Rocky
May 29, 2020, 11:59am
1
Hi Forum,
I have an instance of a wiregurad-server running on my OpenWRT. Works fine.
Is there a way to do so ? In LUCI I - guess - only can configure a server-interface
Thanks for your help
krazeh
May 29, 2020, 12:06pm
2
Wireguard is peer to peer, there is no server-client distinction. You add the other wireguard router as a peer and vice versa.
See OpenWrt & Wireguard Site-to-Site - #2 by krazeh for an example.
1 Like
Rocky
May 29, 2020, 12:09pm
3
thanks a lot. I will have a look on it !
Rocky
May 30, 2020, 6:35am
4
So, I tried to configure the StS VPN. Works on the FW itself. But, If I try to reach a host in the connected LAN it doesn't work. Packages are routed to the LAN-Interface of the FW but are not sent the wg-Interface...
Can you copy the output of the following commands from both routers and post it here using the "Preformatted text </> " button:
uci export network; uci export wireless; \
uci export dhcp; uci export firewall; \
head -n -0 /etc/firewall.user; \
ip -4 addr ; ip -4 ro li tab all ; ip -4 ru
Rocky
May 30, 2020, 8:47am
6
Here is the output. wg0 is the "dial-in" wg-interface
krazeh:
root@OpenWrt:~# uci export network; uci export wireless
package network
config interface 'loopback'
option ifname 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fd2c:c6f7:2e1c::/48'
config atm-bridge 'atm'
option vpi '1'
option vci '32'
option encaps 'llc'
option payload 'bridged'
option nameprefix 'dsl'
config dsl 'dsl'
option annex 'b'
option tone 'av'
option ds_snr_offset '0'
config interface 'lan'
option type 'bridge'
option ifname 'eth0'
option proto 'dhcp'
config device 'lan_eth0_dev'
option name 'eth0'
option macaddr '38:10:D5:3A:61:18'
config interface 'wan'
option ifname 'dsl0'
option proto 'static'
option netmask '255.255.255.0'
list dns '172.17.1.11'
option ipaddr '172.17.1.220'
option gateway '172.17.1.1'
config device 'wan_dsl0_dev'
option name 'dsl0'
option macaddr '38:10:D5:3A:61:1C'
config interface 'WLAN'
option ifname 'wlan0'
option proto 'static'
option netmask '255.255.255.0'
option ipaddr '192.168.178.1'
option delegate '0'
option force_link '0'
option type 'bridge'
config interface 'wifi'
option ifname 'WLAN2'
option proto 'static'
option netmask '255.255.255.0'
option ipaddr '192.168.150.1'
list dns '172.17.1.11'
config interface 'wg0'
option proto 'wireguard'
option private_key 'xxx'
option listen_port '51823'
list addresses '10.14.0.1/16'
config wireguard_wg0
option public_key 'xxx='
option description 'iPhone'
list allowed_ips '10.14.0.3/32'
option persistent_keepalive '25'
config interface 'wg1'
option proto 'wireguard'
option private_key 'xxx'
option listen_port '51820'
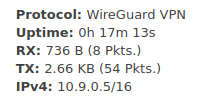
list addresses '10.9.0.5/16'
config wireguard_wg1
option public_key 'xxx'
option description 'Rüdi'
option persistent_keepalive '25'
option endpoint_port '51820'
option route_allowed_ips '1'
option endpoint_host 'xxx.dd-dns.de'
list allowed_ips '192.168.100.0/24'
config wireguard_wg1
list allowed_ips '192.168.100.0/24'
option public_key 'xxx'
config route
option target '192.168.100.0'
option gateway '10.9.0.5'
option netmask '255.255.255.0'
option interface 'lan'
package wireless
config wifi-device 'radio0'
option type 'mac80211'
option channel '11'
option hwmode '11g'
option path 'pci0000:00/0000:00:00.0/0000:01:00.0'
option htmode 'HT20'
option country 'DE'
config wifi-iface 'default_radio0'
option device 'radio0'
option mode 'ap'
option ssid 'OpenWrt'
option key 'xxx'
option encryption 'psk2'
option disabled '1'
config wifi-iface 'wifinet1'
option ssid 'OpenWrt'
option device 'radio0'
option mode 'ap'
option network 'WLAN'
option ifname 'WLAN2'
option key 'xxx'
option encryption 'psk2'
---
uci export dhcp; uci export firewall
package dhcp
config dnsmasq
option localise_queries '1'
option rebind_protection '1'
option rebind_localhost '1'
option local '/lan/'
option domain 'lan'
option expandhosts '1'
option readethers '1'
option leasefile '/tmp/dhcp.leases'
option resolvfile '/tmp/resolv.conf.auto'
option confdir '/tmp/dnsmasq.d'
option localservice '0'
config dhcp 'lan'
option interface 'lan'
option ignore '1'
config dhcp 'wan'
option interface 'wan'
option ignore '1'
config odhcpd 'odhcpd'
option maindhcp '0'
option leasefile '/tmp/hosts/odhcpd'
option leasetrigger '/usr/sbin/odhcpd-update'
option loglevel '4'
config dhcp 'WLAN'
option start '100'
option leasetime '12h'
option limit '150'
option interface 'WLAN'
config dhcp 'wifi'
option start '100'
option leasetime '12h'
option interface 'wifi'
option limit '190'
package firewall
config defaults
option syn_flood '1'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
config zone
option name 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
option network 'lan wg0 wg1'
config include
option path '/etc/firewall.user'
config zone
option input 'ACCEPT'
option name 'WLAN'
option output 'ACCEPT'
option forward 'ACCEPT'
option network 'WLAN wifi'
option log '1'
config forwarding
option dest 'lan'
option src 'WLAN'
config forwarding
option dest 'WLAN'
option src 'lan'
config rule
option src 'WLAN'
option name 'all'
option target 'ACCEPT'
option dest 'lan'
option enabled '0'
config rule
option dest 'WLAN'
option src 'lan'
option name 'all'
option target 'ACCEPT'
---
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
4: br-lan: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
inet 172.17.1.102/24 brd 172.17.1.255 scope global br-lan
valid_lft forever preferred_lft forever
6: wg0: <POINTOPOINT,NOARP,UP,LOWER_UP> mtu 1420 qdisc noqueue state UNKNOWN group default qlen 1000
inet 10.14.0.1/16 brd 10.14.255.255 scope global wg0
valid_lft forever preferred_lft forever
8: WLAN2: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue master br-WLAN state UP group default qlen 1000
inet 192.168.150.1/24 brd 192.168.150.255 scope global WLAN2
valid_lft forever preferred_lft forever
9: br-WLAN: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
inet 192.168.178.1/24 brd 192.168.178.255 scope global br-WLAN
valid_lft forever preferred_lft forever
default via 172.17.1.1 dev br-lan proto static src 172.17.1.102
10.14.0.0/16 dev wg0 proto kernel scope link src 10.14.0.1
91.42.120.148 via 172.17.1.1 dev br-lan proto static
172.17.1.0/24 dev br-lan proto kernel scope link src 172.17.1.102
192.168.150.0/24 dev WLAN2 proto kernel scope link src 192.168.150.1
192.168.178.0/24 dev br-WLAN proto kernel scope link src 192.168.178.1
broadcast 10.14.0.0 dev wg0 table local proto kernel scope link src 10.14.0.1
local 10.14.0.1 dev wg0 table local proto kernel scope host src 10.14.0.1
broadcast 10.14.255.255 dev wg0 table local proto kernel scope link src 10.14.0.1
broadcast 127.0.0.0 dev lo table local proto kernel scope link src 127.0.0.1
local 127.0.0.0/8 dev lo table local proto kernel scope host src 127.0.0.1
local 127.0.0.1 dev lo table local proto kernel scope host src 127.0.0.1
broadcast 127.255.255.255 dev lo table local proto kernel scope link src 127.0.0.1
broadcast 172.17.1.0 dev br-lan table local proto kernel scope link src 172.17.1.102
local 172.17.1.102 dev br-lan table local proto kernel scope host src 172.17.1.102
broadcast 172.17.1.255 dev br-lan table local proto kernel scope link src 172.17.1.102
broadcast 192.168.150.0 dev WLAN2 table local proto kernel scope link src 192.168.150.1
local 192.168.150.1 dev WLAN2 table local proto kernel scope host src 192.168.150.1
broadcast 192.168.150.255 dev WLAN2 table local proto kernel scope link src 192.168.150.1
broadcast 192.168.178.0 dev br-WLAN table local proto kernel scope link src 192.168.178.1
local 192.168.178.1 dev br-WLAN table local proto kernel scope host src 192.168.178.1
broadcast 192.168.178.255 dev br-WLAN table local proto kernel scope link src 192.168.178.1
0: from all lookup local
32766: from all lookup main
32767: from all lookup default
You don't need a second wireguard interface, just add a new peer to the interface you already had set up. I also need to see the output of those commands from the other site.
Can you also detail the setup between each LAN and the internet, I.e. what routers are involved and how they are connected.
Rocky
May 30, 2020, 9:21am
8
Here is the setup:
The OpenWrt (wicht is my test device) Router with the two wg-Interfaces. LAN-Address 172.17.1.102
I set static routs a) on the LAN-WAN OpenWrt and also on the Internetrouter.
A tcp-dump on wg1 shows me that connections from my LAN are routed to wg1, but there is no response from the other side
e.g.:
What's the config on the other end? Is the tunnel connected/exchanging any data at all?
Have you set up two peers on the wg1 interface?
Rocky
May 30, 2020, 9:33am
10
Yes, they are exchanging data. From the console on the wrt-router i can ping devices on the other end
on wg1 only one peer is set up - the one to the wg-server on the other end
krazeh
May 30, 2020, 9:39am
11
Just the Raspi running WG or other devices? What's the config on that end?
Then you shouldn't have
config wireguard_wg1
list allowed_ips '192.168.100.0/24'
option public_key 'xxx'
in your config, delete it and just keep the longer 'config wireguard_wg1' stanza.
Rocky
May 30, 2020, 9:46am
12
On the other site there is the raspi and a view devices (e.g. a webserver).
I deleted the it and just kept the longer one. Restarted the interface, same situation
krazeh
May 30, 2020, 9:52am
13
Which of them can you currently ping?
Yes.
I don't think, it is possible, because UDP is not trackable. However @trendy is not agree.
krazeh
May 30, 2020, 9:54am
15
Sorry, I might have missed something but what is your point?
Rocky
May 30, 2020, 9:56am
16
from the console on the Wrt i can ping any machine on the other side. But none of them from my lan. Only from the Wrt-Router.
Here is the wg0.config from the Pi - Client 4 is the peer that I'm using for the StS VPN:
wg0.conf
[Interface]
Address = 10.9.0.1/24
PrivateKey = xxxM=
ListenPort = 51820
PostUp = sysctl net.ipv4.conf.%i.forwarding=1 net.ipv4.conf.$(sed -n 3p /run/dietpi/.network).forwarding=1
PostUp = sysctl net.ipv6.conf.$(sed -n 3p /run/dietpi/.network).accept_ra=2
PostUp = sysctl net.ipv6.conf.%i.forwarding=1 net.ipv6.conf.$(sed -n 3p /run/dietpi/.network).forwarding=1
PostUp = iptables -A FORWARD -i %i -j ACCEPT; iptables -t nat -A POSTROUTING -o $(sed -n 3p /run/dietpi/.network) -j MASQUERADE
PostUp = ip6tables -A FORWARD -i %i -j ACCEPT; ip6tables -t nat -A POSTROUTING -o $(sed -n 3p /run/dietpi/.network) -j MASQUERADE
PostDown = iptables -D FORWARD -i %i -j ACCEPT; iptables -t nat -D POSTROUTING -o $(sed -n 3p /run/dietpi/.network) -j MASQUERADE
PostDown = ip6tables -D FORWARD -i %i -j ACCEPT; ip6tables -t nat -D POSTROUTING -o $(sed -n 3p /run/dietpi/.network) -j MASQUERADE
# Client 1
[Peer]
PublicKey = xxxo=
AllowedIPs = 10.9.0.2/32
# Client 2
[Peer]
PublicKey = xxx=
AllowedIPs = 10.9.0.3/32
# Client 3
[Peer]
PublicKey = xxx/Xo=
AllowedIPs = 10.9.0.4/32
# Client 4
[Peer]
PublicKey = xxxzXFk=
AllowedIPs = 10.9.0.5/32
trendy
May 30, 2020, 9:57am
17
Don't bother, @ulmwind just enjoys to twist what I say to prove his own theories.
krazeh
May 30, 2020, 10:02am
18
You need to add your LAN subnet to the AllowedIPs. At the moment the only traffic that's allowed in or out at the Raspi end is traffic directly from the OpenWRT router.
Rocky
May 30, 2020, 10:30am
19
you are right. I guess that is the missing pice in the puzzle.