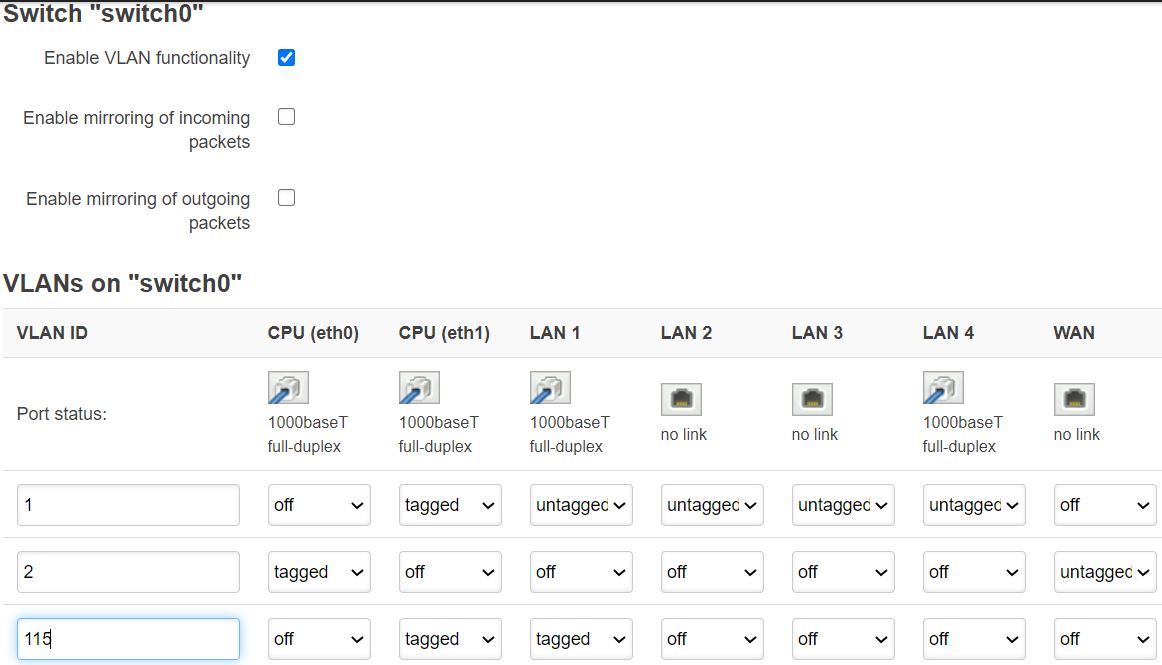
config switch
option name 'switch0'
option reset '1'
option enable_vlan '1'
config switch_vlan
option device 'switch0'
option vlan '1'
option ports '1 2 3 4 6t'
config switch_vlan
option device 'switch0'
option vlan '2'
option ports '5 0t'
config interface 'wifi_iot'
option type 'bridge'
option proto 'dhcp'
Wireless Config
config wifi-device 'radio0'
option type 'mac80211'
option hwmode '11a'
option path 'XXX'
option htmode 'VHT80'
option channel '149'
config wifi-iface 'default_radio0'
option device 'radio0'
option network 'lan'
option mode 'ap'
option key 'password'
option ssid 'Home-5G'
option hidden '1'
option encryption 'psk2'
option ifname 'wlan5g_0'
config wifi-device 'radio1'
option type 'mac80211'
option channel '11'
option hwmode '11g'
option path 'XXX'
option htmode 'HT20'
config wifi-iface 'default_radio1'
option device 'radio1'
option network 'lan'
option mode 'ap'
option key 'password'
option ssid 'Home'
option hidden '1'
option encryption 'psk2'
option ifname 'wlan2g_0'
config wifi-iface 'wifinet2'
option encryption 'psk2'
option device 'radio1'
option mode 'ap'
option key 'password'
option ssid 'IOT'
option ifname 'wlan2g_1'
option network 'wifi_iot lan'
config wifi-iface 'wifinet3'
option ssid 'Guest'
option encryption 'psk2'
option device 'radio1'
option mode 'ap'
option key 'password'
option network 'lan'