If you run wireshark on the windows machine to capture obs64's egress traffic what does it show?
Is the iptables rule executed at all? Can you check its counters?
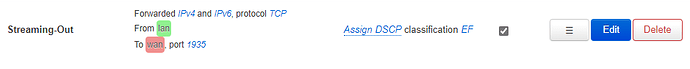
iptables-save | grep dscp does not return anythins, so i'm not totally sure that the Traffic Rule is created:
The full output of iptables-save is:
root@Main-Router:~# iptables-save
# Generated by iptables-save v1.8.3 on Thu Jul 2 10:59:27 2020
*nat
:PREROUTING ACCEPT [5613:874625]
:INPUT ACCEPT [1609:109433]
:OUTPUT ACCEPT [796:53669]
:POSTROUTING ACCEPT [9:1215]
:postrouting_app_rule - [0:0]
:postrouting_lan_rule - [0:0]
:postrouting_rule - [0:0]
:postrouting_vpn_rule - [0:0]
:postrouting_wan_rule - [0:0]
:prerouting_app_rule - [0:0]
:prerouting_lan_rule - [0:0]
:prerouting_rule - [0:0]
:prerouting_vpn_rule - [0:0]
:prerouting_wan_rule - [0:0]
:zone_app_postrouting - [0:0]
:zone_app_prerouting - [0:0]
:zone_lan_postrouting - [0:0]
:zone_lan_prerouting - [0:0]
:zone_vpn_postrouting - [0:0]
:zone_vpn_prerouting - [0:0]
:zone_wan_postrouting - [0:0]
:zone_wan_prerouting - [0:0]
-A PREROUTING -m comment --comment "!fw3: Custom prerouting rule chain" -j prerouting_rule
-A PREROUTING -i br-lan -m comment --comment "!fw3" -j zone_lan_prerouting
-A PREROUTING -i br-app -m comment --comment "!fw3" -j zone_app_prerouting
-A PREROUTING -i eth0.835 -m comment --comment "!fw3" -j zone_wan_prerouting
-A PREROUTING -i tun0 -m comment --comment "!fw3" -j zone_vpn_prerouting
-A POSTROUTING -m comment --comment "!fw3: Custom postrouting rule chain" -j postrouting_rule
-A POSTROUTING -o br-lan -m comment --comment "!fw3" -j zone_lan_postrouting
-A POSTROUTING -o br-app -m comment --comment "!fw3" -j zone_app_postrouting
-A POSTROUTING -o eth0.835 -m comment --comment "!fw3" -j zone_wan_postrouting
-A POSTROUTING -o tun0 -m comment --comment "!fw3" -j zone_vpn_postrouting
-A zone_app_postrouting -m comment --comment "!fw3: Custom app postrouting rule chain" -j postrouting_app_rule
-A zone_app_prerouting -m comment --comment "!fw3: Custom app prerouting rule chain" -j prerouting_app_rule
-A zone_lan_postrouting -m comment --comment "!fw3: Custom lan postrouting rule chain" -j postrouting_lan_rule
-A zone_lan_postrouting -s 192.168.12.0/24 -d 192.168.12.1/32 -p tcp -m tcp --dport 12225 -m comment --comment "!fw3: HomeVPN (reflection)" -j SNAT --to-source 192.168.12.1
-A zone_lan_prerouting -m comment --comment "!fw3: Custom lan prerouting rule chain" -j prerouting_lan_rule
-A zone_lan_prerouting -s 192.168.12.0/24 -d 192.168.10.2/32 -p tcp -m tcp --dport 12225 -m comment --comment "!fw3: HomeVPN (reflection)" -j DNAT --to-destination 192.168.12.1:12225
-A zone_vpn_postrouting -m comment --comment "!fw3: Custom vpn postrouting rule chain" -j postrouting_vpn_rule
-A zone_vpn_postrouting -m comment --comment "!fw3" -j MASQUERADE
-A zone_vpn_prerouting -m comment --comment "!fw3: Custom vpn prerouting rule chain" -j prerouting_vpn_rule
-A zone_wan_postrouting -m comment --comment "!fw3: Custom wan postrouting rule chain" -j postrouting_wan_rule
-A zone_wan_postrouting -m comment --comment "!fw3" -j MASQUERADE
-A zone_wan_prerouting -m comment --comment "!fw3: Custom wan prerouting rule chain" -j prerouting_wan_rule
-A zone_wan_prerouting -p tcp -m tcp --dport 12225 -m comment --comment "!fw3: HomeVPN" -j DNAT --to-destination 192.168.12.1:12225
COMMIT
# Completed on Thu Jul 2 10:59:27 2020
# Generated by iptables-save v1.8.3 on Thu Jul 2 10:59:27 2020
*raw
:PREROUTING ACCEPT [141974:103002838]
:OUTPUT ACCEPT [5425:1134825]
:zone_app_helper - [0:0]
:zone_lan_helper - [0:0]
-A PREROUTING -i br-lan -m comment --comment "!fw3: lan CT helper assignment" -j zone_lan_helper
-A PREROUTING -i br-app -m comment --comment "!fw3: app CT helper assignment" -j zone_app_helper
COMMIT
# Completed on Thu Jul 2 10:59:27 2020
# Generated by iptables-save v1.8.3 on Thu Jul 2 10:59:27 2020
*mangle
:PREROUTING ACCEPT [141981:103003118]
:INPUT ACCEPT [6061:545676]
:FORWARD ACCEPT [133546:101998069]
:OUTPUT ACCEPT [5436:1136721]
:POSTROUTING ACCEPT [138626:103119326]
-A FORWARD -o eth0.835 -p tcp -m tcp --tcp-flags SYN,RST SYN -m comment --comment "!fw3: Zone wan MTU fixing" -j TCPMSS --clamp-mss-to-pmtu
-A FORWARD -o tun0 -p tcp -m tcp --tcp-flags SYN,RST SYN -m comment --comment "!fw3: Zone vpn MTU fixing" -j TCPMSS --clamp-mss-to-pmtu
COMMIT
# Completed on Thu Jul 2 10:59:27 2020
# Generated by iptables-save v1.8.3 on Thu Jul 2 10:59:27 2020
*filter
:INPUT ACCEPT [1:40]
:FORWARD DROP [0:0]
:OUTPUT ACCEPT [0:0]
:forwarding_app_rule - [0:0]
:forwarding_lan_rule - [0:0]
:forwarding_rule - [0:0]
:forwarding_vpn_rule - [0:0]
:forwarding_wan_rule - [0:0]
:input_app_rule - [0:0]
:input_lan_rule - [0:0]
:input_rule - [0:0]
:input_vpn_rule - [0:0]
:input_wan_rule - [0:0]
:output_app_rule - [0:0]
:output_lan_rule - [0:0]
:output_rule - [0:0]
:output_vpn_rule - [0:0]
:output_wan_rule - [0:0]
:reject - [0:0]
:syn_flood - [0:0]
:zone_app_dest_ACCEPT - [0:0]
:zone_app_dest_REJECT - [0:0]
:zone_app_forward - [0:0]
:zone_app_input - [0:0]
:zone_app_output - [0:0]
:zone_app_src_ACCEPT - [0:0]
:zone_lan_dest_ACCEPT - [0:0]
:zone_lan_dest_REJECT - [0:0]
:zone_lan_forward - [0:0]
:zone_lan_input - [0:0]
:zone_lan_output - [0:0]
:zone_lan_src_ACCEPT - [0:0]
:zone_vpn_dest_ACCEPT - [0:0]
:zone_vpn_dest_REJECT - [0:0]
:zone_vpn_forward - [0:0]
:zone_vpn_input - [0:0]
:zone_vpn_output - [0:0]
:zone_vpn_src_REJECT - [0:0]
:zone_wan_dest_ACCEPT - [0:0]
:zone_wan_dest_REJECT - [0:0]
:zone_wan_forward - [0:0]
:zone_wan_input - [0:0]
:zone_wan_output - [0:0]
:zone_wan_src_REJECT - [0:0]
-A INPUT -i lo -m comment --comment "!fw3" -j ACCEPT
-A INPUT -m comment --comment "!fw3: Custom input rule chain" -j input_rule
-A INPUT -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
-A INPUT -p tcp -m tcp --tcp-flags FIN,SYN,RST,ACK SYN -m comment --comment "!fw3" -j syn_flood
-A INPUT -i br-lan -m comment --comment "!fw3" -j zone_lan_input
-A INPUT -i br-app -m comment --comment "!fw3" -j zone_app_input
-A INPUT -i eth0.835 -m comment --comment "!fw3" -j zone_wan_input
-A INPUT -i tun0 -m comment --comment "!fw3" -j zone_vpn_input
-A FORWARD -m comment --comment "!fw3: Custom forwarding rule chain" -j forwarding_rule
-A FORWARD -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
-A FORWARD -i br-lan -m comment --comment "!fw3" -j zone_lan_forward
-A FORWARD -i br-app -m comment --comment "!fw3" -j zone_app_forward
-A FORWARD -i eth0.835 -m comment --comment "!fw3" -j zone_wan_forward
-A FORWARD -i tun0 -m comment --comment "!fw3" -j zone_vpn_forward
-A FORWARD -m comment --comment "!fw3" -j reject
-A OUTPUT -o lo -m comment --comment "!fw3" -j ACCEPT
-A OUTPUT -m comment --comment "!fw3: Custom output rule chain" -j output_rule
-A OUTPUT -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
-A OUTPUT -o br-lan -m comment --comment "!fw3" -j zone_lan_output
-A OUTPUT -o br-app -m comment --comment "!fw3" -j zone_app_output
-A OUTPUT -o eth0.835 -m comment --comment "!fw3" -j zone_wan_output
-A OUTPUT -o tun0 -m comment --comment "!fw3" -j zone_vpn_output
-A reject -p tcp -m comment --comment "!fw3" -j REJECT --reject-with tcp-reset
-A reject -m comment --comment "!fw3" -j REJECT --reject-with icmp-port-unreachable
-A syn_flood -p tcp -m tcp --tcp-flags FIN,SYN,RST,ACK SYN -m limit --limit 25/sec --limit-burst 50 -m comment --comment "!fw3" -j RETURN
-A syn_flood -m comment --comment "!fw3" -j DROP
-A zone_app_dest_ACCEPT -o br-app -m comment --comment "!fw3" -j ACCEPT
-A zone_app_dest_REJECT -o br-app -m comment --comment "!fw3" -j reject
-A zone_app_forward -m comment --comment "!fw3: Custom app forwarding rule chain" -j forwarding_app_rule
-A zone_app_forward -m comment --comment "!fw3: Zone app to wan forwarding policy" -j zone_wan_dest_ACCEPT
-A zone_app_forward -m comment --comment "!fw3: Zone app to vpn forwarding policy" -j zone_vpn_dest_ACCEPT
-A zone_app_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
-A zone_app_forward -m comment --comment "!fw3" -j zone_app_dest_REJECT
-A zone_app_input -m comment --comment "!fw3: Custom app input rule chain" -j input_app_rule
-A zone_app_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
-A zone_app_input -m comment --comment "!fw3" -j zone_app_src_ACCEPT
-A zone_app_output -m comment --comment "!fw3: Custom app output rule chain" -j output_app_rule
-A zone_app_output -m comment --comment "!fw3" -j zone_app_dest_ACCEPT
-A zone_app_src_ACCEPT -i br-app -m conntrack --ctstate NEW,UNTRACKED -m comment --comment "!fw3" -j ACCEPT
-A zone_lan_dest_ACCEPT -o br-lan -m comment --comment "!fw3" -j ACCEPT
-A zone_lan_dest_REJECT -o br-lan -m comment --comment "!fw3" -j reject
-A zone_lan_forward -m comment --comment "!fw3: Custom lan forwarding rule chain" -j forwarding_lan_rule
-A zone_lan_forward -m comment --comment "!fw3: Zone lan to wan forwarding policy" -j zone_wan_dest_ACCEPT
-A zone_lan_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
-A zone_lan_forward -m comment --comment "!fw3" -j zone_lan_dest_REJECT
-A zone_lan_input -m comment --comment "!fw3: Custom lan input rule chain" -j input_lan_rule
-A zone_lan_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
-A zone_lan_input -m comment --comment "!fw3" -j zone_lan_src_ACCEPT
-A zone_lan_output -m comment --comment "!fw3: Custom lan output rule chain" -j output_lan_rule
-A zone_lan_output -m comment --comment "!fw3" -j zone_lan_dest_ACCEPT
-A zone_lan_src_ACCEPT -i br-lan -m conntrack --ctstate NEW,UNTRACKED -m comment --comment "!fw3" -j ACCEPT
-A zone_vpn_dest_ACCEPT -o tun0 -m conntrack --ctstate INVALID -m comment --comment "!fw3: Prevent NAT leakage" -j DROP
-A zone_vpn_dest_ACCEPT -o tun0 -m comment --comment "!fw3" -j ACCEPT
-A zone_vpn_dest_REJECT -o tun0 -m comment --comment "!fw3" -j reject
-A zone_vpn_forward -m comment --comment "!fw3: Custom vpn forwarding rule chain" -j forwarding_vpn_rule
-A zone_vpn_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
-A zone_vpn_forward -m comment --comment "!fw3" -j zone_vpn_dest_REJECT
-A zone_vpn_input -m comment --comment "!fw3: Custom vpn input rule chain" -j input_vpn_rule
-A zone_vpn_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
-A zone_vpn_input -m comment --comment "!fw3" -j zone_vpn_src_REJECT
-A zone_vpn_output -m comment --comment "!fw3: Custom vpn output rule chain" -j output_vpn_rule
-A zone_vpn_output -m comment --comment "!fw3" -j zone_vpn_dest_ACCEPT
-A zone_vpn_src_REJECT -i tun0 -m comment --comment "!fw3" -j reject
-A zone_wan_dest_ACCEPT -o eth0.835 -m conntrack --ctstate INVALID -m comment --comment "!fw3: Prevent NAT leakage" -j DROP
-A zone_wan_dest_ACCEPT -o eth0.835 -m comment --comment "!fw3" -j ACCEPT
-A zone_wan_dest_REJECT -o eth0.835 -m comment --comment "!fw3" -j reject
-A zone_wan_forward -m comment --comment "!fw3: Custom wan forwarding rule chain" -j forwarding_wan_rule
-A zone_wan_forward -p esp -m comment --comment "!fw3: Allow-IPSec-ESP" -j zone_lan_dest_ACCEPT
-A zone_wan_forward -p udp -m udp --dport 500 -m comment --comment "!fw3: Allow-ISAKMP" -j zone_lan_dest_ACCEPT
-A zone_wan_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
-A zone_wan_forward -m comment --comment "!fw3" -j zone_wan_dest_REJECT
-A zone_wan_input -m comment --comment "!fw3: Custom wan input rule chain" -j input_wan_rule
-A zone_wan_input -p udp -m udp --dport 68 -m comment --comment "!fw3: Allow-DHCP-Renew" -j ACCEPT
-A zone_wan_input -p icmp -m icmp --icmp-type 8 -m limit --limit 5/sec -m comment --comment "!fw3: Allow-Ping" -j ACCEPT
-A zone_wan_input -p igmp -m comment --comment "!fw3: Allow-IGMP" -j ACCEPT
-A zone_wan_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
-A zone_wan_input -m comment --comment "!fw3" -j zone_wan_src_REJECT
-A zone_wan_output -m comment --comment "!fw3: Custom wan output rule chain" -j output_wan_rule
-A zone_wan_output -m comment --comment "!fw3" -j zone_wan_dest_ACCEPT
-A zone_wan_src_REJECT -i eth0.835 -m comment --comment "!fw3" -j reject
COMMIT
# Completed on Thu Jul 2 10:59:27 2020
I'm trying to create a command manually, but not sure how to do that (found different examples online but none of them seems to work)