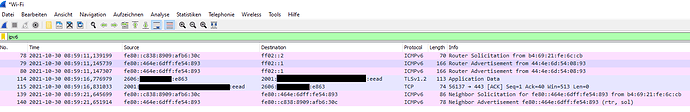
The tcpdump has very little data, it only ran for 5 seconds and there was no router solicitation or dhcpv6 solicitation captured. Let it run and connect one client to capture the whole packet exchange.
I've entered ipconfig /renew6 on the windows client machine and got the following outputs. Does this help?
Windows
>ipconfig /renew6
Windows IP Configuration
An error occurred while renewing interface Ethernet 2 : The semaphore timeout period has expired.
An error occurred while renewing interface VMware Network Adapter VMnet1 : The semaphore timeout period has expired.
An error occurred while renewing interface VMware Network Adapter VMnet8 : The semaphore timeout period has expired.
Ethernet adapter Ethernet 2:
Connection-specific DNS Suffix . : fritz.box
Link-local IPv6 Address . . . . . : fe80::244d:d71e:fdf0:5d0e%22
IPv4 Address. . . . . . . . . . . : 192.168.178.63
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . : 192.168.178.1
Openwrt
root@OpenWrt:~# tcpdump -i br-lan -vn ip6
tcpdump: listening on br-lan, link-type EN10MB (Ethernet), capture size 262144 bytes
06:38:18.861631 IP6 (flowlabel 0x051e5, hlim 1, next-header UDP (17) payload length: 123) fe80::244d:d71e:fdf0:5d0e.546 > ff02::1:2.547: [udp sum ok] dhcp6 solicit (xid=3e437b (elapsed-time 1503) (client-ID hwaddr/time type 1 time 594849418 84a93e9e2418) (IA_NA IAID:286286565 T1:0 T2:0) (Client-FQDN) (vendor-class) (option-request vendor-specific-info DNS-server DNS-search-list Client-FQDN))
06:38:18.871011 IP6 (flowlabel 0x9f4b2, hlim 64, next-header UDP (17) payload length: 68) fe80::464e:6dff:fe54:893.547 > fe80::244d:d71e:fdf0:5d0e.546: [udp sum ok] dhcp6 advertise (xid=3e437b (client-ID hwaddr/time type 1 time 594849418 84a93e9e2418) (server-ID hwaddr type 1 444e6d540893) (status-code NoAddrsAvail))
06:38:42.321558 IP6 (flowlabel 0x0c36d, hlim 1, next-header UDP (17) payload length: 123) fe80::244d:d71e:fdf0:5d0e.546 > ff02::1:2.547: [udp sum ok] dhcp6 solicit (xid=dfaba1 (elapsed-time 0) (client-ID hwaddr/time type 1 time 594849418 84a93e9e2418) (IA_NA IAID:286286565 T1:0 T2:0) (Client-FQDN) (vendor-class) (option-request vendor-specific-info DNS-server DNS-search-list Client-FQDN))
06:38:42.329248 IP6 (flowlabel 0x9f4b2, hlim 64, next-header UDP (17) payload length: 68) fe80::464e:6dff:fe54:893.547 > fe80::244d:d71e:fdf0:5d0e.546: [udp sum ok] dhcp6 advertise (xid=dfaba1 (client-ID hwaddr/time type 1 time 594849418 84a93e9e2418) (server-ID hwaddr type 1 444e6d540893) (status-code NoAddrsAvail))
06:38:42.401992 IP6 (hlim 255, next-header ICMPv6 (58) payload length: 16) fe80::244d:d71e:fdf0:5d0e > ff02::2: [icmp6 sum ok] ICMP6, router solicitation, length 16
source link-address option (1), length 8 (1): 10:62:e5:8a:55:23
06:38:43.323481 IP6 (flowlabel 0x0c36d, hlim 1, next-header UDP (17) payload length: 123) fe80::244d:d71e:fdf0:5d0e.546 > ff02::1:2.547: [udp sum ok] dhcp6 solicit (xid=dfaba1 (elapsed-time 100) (client-ID hwaddr/time type 1 time 594849418 84a93e9e2418) (IA_NA IAID:286286565 T1:0 T2:0) (Client-FQDN) (vendor-class) (option-request vendor-specific-info DNS-server DNS-search-list Client-FQDN))
06:38:43.329080 IP6 (flowlabel 0x9f4b2, hlim 64, next-header UDP (17) payload length: 68) fe80::464e:6dff:fe54:893.547 > fe80::244d:d71e:fdf0:5d0e.546: [udp sum ok] dhcp6 advertise (xid=dfaba1 (client-ID hwaddr/time type 1 time 594849418 84a93e9e2418) (server-ID hwaddr type 1 444e6d540893) (status-code NoAddrsAvail))
06:38:45.336303 IP6 (flowlabel 0x0c36d, hlim 1, next-header UDP (17) payload length: 123) fe80::244d:d71e:fdf0:5d0e.546 > ff02::1:2.547: [udp sum ok] dhcp6 solicit (xid=dfaba1 (elapsed-time 301) (client-ID hwaddr/time type 1 time 594849418 84a93e9e2418) (IA_NA IAID:286286565 T1:0 T2:0) (Client-FQDN) (vendor-class) (option-request vendor-specific-info DNS-server DNS-search-list Client-FQDN))
06:38:45.343727 IP6 (flowlabel 0x9f4b2, hlim 64, next-header UDP (17) payload length: 68) fe80::464e:6dff:fe54:893.547 > fe80::244d:d71e:fdf0:5d0e.546: [udp sum ok] dhcp6 advertise (xid=dfaba1 (client-ID hwaddr/time type 1 time 594849418 84a93e9e2418) (server-ID hwaddr type 1 444e6d540893) (status-code NoAddrsAvail))
06:38:46.395950 IP6 (hlim 255, next-header ICMPv6 (58) payload length: 16) fe80::244d:d71e:fdf0:5d0e > ff02::2: [icmp6 sum ok] ICMP6, router solicitation, length 16
source link-address option (1), length 8 (1): 10:62:e5:8a:55:23
06:38:49.345007 IP6 (flowlabel 0x0c36d, hlim 1, next-header UDP (17) payload length: 123) fe80::244d:d71e:fdf0:5d0e.546 > ff02::1:2.547: [udp sum ok] dhcp6 solicit (xid=dfaba1 (elapsed-time 701) (client-ID hwaddr/time type 1 time 594849418 84a93e9e2418) (IA_NA IAID:286286565 T1:0 T2:0) (Client-FQDN) (vendor-class) (option-request vendor-specific-info DNS-server DNS-search-list Client-FQDN))
06:38:49.352911 IP6 (flowlabel 0x9f4b2, hlim 64, next-header UDP (17) payload length: 68) fe80::464e:6dff:fe54:893.547 > fe80::244d:d71e:fdf0:5d0e.546: [udp sum ok] dhcp6 advertise (xid=dfaba1 (client-ID hwaddr/time type 1 time 594849418 84a93e9e2418) (server-ID hwaddr type 1 444e6d540893) (status-code NoAddrsAvail))
06:38:50.403926 IP6 (hlim 255, next-header ICMPv6 (58) payload length: 16) fe80::244d:d71e:fdf0:5d0e > ff02::2: [icmp6 sum ok] ICMP6, router solicitation, length 16
source link-address option (1), length 8 (1): 10:62:e5:8a:55:23
06:38:57.345422 IP6 (flowlabel 0x0c36d, hlim 1, next-header UDP (17) payload length: 123) fe80::244d:d71e:fdf0:5d0e.546 > ff02::1:2.547: [udp sum ok] dhcp6 solicit (xid=dfaba1 (elapsed-time 1501) (client-ID hwaddr/time type 1 time 594849418 84a93e9e2418) (IA_NA IAID:286286565 T1:0 T2:0) (Client-FQDN) (vendor-class) (option-request vendor-specific-info DNS-server DNS-search-list Client-FQDN))
06:38:57.355308 IP6 (flowlabel 0x9f4b2, hlim 64, next-header UDP (17) payload length: 68) fe80::464e:6dff:fe54:893.547 > fe80::244d:d71e:fdf0:5d0e.546: [udp sum ok] dhcp6 advertise (xid=dfaba1 (client-ID hwaddr/time type 1 time 594849418 84a93e9e2418) (server-ID hwaddr type 1 444e6d540893) (status-code NoAddrsAvail))
06:39:13.354577 IP6 (flowlabel 0x0c36d, hlim 1, next-header UDP (17) payload length: 123) fe80::244d:d71e:fdf0:5d0e.546 > ff02::1:2.547: [udp sum ok] dhcp6 solicit (xid=dfaba1 (elapsed-time 3103) (client-ID hwaddr/time type 1 time 594849418 84a93e9e2418) (IA_NA IAID:286286565 T1:0 T2:0) (Client-FQDN) (vendor-class) (option-request vendor-specific-info DNS-server DNS-search-list Client-FQDN))
06:39:13.362994 IP6 (flowlabel 0x9f4b2, hlim 64, next-header UDP (17) payload length: 68) fe80::464e:6dff:fe54:893.547 > fe80::244d:d71e:fdf0:5d0e.546: [udp sum ok] dhcp6 advertise (xid=dfaba1 (client-ID hwaddr/time type 1 time 594849418 84a93e9e2418) (server-ID hwaddr type 1 444e6d540893) (status-code NoAddrsAvail))
06:39:45.363622 IP6 (flowlabel 0x0c36d, hlim 1, next-header UDP (17) payload length: 123) fe80::244d:d71e:fdf0:5d0e.546 > ff02::1:2.547: [udp sum ok] dhcp6 solicit (xid=dfaba1 (elapsed-time 6303) (client-ID hwaddr/time type 1 time 594849418 84a93e9e2418) (IA_NA IAID:286286565 T1:0 T2:0) (Client-FQDN) (vendor-class) (option-request vendor-specific-info DNS-server DNS-search-list Client-FQDN))
06:39:45.371242 IP6 (flowlabel 0x9f4b2, hlim 64, next-header UDP (17) payload length: 68) fe80::464e:6dff:fe54:893.547 > fe80::244d:d71e:fdf0:5d0e.546: [udp sum ok] dhcp6 advertise (xid=dfaba1 (client-ID hwaddr/time type 1 time 594849418 84a93e9e2418) (server-ID hwaddr type 1 444e6d540893) (status-code NoAddrsAvail))
One thing is that router solicitations are left unanswered. Does the Fritzbox answer with RAs or only DHCP?
The other thing is that dhcp solicitations are answered. Does the lan host receive them? Can you run tcpdump or wireshark on the lan host to verify?
How can I find out?
I'll try TCPdump for Windows and let you know.
See if there is anything relevant in the Fritz menu.
If your host is running Windows, better install Wireshark and use ipv6 in the filter bar.
There's one setting activated. Should I deactivate it?
Also announce DNSv6 server via router advertisement (RFC 5006)
With this setting you specify that the FRITZ!Box identifies the local DNSv6 server in the local network by router advertisement. Alternatively, the network devices can identify the local DNSv6 server via DHCPv6.
Wireshark installation will take I while..
You can keep it activated.
Here's the output after entering:
ipconfig /renew6
with output:
Windows IP Configuration
An error occurred while renewing interface Ethernet 2 : The semaphore timeout period has expired.
| No. | Time | Source | Destination | Protocol | Length | Info |
|---|---|---|---|---|---|---|
| 2433 | 2021-10-29 15:47:11,557312 | fe80::244d:d71e:fdf0:5d0e | ff02::1:2 | DHCPv6 | 177 | Solicit XID: 0xe43d17 CID: 000100012374ae8a84a93e9e2418 |
| 2434 | 2021-10-29 15:47:11,565216 | fe80::464e:6dff:fe54:893 | fe80::244d:d71e:fdf0:5d0e | DHCPv6 | 122 | Advertise XID: 0xe43d17 CID: 000100012374ae8a84a93e9e2418 |
| 2435 | 2021-10-29 15:47:11,786475 | fe80::244d:d71e:fdf0:5d0e | ff02::2 | ICMPv6 | 70 | Router Solicitation from 10:62:e5:8a:55:23 |
| 2625 | 2021-10-29 15:47:12,563997 | fe80::244d:d71e:fdf0:5d0e | ff02::1:2 | DHCPv6 | 177 | Solicit XID: 0xe43d17 CID: 000100012374ae8a84a93e9e2418 |
| 2628 | 2021-10-29 15:47:12,575328 | fe80::464e:6dff:fe54:893 | fe80::244d:d71e:fdf0:5d0e | DHCPv6 | 122 | Advertise XID: 0xe43d17 CID: 000100012374ae8a84a93e9e2418 |
| 3233 | 2021-10-29 15:47:14,571071 | fe80::244d:d71e:fdf0:5d0e | ff02::1:2 | DHCPv6 | 177 | Solicit XID: 0xe43d17 CID: 000100012374ae8a84a93e9e2418 |
| 3234 | 2021-10-29 15:47:14,592505 | fe80::464e:6dff:fe54:893 | fe80::244d:d71e:fdf0:5d0e | DHCPv6 | 122 | Advertise XID: 0xe43d17 CID: 000100012374ae8a84a93e9e2418 |
| 3235 | 2021-10-29 15:47:15,780476 | fe80::244d:d71e:fdf0:5d0e | ff02::2 | ICMPv6 | 70 | Router Solicitation from 10:62:e5:8a:55:23 |
| 3260 | 2021-10-29 15:47:18,585432 | fe80::244d:d71e:fdf0:5d0e | ff02::1:2 | DHCPv6 | 177 | Solicit XID: 0xe43d17 CID: 000100012374ae8a84a93e9e2418 |
| 3261 | 2021-10-29 15:47:18,626062 | fe80::464e:6dff:fe54:893 | fe80::244d:d71e:fdf0:5d0e | DHCPv6 | 122 | Advertise XID: 0xe43d17 CID: 000100012374ae8a84a93e9e2418 |
| 3262 | 2021-10-29 15:47:19,790556 | fe80::244d:d71e:fdf0:5d0e | ff02::2 | ICMPv6 | 70 | Router Solicitation from 10:62:e5:8a:55:23 |
| 3327 | 2021-10-29 15:47:26,593525 | fe80::244d:d71e:fdf0:5d0e | ff02::1:2 | DHCPv6 | 177 | Solicit XID: 0xe43d17 CID: 000100012374ae8a84a93e9e2418 |
| 3328 | 2021-10-29 15:47:26,604367 | fe80::464e:6dff:fe54:893 | fe80::244d:d71e:fdf0:5d0e | DHCPv6 | 122 | Advertise XID: 0xe43d17 CID: 000100012374ae8a84a93e9e2418 |
| 3374 | 2021-10-29 15:47:42,599891 | fe80::244d:d71e:fdf0:5d0e | ff02::1:2 | DHCPv6 | 177 | Solicit XID: 0xe43d17 CID: 000100012374ae8a84a93e9e2418 |
| 3375 | 2021-10-29 15:47:42,610210 | fe80::464e:6dff:fe54:893 | fe80::244d:d71e:fdf0:5d0e | DHCPv6 | 122 | Advertise XID: 0xe43d17 CID: 000100012374ae8a84a93e9e2418 |
| 3635 | 2021-10-29 15:48:14,605392 | fe80::244d:d71e:fdf0:5d0e | ff02::1:2 | DHCPv6 | 177 | Solicit XID: 0xe43d17 CID: 000100012374ae8a84a93e9e2418 |
| 3636 | 2021-10-29 15:48:14,614377 | fe80::464e:6dff:fe54:893 | fe80::244d:d71e:fdf0:5d0e | DHCPv6 | 122 | Advertise XID: 0xe43d17 CID: 000100012374ae8a84a93e9e2418 |
It's the same as from OpenWrt. Windows are soliciting a DHCPv6 and get the advertisement, then instead of continuing with sending the request they resend a solicit. (https://en.wikipedia.org/wiki/DHCPv6#DHCPv6_Message_types)
Can you try to connect this windows host directly on the fritz and run again the wireshark?
Without OpenWrt inbetween, it works like a charm. I'm also getting global IPv6 adresses.
(I've hidden the adresses for privacy reasons):
| No. | Time | Protocol | Length | Info |
|---|---|---|---|---|
| 803 | 2021-10-29 17:17:33,499326 | QUIC | 1399 | 0-RTT, DCID=3b545c8a1f2e918a, SCID=97f1f6 |
| 1861 | 2021-10-29 17:18:22,615228 | TCP | 94 | 40797 → 80 [SYN] Seq=0 Win=28640 Len=0 MSS=1432 SACK_PERM=1 TSval=46857576 TSecr=0 WS=64 |
| 1090 | 2021-10-29 17:17:33,973174 | TCP | 74 | 60577 → 80 [ACK] Seq=1 Ack=1 Win=131840 Len=0 |
| 1120 | 2021-10-29 17:17:34,079614 | TCP | 74 | 60577 → 80 [ACK] Seq=434 Ack=940 Win=130816 Len=0 |
| 1085 | 2021-10-29 17:17:33,957264 | TCP | 86 | 60577 → 80 [SYN] Seq=0 Win=64440 Len=0 MSS=1432 WS=256 SACK_PERM=1 |
| 1091 | 2021-10-29 17:17:33,973292 | TCP | 74 | 60578 → 80 [ACK] Seq=1 Ack=1 Win=131840 Len=0 |
| 1131 | 2021-10-29 17:17:34,094660 | TCP | 74 | 60578 → 80 [ACK] Seq=434 Ack=941 Win=130816 Len=0 |
| 1086 | 2021-10-29 17:17:33,958078 | TCP | 86 | 60578 → 80 [SYN] Seq=0 Win=64440 Len=0 MSS=1432 WS=256 SACK_PERM=1 |
| 1096 | 2021-10-29 17:17:33,989968 | TCP | 74 | 80 → 60577 [ACK] Seq=1 Ack=434 Win=67584 Len=0 |
| 1088 | 2021-10-29 17:17:33,972734 | TCP | 86 | 80 → 60577 [SYN, ACK] Seq=0 Ack=1 Win=65535 Len=0 MSS=1360 SACK_PERM=1 WS=1024 |
| 1097 | 2021-10-29 17:17:33,991351 | TCP | 74 | 80 → 60578 [ACK] Seq=1 Ack=434 Win=67584 Len=0 |
| 1089 | 2021-10-29 17:17:33,972734 | TCP | 86 | 80 → 60578 [SYN, ACK] Seq=0 Ack=1 Win=65535 Len=0 MSS=1360 SACK_PERM=1 WS=1024 |
| 986 | 2021-10-29 17:17:33,808519 | QUIC | 149 | Handshake, DCID=55ab2a9ac03ff983, SCID=e667e6 |
| 979 | 2021-10-29 17:17:33,794878 | QUIC | 1399 | Handshake, DCID=e667e6, SCID=55ab2a9ac03ff983 |
| 980 | 2021-10-29 17:17:33,794878 | QUIC | 1399 | Handshake, DCID=e667e6, SCID=55ab2a9ac03ff983 |
| 981 | 2021-10-29 17:17:33,794878 | QUIC | 1399 | Handshake, DCID=e667e6, SCID=55ab2a9ac03ff983 |
| 972 | 2021-10-29 17:17:33,769900 | QUIC | 1399 | Initial, DCID=55ab2a9ac03ff9832b4429b681, SCID=e667e6, PKN: 0, CRYPTO |
| 978 | 2021-10-29 17:17:33,794878 | QUIC | 1399 | Initial, DCID=e667e6, SCID=55ab2a9ac03ff983, PKN: 1, ACK, CRYPTO, PADDING |
| 816 | 2021-10-29 17:17:33,548994 | QUIC | 275 | Protected Payload (KP0), DCID=3b545c8a1f2e918a |
| 817 | 2021-10-29 17:17:33,550678 | QUIC | 349 | Protected Payload (KP0), DCID=3b545c8a1f2e918a |
| 827 | 2021-10-29 17:17:33,566547 | QUIC | 93 | Protected Payload (KP0), DCID=3b545c8a1f2e918a |
| 842 | 2021-10-29 17:17:33,573492 | QUIC | 98 | Protected Payload (KP0), DCID=3b545c8a1f2e918a |
| 1251 | 2021-10-29 17:17:38,795282 | QUIC | 284 | Protected Payload (KP0), DCID=3b545c8a1f2e918a |
| 1257 | 2021-10-29 17:17:38,821040 | QUIC | 98 | Protected Payload (KP0), DCID=3b545c8a1f2e918a |
| 991 | 2021-10-29 17:17:33,821775 | QUIC | 170 | Protected Payload (KP0), DCID=55ab2a9ac03ff983 |
| 992 | 2021-10-29 17:17:33,822060 | QUIC | 125 | Protected Payload (KP0), DCID=55ab2a9ac03ff983 |
| 1006 | 2021-10-29 17:17:33,841133 | QUIC | 93 | Protected Payload (KP0), DCID=55ab2a9ac03ff983 |
| 1416 | 2021-10-29 17:17:39,044808 | QUIC | 422 | Protected Payload (KP0), DCID=55ab2a9ac03ff983 |
| 1455 | 2021-10-29 17:17:39,053218 | QUIC | 359 | Protected Payload (KP0), DCID=55ab2a9ac03ff983 |
| 1498 | 2021-10-29 17:17:39,060189 | QUIC | 98 | Protected Payload (KP0), DCID=55ab2a9ac03ff983 |
| 1508 | 2021-10-29 17:17:39,064288 | QUIC | 93 | Protected Payload (KP0), DCID=55ab2a9ac03ff983 |
| 1514 | 2021-10-29 17:17:39,071912 | QUIC | 98 | Protected Payload (KP0), DCID=55ab2a9ac03ff983 |
| 1519 | 2021-10-29 17:17:39,075894 | QUIC | 93 | Protected Payload (KP0), DCID=55ab2a9ac03ff983 |
| 1526 | 2021-10-29 17:17:39,078334 | QUIC | 93 | Protected Payload (KP0), DCID=55ab2a9ac03ff983 |
| 1528 | 2021-10-29 17:17:39,078928 | QUIC | 93 | Protected Payload (KP0), DCID=55ab2a9ac03ff983 |
| 812 | 2021-10-29 17:17:33,526613 | QUIC | 1399 | Protected Payload (KP0), DCID=97f1f6 |
| 813 | 2021-10-29 17:17:33,526613 | QUIC | 671 | Protected Payload (KP0), DCID=97f1f6 |
| 815 | 2021-10-29 17:17:33,546669 | QUIC | 91 | Protected Payload (KP0), DCID=97f1f6 |
| 822 | 2021-10-29 17:17:33,561209 | QUIC | 169 | Protected Payload (KP0), DCID=97f1f6 |
| 824 | 2021-10-29 17:17:33,562740 | QUIC | 92 | Protected Payload (KP0), DCID=97f1f6 |
| 838 | 2021-10-29 17:17:33,572688 | QUIC | 1296 | Protected Payload (KP0), DCID=97f1f6 |
| 839 | 2021-10-29 17:17:33,572688 | QUIC | 99 | Protected Payload (KP0), DCID=97f1f6 |
| 840 | 2021-10-29 17:17:33,572688 | QUIC | 253 | Protected Payload (KP0), DCID=97f1f6 |
| 873 | 2021-10-29 17:17:33,611745 | QUIC | 90 | Protected Payload (KP0), DCID=97f1f6 |
| 1253 | 2021-10-29 17:17:38,810844 | QUIC | 92 | Protected Payload (KP0), DCID=97f1f6 |
| 1254 | 2021-10-29 17:17:38,820091 | QUIC | 883 | Protected Payload (KP0), DCID=97f1f6 |
| 1255 | 2021-10-29 17:17:38,820091 | QUIC | 99 | Protected Payload (KP0), DCID=97f1f6 |
| 1256 | 2021-10-29 17:17:38,820091 | QUIC | 202 | Protected Payload (KP0), DCID=97f1f6 |
| 1260 | 2021-10-29 17:17:38,860837 | QUIC | 90 | Protected Payload (KP0), DCID=97f1f6 |
| 982 | 2021-10-29 17:17:33,794878 | QUIC | 616 | Protected Payload (KP0), DCID=e667e6 |
| 1002 | 2021-10-29 17:17:33,834087 | QUIC | 671 | Protected Payload (KP0), DCID=e667e6 |
| 1003 | 2021-10-29 17:17:33,834087 | QUIC | 170 | Protected Payload (KP0), DCID=e667e6 |
| 1012 | 2021-10-29 17:17:33,859930 | QUIC | 90 | Protected Payload (KP0), DCID=e667e6 |
| 1491 | 2021-10-29 17:17:39,058285 | QUIC | 92 | Protected Payload (KP0), DCID=e667e6 |
| 1492 | 2021-10-29 17:17:39,058285 | QUIC | 1395 | Protected Payload (KP0), DCID=e667e6 |
| 1493 | 2021-10-29 17:17:39,058285 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1494 | 2021-10-29 17:17:39,058285 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1495 | 2021-10-29 17:17:39,058285 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1496 | 2021-10-29 17:17:39,058285 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1499 | 2021-10-29 17:17:39,063296 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1500 | 2021-10-29 17:17:39,063296 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1501 | 2021-10-29 17:17:39,063296 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1502 | 2021-10-29 17:17:39,063296 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1503 | 2021-10-29 17:17:39,063296 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1504 | 2021-10-29 17:17:39,063296 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1505 | 2021-10-29 17:17:39,063296 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1506 | 2021-10-29 17:17:39,063296 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1507 | 2021-10-29 17:17:39,063296 | QUIC | 297 | Protected Payload (KP0), DCID=e667e6 |
| 1510 | 2021-10-29 17:17:39,070690 | QUIC | 92 | Protected Payload (KP0), DCID=e667e6 |
| 1511 | 2021-10-29 17:17:39,070690 | QUIC | 1395 | Protected Payload (KP0), DCID=e667e6 |
| 1513 | 2021-10-29 17:17:39,070690 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1515 | 2021-10-29 17:17:39,075095 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1516 | 2021-10-29 17:17:39,075095 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1517 | 2021-10-29 17:17:39,075095 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1520 | 2021-10-29 17:17:39,077628 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1521 | 2021-10-29 17:17:39,077628 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1522 | 2021-10-29 17:17:39,077628 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1523 | 2021-10-29 17:17:39,078097 | QUIC | 1399 | Protected Payload (KP0), DCID=e667e6 |
| 1524 | 2021-10-29 17:17:39,078097 | QUIC | 1101 | Protected Payload (KP0), DCID=e667e6 |
| 1531 | 2021-10-29 17:17:39,113891 | QUIC | 90 | Protected Payload (KP0), DCID=e667e6 |
| 1092 | 2021-10-29 17:17:33,973449 | OCSP | 507 | Request |
| 1093 | 2021-10-29 17:17:33,973880 | OCSP | 507 | Request |
| 1099 | 2021-10-29 17:17:34,033374 | OCSP | 1013 | Response |
| 1100 | 2021-10-29 17:17:34,039433 | OCSP | 1014 | Response |
| 1585 | 2021-10-29 17:17:44,057485 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60577 [ACK] Seq=940 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 1646 | 2021-10-29 17:17:54,085547 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60577 [ACK] Seq=940 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 1711 | 2021-10-29 17:18:04,111468 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60577 [ACK] Seq=940 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 1803 | 2021-10-29 17:18:14,145313 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60577 [ACK] Seq=940 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 1873 | 2021-10-29 17:18:24,166865 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60577 [ACK] Seq=940 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 2004 | 2021-10-29 17:18:34,196787 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60577 [ACK] Seq=940 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 2081 | 2021-10-29 17:18:44,211832 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60577 [ACK] Seq=940 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 2267 | 2021-10-29 17:18:54,229474 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60577 [ACK] Seq=940 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 2321 | 2021-10-29 17:19:04,256758 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60577 [ACK] Seq=940 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 1586 | 2021-10-29 17:17:44,057485 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60578 [ACK] Seq=941 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 1647 | 2021-10-29 17:17:54,085547 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60578 [ACK] Seq=941 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 1712 | 2021-10-29 17:18:04,112809 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60578 [ACK] Seq=941 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 1802 | 2021-10-29 17:18:14,145313 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60578 [ACK] Seq=941 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 1874 | 2021-10-29 17:18:24,168087 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60578 [ACK] Seq=941 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 2003 | 2021-10-29 17:18:34,196787 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60578 [ACK] Seq=941 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 2082 | 2021-10-29 17:18:44,213055 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60578 [ACK] Seq=941 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 2268 | 2021-10-29 17:18:54,235559 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60578 [ACK] Seq=941 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 2322 | 2021-10-29 17:19:04,257800 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60578 [ACK] Seq=941 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 1584 | 2021-10-29 17:17:44,043520 | TCP | 75 | [TCP Keep-Alive] 60577 → 80 [ACK] Seq=433 Ack=940 Win=130816 Len=1 |
| 1644 | 2021-10-29 17:17:54,071836 | TCP | 75 | [TCP Keep-Alive] 60577 → 80 [ACK] Seq=433 Ack=940 Win=130816 Len=1 |
| 1710 | 2021-10-29 17:18:04,098481 | TCP | 75 | [TCP Keep-Alive] 60577 → 80 [ACK] Seq=433 Ack=940 Win=130816 Len=1 |
| 1801 | 2021-10-29 17:18:14,131624 | TCP | 75 | [TCP Keep-Alive] 60577 → 80 [ACK] Seq=433 Ack=940 Win=130816 Len=1 |
| 1872 | 2021-10-29 17:18:24,154128 | TCP | 75 | [TCP Keep-Alive] 60577 → 80 [ACK] Seq=433 Ack=940 Win=130816 Len=1 |
| 2002 | 2021-10-29 17:18:34,182410 | TCP | 75 | [TCP Keep-Alive] 60577 → 80 [ACK] Seq=433 Ack=940 Win=130816 Len=1 |
| 2079 | 2021-10-29 17:18:44,199069 | TCP | 75 | [TCP Keep-Alive] 60577 → 80 [ACK] Seq=433 Ack=940 Win=130816 Len=1 |
| 2264 | 2021-10-29 17:18:54,214535 | TCP | 75 | [TCP Keep-Alive] 60577 → 80 [ACK] Seq=433 Ack=940 Win=130816 Len=1 |
| 2319 | 2021-10-29 17:19:04,244175 | TCP | 75 | [TCP Keep-Alive] 60577 → 80 [ACK] Seq=433 Ack=940 Win=130816 Len=1 |
| 1583 | 2021-10-29 17:17:44,043221 | TCP | 75 | [TCP Keep-Alive] 60578 → 80 [ACK] Seq=433 Ack=941 Win=130816 Len=1 |
| 1645 | 2021-10-29 17:17:54,071836 | TCP | 75 | [TCP Keep-Alive] 60578 → 80 [ACK] Seq=433 Ack=941 Win=130816 Len=1 |
| 1709 | 2021-10-29 17:18:04,098481 | TCP | 75 | [TCP Keep-Alive] 60578 → 80 [ACK] Seq=433 Ack=941 Win=130816 Len=1 |
| 1800 | 2021-10-29 17:18:14,131625 | TCP | 75 | [TCP Keep-Alive] 60578 → 80 [ACK] Seq=433 Ack=941 Win=130816 Len=1 |
| 1871 | 2021-10-29 17:18:24,154127 | TCP | 75 | [TCP Keep-Alive] 60578 → 80 [ACK] Seq=433 Ack=941 Win=130816 Len=1 |
| 2001 | 2021-10-29 17:18:34,182409 | TCP | 75 | [TCP Keep-Alive] 60578 → 80 [ACK] Seq=433 Ack=941 Win=130816 Len=1 |
| 2080 | 2021-10-29 17:18:44,199069 | TCP | 75 | [TCP Keep-Alive] 60578 → 80 [ACK] Seq=433 Ack=941 Win=130816 Len=1 |
| 2265 | 2021-10-29 17:18:54,214552 | TCP | 75 | [TCP Keep-Alive] 60578 → 80 [ACK] Seq=433 Ack=941 Win=130816 Len=1 |
| 2320 | 2021-10-29 17:19:04,244186 | TCP | 75 | [TCP Keep-Alive] 60578 → 80 [ACK] Seq=433 Ack=941 Win=130816 Len=1 |
| 1870 | 2021-10-29 17:18:23,635491 | TCP | 94 | [TCP Retransmission] 40797 → 80 [SYN] Seq=0 Win=28640 Len=0 MSS=1432 SACK_PERM=1 TSval=46857832 TSecr=0 WS=64 |
| 1886 | 2021-10-29 17:18:25,651511 | TCP | 94 | [TCP Retransmission] 40797 → 80 [SYN] Seq=0 Win=28640 Len=0 MSS=1432 SACK_PERM=1 TSval=46858336 TSecr=0 WS=64 |
| 1919 | 2021-10-29 17:18:29,874549 | TCP | 94 | [TCP Retransmission] 40797 → 80 [SYN] Seq=0 Win=28640 Len=0 MSS=1432 SACK_PERM=1 TSval=46859392 TSecr=0 WS=64 |
| 2380 | 2021-10-29 17:19:14,270279 | TCP | 75 | [TCP Keep-Alive] 60577 → 80 [ACK] Seq=433 Ack=940 Win=130816 Len=1 |
| 2381 | 2021-10-29 17:19:14,270279 | TCP | 75 | [TCP Keep-Alive] 60578 → 80 [ACK] Seq=433 Ack=941 Win=130816 Len=1 |
| 2382 | 2021-10-29 17:19:14,284044 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60578 [ACK] Seq=941 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 2383 | 2021-10-29 17:19:14,284044 | TCP | 86 | [TCP Keep-Alive ACK] 80 → 60577 [ACK] Seq=940 Ack=434 Win=67584 Len=0 SLE=433 SRE=434 |
| 2400 | 2021-10-29 17:19:16,634769 | ICMPv6 | 70 | Router Solicitation from b4:69:21:fe:6c:cb |
| 2401 | 2021-10-29 17:19:16,642693 | ICMPv6 | 166 | Router Advertisement from 44:4e:6d:54:08:93 |
| 2402 | 2021-10-29 17:19:16,644814 | ICMPv6 | 166 | Router Advertisement from 44:4e:6d:54:08:93 |
Did you connect on the FritzBox or the FritzRepeater?
There are no DHCPv6 packets captured, so there isn't much to compare with the previous one.
With the repeater. I tried to catch more interesting information, hope it helps:
Obviously, OpenWrt is blocking some parts of the IPv6 traffic, right?
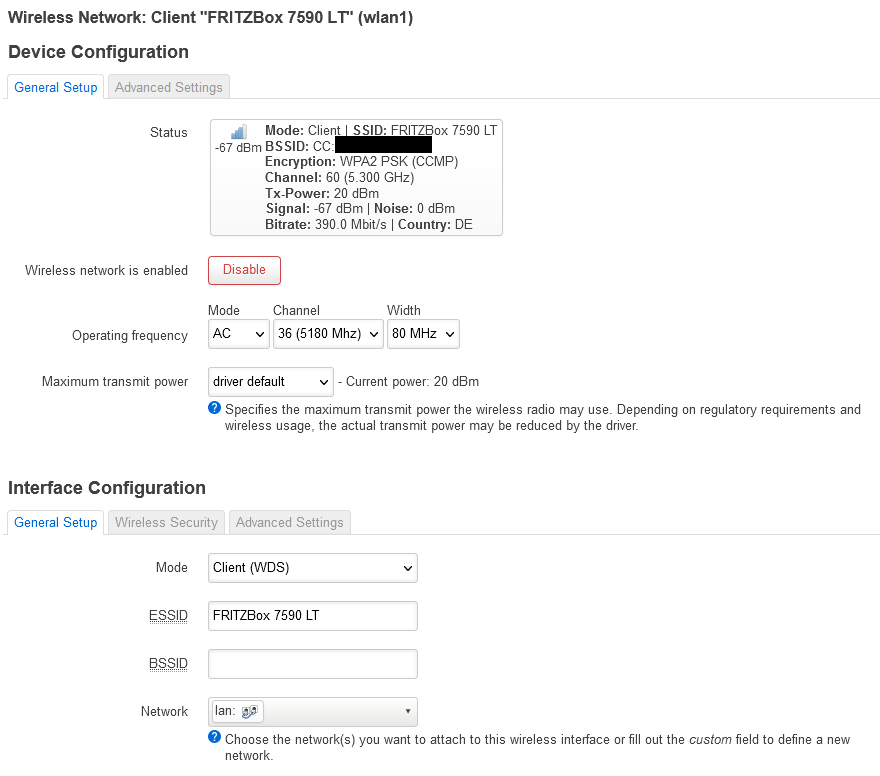
After some hours of googling around, I found out, that the Fritz!Box does not support WDS any longer 
Currently, my wireless network, which connects the repeater to the OpenWrt router, is set up in mode Client (WDS) Which mode should I choose instead? Does it break the bridge if I change the mode?
I had a closer look on the logs, as this is quite interesting case. It is weird that the windows do not continue the DHCP6 process and restart it after receiving the advertisement. Looking carefully at the contents of the packet, we can see that FritzBox doesn't actually offer any address (status-code NoAddrsAvail)
I would also not be surprised if the unanswered Router Solicitation has similar destiny.
That might be the reason behind it.
You should use station and it will break the bridge if you do.
Your option in this case is to delegate a prefix from the Fritz and use it in the lan of OpenWrt.
I'll try that, however I'm not quite sure how.
I've now configured my wireless network in mode "Client", so it acts as Access Point (which is a bit confusing from the naming). The OpenWrt router gets its IPv4 address and I have a stable connection to the main router. My PC, which should get the IPv6 address, is connected via cable to the OpenWrt router.
Some questions to prefix delegation, because I find the available descriptions extremly confusing ![]()
- For which interface do I have to maintain "IPv6 Settings"? LAN, WAN6, or both?
- Which settings do I have to choose for "RA-Service", "DHCPv6-Service" and "NDP-Proxy"?
- Which interface acts as master?
- Should WAN6 request IPv6 addresses? If yes, which length?
- What should be the "IPv6 assignment length" for the LAN interface.
My suggestion here is to reset to factory defaults and when you start from scratch you'll only have to setup the OpenWrt as a wireless client to the repeater.
By default, wan will use dhcp and wan6 will use dhcp6 and request a prefix from Fritz. So basically all of the configuration will be ready.
I've found a solution and it is desribed mostly in the User Guides. As prerequisite I had to istall relayd on the router, which is described here.
Findings
- I was not able to find a solution without lan/wlan bridging
- WDS bridging does not work, because FritzBox does not support WDS (any longer)
- Relayd supports IPv6
Addition: I've observed that the WDS bridge is about 30% faster than Relayd. So if you don't really need IPv6, you should go for WDS.
Pretty sure that was not the case before. When was that added?
WDS/ 4addr supports IPv6 transparently, relayd does not.