apparent resolution, but have not seen an patch submitted.
I had to google it. If anyone else needs a quick overview of the situation:
- CVE-2022-4304 openSSL
- CVE-2022-4450 openSSL
- CVE-2022-47522 wifi client isolation bypasses
- CVE-2022-47938 ksmbd
- CVE-2022-47939 ksmbd
- CVE-2022-47940 ksmbd
- CVE-2022-47941 ksmbd
- CVE-2022-47942 ksmbd
- CVE-2022-47943 ksmbd
- CVE-2023-0215 openSSL
- CVE-2023-0286 openSSL
The issue that is affecting UBI based MTD devices breaking 22.03.and snapshot release due to the kernel 5.10.x and 5.15.x still has the bug and the dev team should have just applied the emergency roll-back or corrective patch already widely known and confirmed to work over the past month, every expected stable releases is broken now.
And details if anyone wants to dig into it:
Upgraded Netgear WAX202 serving as a WDS client, using attended sysupgrade, from 22.03.3, almost successfully. The only trouble is that the browser never told me that the upgrade is actually successful, it stuck on the "please wait, do not disconnect the power" page.
I don't fully understand, is Linksys E8450 (UBI) safe to upgrade?
Huge Thanks to the devs and community
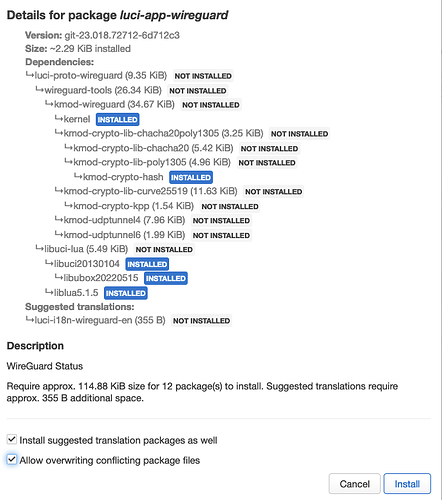
What does this new option?
Allow overwriting conflicting package files
so this release doesn't cover xiaomi ax3600 either ? ![]()
are there any plans to include that device too ?
This is just a maintenance release to the year-old 22.03 branch, not a new full release. There is no ath11k or ipq807x support in 22.03.
Those will be part of the full release, 23.0x.0
That has always been available in opkg as --force-overwrite
Now it is just exposed to LuCI GUI.
It allows overwriting files from other packages (without uninstalling the other package).
useful e.g. when testing alternative WiFi firmware blobs ath10k vs. ath10k-ct, as you can install the other similarly named alternative blob without formally removing the old package.
Just updated another mi 4a gig v1 and successful.
Updated successfully via attended sysupgrade 22.03.3 => 22.03.4 after 95 days uptime:
- EAP615-WALL access point
- RPI4 router
Many thanks to the devs!
I upgraded and all seems fine with my RT3200s.
But it seems like rather a blunder that this service release results in failure on a pretty popular device.
I wonder how this happened and what steps will be taken to help safeguard against this for future service releases?
Was this issue:
not already active at the time the 22.03.4 service release was issued?
Upgraded my Linksys E8540. There was some breakage, but I am not sure if it was due to the upgrade or merely due to the reboot.
- The USB LTE modem (Huawei NCM) did not get IPv6 on the first try.
- The StrongSwan VPN that I use to get a public IP address did not come up correctly (connected but no IP). Fixed with a restart.
- The WireGuard VPN that I use in order to access some specific geo-restricted sites broke. For some reason, there was a route to the WireGuard VPN server through the IPSEC tunnel, which is wrong.
Add new supported devices to table of hardware
Does installing this version still cause bootloop and bricking issues for BT HomeHub 5?
Do you think I should upgrade from version 21.02.6 to this version or not at all recommended?
I have one more question, is it possible to brick my router in all versions of 22.03.X?
What should I do to stay on version 21.02.6?
Second service release without support for Linksys WRT AC series, are we dropping support or what?
Yes, support is dropped for wrt ac series in the 22.03 release. Use master or downgrade to 21.02
That's a shame, switch was patched months ago