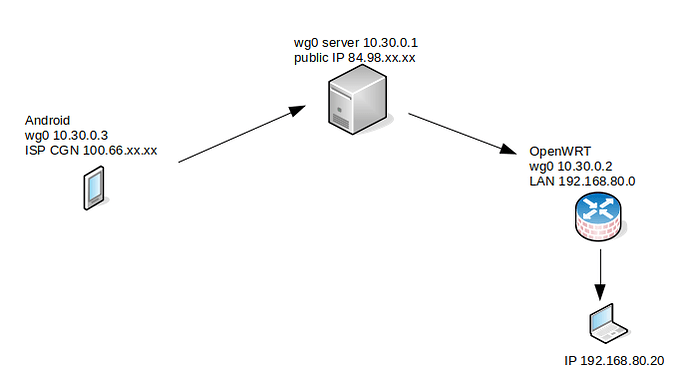
I need to get from my smartphone to LAN 192.168.80.0/24. I set up a wireguard on my smartphone, servers and router (openwrt). Now I get to 10.30.0.2 (LUCI OpenWRT) from my smartphone. I can't get to LAN 192.168.80.0/24.
How do I set up OpenWRT to have access from a smartphone to LAN 192.168.80.0/24.
This is certainly possible. Have you setup WG and gotten a general handshake?
Please post your config:
Please copy the output of the following commands and post it here using the "Preformatted text </> " button:
![]()
Remember to redact passwords, MAC addresses and any public IP addresses you may have:
cat /etc/config/network
cat /etc/config/firewall
I think wireguard works well on all devices (smartphone, server, router/openwrt)
This is the output from the server
interface: wg0
public key: CXOePGlyO***************FryOZm7+bBZXJ22p2DA=
private key: (hidden)
listening port: 51830
peer: 7mcbsTwkPL***************kU4Vum5rAVZ32fTKS8=
endpoint: xx.xx.xx.78:50366
allowed ips: 10.30.0.2/32
latest handshake: 51 seconds ago
transfer: 80.22 KiB received, 22.38 KiB sent
peer: 2puYaBPY5xEB64***************/iXJeg1P2ketQM=
endpoint: xx.xx.10.90:34325
allowed ips: 10.30.0.3/32
latest handshake: 2 minutes, 7 seconds ago
transfer: 7.93 KiB received, 2.46 KiB sent
cat /etc/config/network
config interface 'loopback'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
option device 'lo'
config globals 'globals'
option ula_prefix 'ffff:453f:66e4::/48'
config interface 'lan'
option proto 'static'
option netmask '255.255.255.0'
option ip6assign '60'
option device 'br-lan'
option ipaddr '192.168.80.1'
config device 'lan_dev'
option name 'eth0.1'
option macaddr 'ff:ff:18:a1:ac:ca'
config interface 'wan'
option proto 'dhcp'
option device 'eth0.2'
config device 'wan_dev'
option name 'eth0.2'
option macaddr 'ff:ff:18:a1:ac:cb'
config interface 'wan6'
option proto 'dhcpv6'
option device 'eth0.2'
config switch
option name 'switch0'
option reset '1'
option enable_vlan '1'
config switch_vlan
option device 'switch0'
option vlan '1'
option ports '1 2 3 4 6t'
config switch_vlan
option device 'switch0'
option vlan '2'
option ports '0 6t'
config device
option name 'br-lan'
option type 'bridge'
list ports 'eth0.1'
config interface 'wg0'
option proto 'wireguard'
option private_key 'qAfZrE6ZW***************exNHEm2rvq2jBwy1nXY='
list addresses '10.30.0.2/32'
config wireguard_wg0
option description 'server'
option public_key 'CXOePGlyO***************FryOZm7+bBZXJ22p2DA='
list allowed_ips '10.30.0.0/24'
option route_allowed_ips '1'
option endpoint_host 'example-host.com'
option endpoint_port '51030'
option persistent_keepalive '25'
config route
option target '192.168.80.0'
option netmask '255.255.255.0'
option gateway '192.168.80.1'
option interface 'wg0'
cat /etc/config/firewall
config defaults
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
option synflood_protect '1'
config zone
option name 'lan'
list network 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
config zone
option name 'wan'
list network 'wan'
list network 'wan6'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
config forwarding
option src 'lan'
option dest 'wan'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option src_ip 'fc00::/6'
option dest_ip 'fc00::/6'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config include
option path '/etc/firewall.user'
config redirect
option name 'luci-remote'
option src 'wan'
option proto 'tcp'
option src_dport '9999'
option dest_port '443'
option target 'DNAT'
option dest 'lan'
config zone
option name 'vpn'
option input 'ACCEPT'
option output 'ACCEPT'
list network 'wg0'
option forward 'REJECT'
config rule
option src wan
option dest_port 22
option target ACCEPT
option proto tcp
Mutual ping works 10.30.0.2 <--> 10.30.0.3
In the firewall add a config forwarding from vpn to lan. Or you could add wg0 to the lan zone instead of a separate zone.
The config looks fine, except for what @mk24 said about the firewall.
What does the Android device's WG config look like? Specifically the allowed IPs?
Finally, on the server at 84.98.xxx.xxx -- does that have a static route configured for 192.168.80.0/24? If it doesn't, it will need one added. The reason is that the server wouldn't otherwise know where to find 192.168.80.0/24... so you need to provide a static route of 192.168.80.0/24 via 10.3.0.2.
Wg settings on a smartphone
[Interface]
Address = 10.30.0.3/32
PrivateKey = mK6wKvd9Z********************wUU5bNVfyYiaH8=
[Peer]
PublicKey = CXOePGlyO***************FryOZm7+bBZXJ22p2DA=
AllowedIPs = 10.30.0.0/24,192.168.80.0/24
Endpoint = example-host.com:51830
PersistentKeepalive = 25
I added server routing to wg0.conf
PostUp = ip route add 192.168.80.0/24 dev wg0
PostDown = ip route del 192.168.80.0/24 dev wg0
Ping from your smartphone to 192.168.80.1
PING 192.168.80.1 (192.168.80.1) 56(84) bytes of data
From 10.30.0.1: icmp_seq=1 Destination Host Unreachable
From 10.30.0.1: icmp_seq=1 Destination Host Unreachable
I set up Openwrt like this
Remove this route. It doesn't do anything constructive and might mess things up.
And did you add the forwarding from vpn > lan as suggested by @mk24?
Try your ping test again. And also try pinging another host on the 192.168.80.0/24 network.
oh... sorry. That's good. I missed that in the previous screenshot. Yes, that's what you want.
However, I still can't get into the LAN
Ping from smartphone to LAN
PING 192.168.80.1 (192.168.80.1) 56(84) bytes of data
From 10.30.0.1: icmp_seq=1 Destination Host Unreachable
From 10.30.0.1: icmp_seq=1 Destination Host Unreachable
what about another host? not the router address.
There is nothing connected yet.
try connecting something and giving it a shot (if it is windows, make sure to turn off the firewall or adjust it so that it will accept connections from another subnet)
I connected to an openwrt router PC and tried to ping the IP PC 192.168.80.209 but the result is the same.
PING 192.168.80.209 (192.168.80.209) 56(84) bytes of data
From 10.30.0.1: icmp_seq=1 Destination Host Unreachable
From 10.30.0.1: icmp_seq=1 Destination Host Unreachable
Why is there a zone called wg and one called vpn? The diagram shows only three networks on the router on the right: lan, wan, and wireguard VPN.
If you put the wireguard interface/network into lan instead of a separate zone it should just work (forwarding must be enabled on the lan zone, which is the default). That is good to sort if it is a firewall situation or something else.
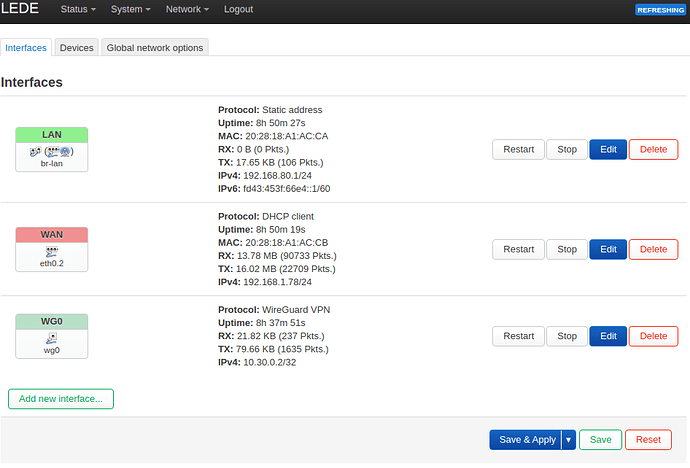
Now I have it this way
interfaces
zones
Ping from smartphone to LAN (192.168.80.0/24) does not work. If you ping from the server to the LAN, then the output
ping 192.168.80.1
PING 192.168.80.1 (192.168.80.1) 56(84) bytes of data.
From 10.30.0.1 icmp_seq=1 Destination Host Unreachable
ping: sendmsg: Required key not available
From 10.30.0.1 icmp_seq=2 Destination Host Unreachable
ping: sendmsg: Required key not available
From 10.30.0.1 icmp_seq=3 Destination Host Unreachable
ping: sendmsg: Required key not available
From 10.30.0.1 icmp_seq=4 Destination Host Unreachable
ping: sendmsg: Required key not available
The netmask size on the wg0 is wrong, it should be /24. Also the allowed_ips need to include the origin of the packets, which is the smartphone at 10.30.0.3, so set that to 10.30.0.0/24 as well.
You can (and should) use /32 for allowed_ips in the server's configuration of each client (plus any LANs that will be exported from that client.) But the overall wireguard tunnel network is a /24.
I'm pretty confused about that. ![]()
I don't know where I have anything to change. Everything seems to be set up well.
From the smartphone I get to 10.30.0.2 (OpenWRT LUCI). I can't connect to LAN 192.168.80.0/24.
It works now
I had to add the server to wg0.conf as well allowedips 192.168.80.0/24
[Peer]
PublicKey = 7mcbsTwkPL+C6***************Vum5rAVZ32fTKS8=
AllowedIPs = 192.168.80.0/24,10.30.0.2/32
I don't need to create a route to the server, because the wireguard will create it automatically.
10.30.0.2 dev wg0 scope link
10.30.0.3 dev wg0 scope link
192.168.30.0/24 dev eth0 proto kernel scope link src 192.168.30.10
192.168.80.0/24 dev wg0 scope link
This topic was automatically closed 10 days after the last reply. New replies are no longer allowed.