My ax3600 arrived now, maybe i can do the check. But i have no idea what should i do
You don't really need a physical one to extract the image, but I have the feeling that Xiaomi would have patched it since the image listed on the site is dated 4 days after the pppd vuln became public knowledge. (That and the Qualcomm SDK that they built off of... probably has mitigation in place.)
I can't be bothered checking since it's a little out of my price range and I can't get the ubifs extracted anyway.
As for RM2100 owners, here you go:
Replace the source/destination mac addresses and the interface, setup pppoe-server, and run when you see an active pppoe session between the router and your pc.
I think there's a watchdog that kills off pppd (and thus your shell) after a while, so I'd only probably use this to get your foot in the door and curl over a busybox binary to secure you proper access. (Ie. DO NOT DIRECTLY MTD WRITE YOUR OPENWRT IMAGES FROM THIS)
Should work on the black cylinder AC2100 (and anything older...) if you adjust the addresses of the rop gadgets and stuff.
Ok, here is the ubifs for ax3600, you can easily extracted with binwalk:
Otherwise, do you have a ARM version payload?
Anyone here who knows how I can get back to stock?
I want to test the exploit! I guess I can just flash the original kernel via tftp, boot it and send the original firmware via tftp. ???
Anyone willing to share the stock kernel.bin?
for your information: I am currently compiling a new OpenWrt version with kernel 5.4., will upload it as soon as I have tested it ...
thanks, but I think I need the kernel partition first. Is there an easy way of extracting it from the firmware image?
Here is kernel for Redmi AC2100: https://drive.google.com/open?id=1QBcKs6aIUWlMJ0Ngx1hg1d7iYuEaPJxe
What exploit you want to test? I can help you with this? Please give a solution, i have a Redmi AC2100 router.
thanks! I mean the one from @namidairo New Xiaomi Router AC2100
Great!
How can I get the values necessary from my ac2100 (rop gadgets addresses etc.)
Hi,
Did someone test if the BootRom DL Mode is disabled ?
The pppd binary, the libuclibc.so (Not strictly necessary but nice to have), and the memory map that gets spit out to messages when you crash it with a normal payload of all 'A' in the registers. (Assuming the mappings are different)
First two you can extract from the squashfs ín the ubifs image (assuming you can get ubireader to work, I never could and just used Percy's dumps), last one you can get from the device logs (192.168.31.1/....blahblahstok=something/api/misystem/sys_log)
There might be a little bit of messing around as I guessed the stack address by just going down by 0x200 until it landed somewhere in the nop sled.
I shouldn't have called it the AC2100 either, it's really the R2100 isn't it. Confusing model naming all round.
Yes, that's confusing. My ax3600 is also called R
3600. Could you please tell me how to confirm if this exploit is fixed in R3600? Unfortunately this is the only way which may get ssh access on 3600 now, because of the high price of a tosp-48 programer
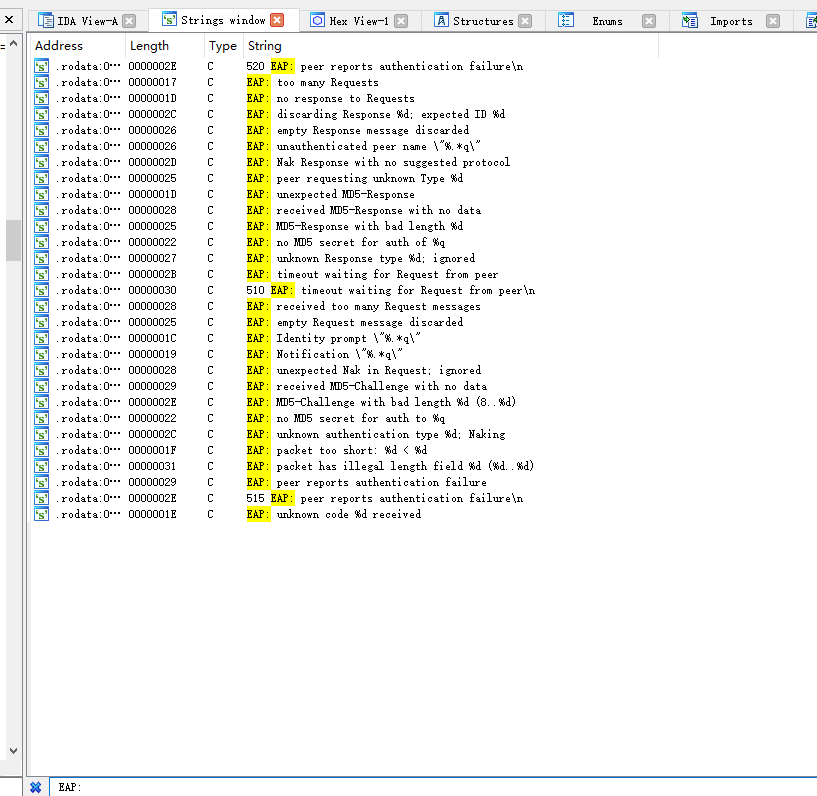
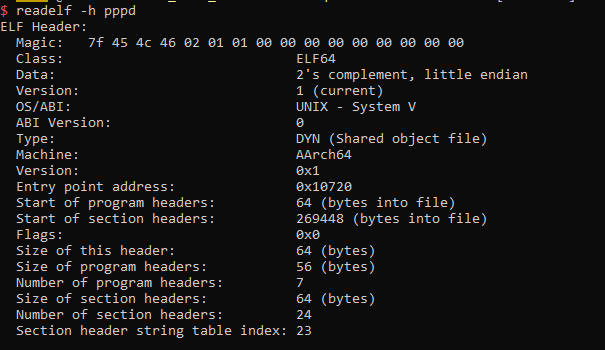
- Opening up the pppd binary and uclibc one in a disassembler.
- Checking that this hasn't been implemented yet https://github.com/paulusmack/ppp/commit/8d7970b8f3db727fe798b65f3377fe6787575426#diff-b7f5f2404cf3f5c09b1f8ad9364bb340
- Checking that bcopy/memcpy/memmove does not call a FORTIFY_SOURCE version
- Checking that they are not position independent executables.
- Crying if you find out they actually did do it properly by virtue of using Qualcomm's BSP?
- That's strange. I can't find this
eap_requestfunction, also the string:EAP: trimming really long peer name down
- Moreover, R3600 use musl not uclibc, i don't know how to check FORTIFY_SOURCE calling
- Sadly, it is PIE.
Maybe i can ready to cry??

The `pppd` and `libc.so` file: https://send.firefox.com/download/e042bee0081e2b04/#TTMmbHbGE9YUCZaJcAfwHw
Yeah, they have stack guards on in there too.
At least Qualcomm have shown to have their BSP up to date on their flagship chipsets... ![]() (The only reason it works on the ramips hardware is because they have pretty much every single mitigation turned off, no stack guards, no pie, rwx stacks, etc.)
(The only reason it works on the ramips hardware is because they have pretty much every single mitigation turned off, no stack guards, no pie, rwx stacks, etc.)
current master compiled for ac2100:
https://gofile.io/?c=LWjyIx
There are a couple things that I see in your patch that would probably need to be changed before doing a pull request and getting it supported properly.
Most of it should be covered here https://openwrt.org/submitting-patches
The stuff I spotted:
Do we need to rename the device? I'm not sure if we need a different DTS for the two devices since they're so very similar hardware wise. Probably just call the white one the RM2100 and the cylinder one R2100 like Xiaomi do? Check with one of the devs I guess
You have a duplicate DTS file that does nothing
Remember to preserve alphabetical order when you add the device to lists
memory@0 { device_type = "memory"; /*reg = <0x0 0x10000000>;256Mbyte*/ reg = <0x0 0x8000000>; };
I don't think this is needed anymore after https://github.com/openwrt/openwrt/commit/a2c19f1d2f658367e6d62a6bdcfc72f12f23e43e
`
lan3_amber {
label = "ac2100:amber:lan3";
gpios = <&gpio0 13 GPIO_ACTIVE_LOW>;
};
lan2_amber {
label = "ac2100:amber:lan2";
gpios = <&gpio0 16 GPIO_ACTIVE_LOW>;
};
lan1_amber {
label = "ac2100:amber:lan1";
gpios = <&gpio0 15 GPIO_ACTIVE_LOW>;
};`
I think these may require updates for DSA?
Eg. https://github.com/openwrt/openwrt/blob/master/target/linux/ramips/dts/mt7621_xiaomi_mir3p.dts#L46 and https://github.com/openwrt/openwrt/commit/30644bc579e771e4b6dcc165ca966124e0259e1e
License needs to be added to the top of the dts
The comments in the dts might need to be moved to the commit message?
And uhh, instructions to flash for those who manage to get root on stock?
Edit: I wrote "the white one and the white one", that makes no sense. Derp.
Have you managed to test exploit from @namidairo ? If yes, what is the result? I would like to try but do not know where to start... @namidairo, can you help me to test exploit?
Nope and I don't think I can test it in the near future as I need the router ...
I changed the necessary parts for DSA. I will post the patches later. Timewise I am quite restricted in the next days. In case somebody wants to take care of an PR feel free to do with my patches as I don't know when I will be able to do it ...