All,
I recently setup a wrt3200acm with OpenWrt 21.02.1 r16325-88151b8303 . When I'm connected via a SSH terminal to another machine on the network, both wireless (5Ghz), I'll get an occasional ssh disconnect (even happens while I'm tying in wither screen or tmux; both tested to see if either helped) with the error message: client_loop: send disconnect: Broken pipe.
If I try to reconnect, shortly after the disconnect, I get the same message.
When I try to connect with verbose logging, I see the following:
OpenSSH_8.6p1, LibreSSL 2.8.3
debug1: Reading configuration data /Users/stduser/.ssh/config
debug1: /Users/stduser/.ssh/config line 1: Applying options for *
debug1: Reading configuration data /etc/ssh/ssh_config
debug1: /etc/ssh/ssh_config line 21: include /etc/ssh/ssh_config.d/* matched no files
debug1: /etc/ssh/ssh_config line 54: Applying options for *
debug2: resolve_canonicalize: hostname 172.20.1.111 is address
debug3: expanded UserKnownHostsFile '~/.ssh/known_hosts' -> '/Users/stduser/.ssh/known_hosts'
debug3: expanded UserKnownHostsFile '~/.ssh/known_hosts2' -> '/Users/stduser/.ssh/known_hosts2'
debug1: Authenticator provider $SSH_SK_PROVIDER did not resolve; disabling
debug3: ssh_connect_direct: entering
debug1: Connecting to 172.20.1.111 [172.20.1.111] port 22.
debug3: set_sock_tos: set socket 3 IP_TOS 0x08
debug1: Connection established.
debug1: identity file /Users/stduser/.ssh/id_rsa type 0
debug1: identity file /Users/stduser/.ssh/id_rsa-cert type -1
debug1: identity file /Users/stduser/.ssh/id_dsa type -1
debug1: identity file /Users/stduser/.ssh/id_dsa-cert type -1
debug1: identity file /Users/stduser/.ssh/id_ecdsa type 2
debug1: identity file /Users/stduser/.ssh/id_ecdsa-cert type -1
debug1: identity file /Users/stduser/.ssh/id_ecdsa_sk type -1
debug1: identity file /Users/stduser/.ssh/id_ecdsa_sk-cert type -1
debug1: identity file /Users/stduser/.ssh/id_ed25519 type 3
debug1: identity file /Users/stduser/.ssh/id_ed25519-cert type -1
debug1: identity file /Users/stduser/.ssh/id_ed25519_sk type -1
debug1: identity file /Users/stduser/.ssh/id_ed25519_sk-cert type -1
debug1: identity file /Users/stduser/.ssh/id_xmss type -1
debug1: identity file /Users/stduser/.ssh/id_xmss-cert type -1
debug1: Local version string SSH-2.0-OpenSSH_8.6
debug1: Remote protocol version 2.0, remote software version OpenSSH_8.6
debug1: compat_banner: match: OpenSSH_8.6 pat OpenSSH* compat 0x04000000
debug2: fd 3 setting O_NONBLOCK
debug1: Authenticating to 172.20.1.111:22 as 'stduser'
debug3: record_hostkey: found key type ED25519 in file /Users/stduser/.ssh/known_hosts:53
debug3: load_hostkeys_file: loaded 1 keys from 172.20.1.111
debug1: load_hostkeys: fopen /Users/stduser/.ssh/known_hosts2: No such file or directory
debug1: load_hostkeys: fopen /etc/ssh/ssh_known_hosts: No such file or directory
debug1: load_hostkeys: fopen /etc/ssh/ssh_known_hosts2: No such file or directory
debug3: order_hostkeyalgs: have matching best-preference key type ssh-ed25519-cert-v01@openssh.com, using HostkeyAlgorithms verbatim
debug3: send packet: type 20
debug1: SSH2_MSG_KEXINIT sent
debug3: receive packet: type 20
debug1: SSH2_MSG_KEXINIT received
debug2: local client KEXINIT proposal
debug2: KEX algorithms: curve25519-sha256,curve25519-sha256@libssh.org,ecdh-sha2-nistp256,ecdh-sha2-nistp384,ecdh-sha2-nistp521,diffie-hellman-group-exchange-sha256,diffie-hellman-group16-sha512,diffie-hellman-group18-sha512,diffie-hellman-group14-sha256,ext-info-c
debug2: host key algorithms: ssh-ed25519-cert-v01@openssh.com,ecdsa-sha2-nistp256-cert-v01@openssh.com,ecdsa-sha2-nistp384-cert-v01@openssh.com,ecdsa-sha2-nistp521-cert-v01@openssh.com,sk-ssh-ed25519-cert-v01@openssh.com,sk-ecdsa-sha2-nistp256-cert-v01@openssh.com,rsa-sha2-512-cert-v01@openssh.com,rsa-sha2-256-cert-v01@openssh.com,ssh-rsa-cert-v01@openssh.com,ssh-ed25519,ecdsa-sha2-nistp256,ecdsa-sha2-nistp384,ecdsa-sha2-nistp521,sk-ssh-ed25519@openssh.com,sk-ecdsa-sha2-nistp256@openssh.com,rsa-sha2-512,rsa-sha2-256,ssh-rsa
debug2: ciphers ctos: chacha20-poly1305@openssh.com,aes128-ctr,aes192-ctr,aes256-ctr,aes128-gcm@openssh.com,aes256-gcm@openssh.com
debug2: ciphers stoc: chacha20-poly1305@openssh.com,aes128-ctr,aes192-ctr,aes256-ctr,aes128-gcm@openssh.com,aes256-gcm@openssh.com
debug2: MACs ctos: umac-64-etm@openssh.com,umac-128-etm@openssh.com,hmac-sha2-256-etm@openssh.com,hmac-sha2-512-etm@openssh.com,hmac-sha1-etm@openssh.com,umac-64@openssh.com,umac-128@openssh.com,hmac-sha2-256,hmac-sha2-512,hmac-sha1
debug2: MACs stoc: umac-64-etm@openssh.com,umac-128-etm@openssh.com,hmac-sha2-256-etm@openssh.com,hmac-sha2-512-etm@openssh.com,hmac-sha1-etm@openssh.com,umac-64@openssh.com,umac-128@openssh.com,hmac-sha2-256,hmac-sha2-512,hmac-sha1
debug2: compression ctos: none,zlib@openssh.com,zlib
debug2: compression stoc: none,zlib@openssh.com,zlib
debug2: languages ctos:
debug2: languages stoc:
debug2: first_kex_follows 0
debug2: reserved 0
debug2: peer server KEXINIT proposal
debug2: KEX algorithms: curve25519-sha256,curve25519-sha256@libssh.org,ecdh-sha2-nistp256,ecdh-sha2-nistp384,ecdh-sha2-nistp521,diffie-hellman-group-exchange-sha256,diffie-hellman-group14-sha256,diffie-hellman-group16-sha512,diffie-hellman-group18-sha512
debug2: host key algorithms: rsa-sha2-512,rsa-sha2-256,ecdsa-sha2-nistp256,ssh-ed25519
debug2: ciphers ctos: aes256-gcm@openssh.com,chacha20-poly1305@openssh.com,aes256-ctr,aes128-gcm@openssh.com,aes128-ctr
debug2: ciphers stoc: aes256-gcm@openssh.com,chacha20-poly1305@openssh.com,aes256-ctr,aes128-gcm@openssh.com,aes128-ctr
debug2: MACs ctos: hmac-sha2-256-etm@openssh.com,hmac-sha1-etm@openssh.com,umac-128-etm@openssh.com,hmac-sha2-512-etm@openssh.com,hmac-sha2-256,hmac-sha1,umac-128@openssh.com,hmac-sha2-512
debug2: MACs stoc: hmac-sha2-256-etm@openssh.com,hmac-sha1-etm@openssh.com,umac-128-etm@openssh.com,hmac-sha2-512-etm@openssh.com,hmac-sha2-256,hmac-sha1,umac-128@openssh.com,hmac-sha2-512
debug2: compression ctos: none,zlib@openssh.com
debug2: compression stoc: none,zlib@openssh.com
debug2: languages ctos:
debug2: languages stoc:
debug2: first_kex_follows 0
debug2: reserved 0
debug1: kex: algorithm: curve25519-sha256
debug1: kex: host key algorithm: ssh-ed25519
debug1: kex: server->client cipher: chacha20-poly1305@openssh.com MAC: <implicit> compression: none
debug1: kex: client->server cipher: chacha20-poly1305@openssh.com MAC: <implicit> compression: none
debug3: send packet: type 30
debug1: expecting SSH2_MSG_KEX_ECDH_REPLY
debug3: receive packet: type 31
debug1: SSH2_MSG_KEX_ECDH_REPLY received
debug1: Server host key: ssh-ed25519 SHA256:Z9oqGRlH5vpg4Sj1hZPDzDO4Ccb78Ckf3j51e2KC/6o
debug3: record_hostkey: found key type ED25519 in file /Users/stduser/.ssh/known_hosts:53
debug3: load_hostkeys_file: loaded 1 keys from 172.20.1.111
debug1: load_hostkeys: fopen /Users/stduser/.ssh/known_hosts2: No such file or directory
debug1: load_hostkeys: fopen /etc/ssh/ssh_known_hosts: No such file or directory
debug1: load_hostkeys: fopen /etc/ssh/ssh_known_hosts2: No such file or directory
debug1: Host '172.20.1.111' is known and matches the ED25519 host key.
debug1: Found key in /Users/stduser/.ssh/known_hosts:53
debug3: send packet: type 21
debug2: set_newkeys: mode 1
debug1: rekey out after 134217728 blocks
debug1: SSH2_MSG_NEWKEYS sent
debug1: expecting SSH2_MSG_NEWKEYS
debug3: receive packet: type 21
debug1: SSH2_MSG_NEWKEYS received
debug2: set_newkeys: mode 0
debug1: rekey in after 134217728 blocks
debug1: Will attempt key: /Users/stduser/.ssh/id_rsa RSA SHA256:zpLWJIjAi3eJ6STQDJWuEuJIbnETkUznnCX55txXS3A
debug1: Will attempt key: /Users/stduser/.ssh/id_dsa
debug1: Will attempt key: /Users/stduser/.ssh/id_ecdsa ECDSA SHA256:BLXORCMtsZSHyKvcQRCgfPJd+f5XLGWby+eamvJDeD4
debug1: Will attempt key: /Users/stduser/.ssh/id_ecdsa_sk
debug1: Will attempt key: /Users/stduser/.ssh/id_ed25519 ED25519 SHA256:muW5Q2sgpczK6UA/U1S3k+nghs7VO5b4i1ehRPj7pOk
debug1: Will attempt key: /Users/stduser/.ssh/id_ed25519_sk
debug1: Will attempt key: /Users/stduser/.ssh/id_xmss
debug2: pubkey_prepare: done
debug3: send packet: type 5
debug3: receive packet: type 7
debug1: SSH2_MSG_EXT_INFO received
debug1: kex_input_ext_info: server-sig-algs=<ssh-ed25519,sk-ssh-ed25519@openssh.com,ssh-rsa,rsa-sha2-256,rsa-sha2-512,ssh-dss,ecdsa-sha2-nistp256,ecdsa-sha2-nistp384,ecdsa-sha2-nistp521,sk-ecdsa-sha2-nistp256@openssh.com,webauthn-sk-ecdsa-sha2-nistp256@openssh.com>
debug3: receive packet: type 6
debug2: service_accept: ssh-userauth
debug1: SSH2_MSG_SERVICE_ACCEPT received
debug3: send packet: type 50
debug3: receive packet: type 51
debug1: Authentications that can continue: publickey,gssapi-keyex,gssapi-with-mic,password
debug3: start over, passed a different list publickey,gssapi-keyex,gssapi-with-mic,password
debug3: preferred publickey,keyboard-interactive,password
debug3: authmethod_lookup publickey
debug3: remaining preferred: keyboard-interactive,password
debug3: authmethod_is_enabled publickey
debug1: Next authentication method: publickey
debug1: Offering public key: /Users/stduser/.ssh/id_rsa RSA SHA256:zpLWJIjAi3eJ6STQDJWuEuJIbnETkUznnCX55txXS3A
debug3: send packet: type 50
debug2: we sent a publickey packet, wait for reply
debug3: receive packet: type 51
debug1: Authentications that can continue: publickey,gssapi-keyex,gssapi-with-mic,password
debug1: Trying private key: /Users/stduser/.ssh/id_dsa
debug3: no such identity: /Users/stduser/.ssh/id_dsa: No such file or directory
debug1: Offering public key: /Users/stduser/.ssh/id_ecdsa ECDSA SHA256:BLXORCMtsZSHyKvcQRCgfPJd+f5XLGWby+eamvJDeD4
debug3: send packet: type 50
debug2: we sent a publickey packet, wait for reply
debug3: receive packet: type 51
debug1: Authentications that can continue: publickey,gssapi-keyex,gssapi-with-mic,password
debug1: Trying private key: /Users/stduser/.ssh/id_ecdsa_sk
debug3: no such identity: /Users/stduser/.ssh/id_ecdsa_sk: No such file or directory
debug1: Offering public key: /Users/stduser/.ssh/id_ed25519 ED25519 SHA256:muW5Q2sgpczK6UA/U1S3k+nghs7VO5b4i1ehRPj7pOk
debug3: send packet: type 50
debug2: we sent a publickey packet, wait for reply
debug3: receive packet: type 60
debug1: Server accepts key: /Users/stduser/.ssh/id_ed25519 ED25519 SHA256:muW5Q2sgpczK6UA/U1S3k+nghs7VO5b4i1ehRPj7pOk
debug3: sign_and_send_pubkey: ED25519 SHA256:muW5Q2sgpczK6UA/U1S3k+nghs7VO5b4i1ehRPj7pOk
debug3: sign_and_send_pubkey: signing using ssh-ed25519 SHA256:muW5Q2sgpczK6UA/U1S3k+nghs7VO5b4i1ehRPj7pOk
debug3: send packet: type 50
debug3: receive packet: type 52
debug1: Authentication succeeded (publickey).
Authenticated to 172.20.1.111 ([172.20.1.111]:22).
debug1: channel 0: new [client-session]
debug3: ssh_session2_open: channel_new: 0
debug2: channel 0: send open
debug3: send packet: type 90
debug1: Requesting no-more-sessions@openssh.com
debug3: send packet: type 80
debug1: Entering interactive session.
debug1: pledge: filesystem full
debug3: receive packet: type 80
debug1: client_input_global_request: rtype hostkeys-00@openssh.com want_reply 0
debug3: client_input_hostkeys: received RSA key SHA256:afks5SBb4uOec9t93HJq/eKq0zp/W9PhGUiCGUeFQIE
debug3: client_input_hostkeys: received ECDSA key SHA256:zalMVjkkUr4xesN3TGpOFM73lYYFL9+qrMPJmxErfBk
debug3: client_input_hostkeys: received ED25519 key SHA256:Z9oqGRlH5vpg4Sj1hZPDzDO4Ccb78Ckf3j51e2KC/6o
debug1: client_input_hostkeys: searching /Users/stduser/.ssh/known_hosts for 172.20.1.111 / (none)
debug3: hostkeys_foreach: reading file "/Users/stduser/.ssh/known_hosts"
debug3: hostkeys_find: found ecdsa-sha2-nistp256 key under different name/addr at /Users/stduser/.ssh/known_hosts:25
debug3: hostkeys_find: found ecdsa-sha2-nistp256 key under different name/addr at /Users/stduser/.ssh/known_hosts:30
debug3: hostkeys_find: found ssh-ed25519 key under different name/addr at /Users/stduser/.ssh/known_hosts:51
debug3: hostkeys_find: found ssh-ed25519 key under different name/addr at /Users/stduser/.ssh/known_hosts:52
debug3: hostkeys_find: found ssh-ed25519 key at /Users/stduser/.ssh/known_hosts:53
debug1: client_input_hostkeys: searching /Users/stduser/.ssh/known_hosts2 for 172.20.1.111 / (none)
debug1: client_input_hostkeys: hostkeys file /Users/stduser/.ssh/known_hosts2 does not exist
debug3: client_input_hostkeys: 3 server keys: 2 new, 18446744073709551615 retained, 2 incomplete match. 0 to remove
debug1: client_input_hostkeys: host key found matching a different name/address, skipping UserKnownHostsFile update
debug3: receive packet: type 4
debug1: Remote: /home/stduser/.ssh/authorized_keys:1: key options: agent-forwarding port-forwarding pty user-rc x11-forwarding
debug3: receive packet: type 4
debug1: Remote: /home/stduser/.ssh/authorized_keys:1: key options: agent-forwarding port-forwarding pty user-rc x11-forwarding
debug3: receive packet: type 91
debug2: channel_input_open_confirmation: channel 0: callback start
debug2: fd 3 setting TCP_NODELAY
debug3: set_sock_tos: set socket 3 IP_TOS 0x08
debug2: client_session2_setup: id 0
debug2: channel 0: request pty-req confirm 1
debug3: send packet: type 98
debug1: Sending environment.
debug1: channel 0: setting env LC_TERMINAL_VERSION = "3.4.14"
debug2: channel 0: request env confirm 0
debug3: send packet: type 98
debug1: channel 0: setting env LANG = "en_US.UTF-8"
debug2: channel 0: request env confirm 0
debug3: send packet: type 98
debug1: channel 0: setting env LC_TERMINAL = "iTerm2"
debug2: channel 0: request env confirm 0
debug3: send packet: type 98
debug1: channel 0: setting env LC_ALL = "en_US.UTF-8"
debug2: channel 0: request env confirm 0
debug3: send packet: type 98
debug2: channel 0: request shell confirm 1
debug3: send packet: type 98
debug2: channel_input_open_confirmation: channel 0: callback done
debug2: channel 0: open confirm rwindow 0 rmax 32768
debug3: send packet: type 1
client_loop: send disconnect: Broken pipe
Exit 255
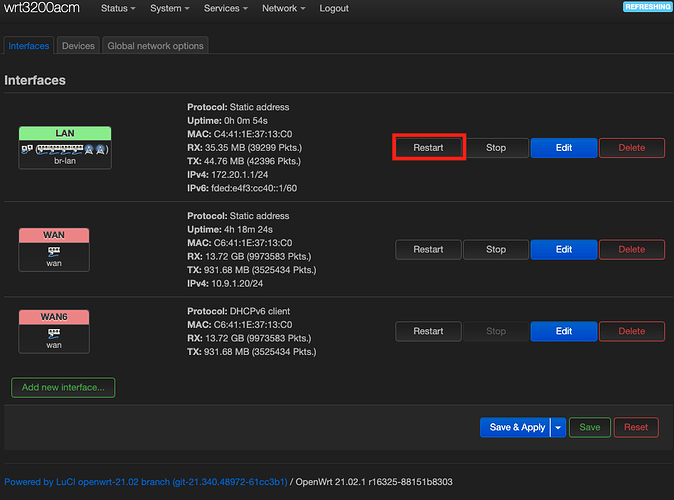
If I wait for a while, say about thirty minutes, it works again but this will inevitably happen again. Maybe it will happen in three hours, maybe tomorrow but it will happen. I've seen a few posts about turning off "Software flow offloading" which I do not have enabled.
Here are some more data points:
- Even when I cannot SSH to
172.20.1.111, I can SSH into the gateway (172.20.1.1). - I can connect to the same host (in this case
172.20.1.111) via HTTP/HTTPS, it's only SSH that seems to have an issue. - I can also ping the host
172.20.1.111with zero packet loss.
Any help would be awesome.
Thanks in advance.
- Mike D.