So.. what's left? what is the reason to completely disable IPv6 on the router and ignore (or just letting it pass without any way of knowing) any IPv6 traffic that my reach it?
Not fw4.
Not installed by default on fw4 devices.
- Nothing should pass; but
- You can disable IPv6 routing by sysctrl

net.ipv6.conf.all.forwarding
Not if you disable IPv6 "completely", as in, even at the kernel level, so that option does nothing.
And the switch will "switch" IPv6 packets just fine in any case. ![]()
Bottom line: even for "SOHO" every user should learn how to setup his dual stack network properly even if the main one is IPv4. Burying ones head in the sand when it comes to IPv6 doesn't solve anything.
IPv6 origin for WAN/Internet/ISP IP Addressing. The objective is not for SOHO/Intranet IP Addressing.
IPv4 enough to handle SOHO/Intranet IP Addressing.
Second Its all depends on usability and necessity.
Can we configure SOHO with IPv4? Ans is yes.
Do we need IPv6 to configure SOHO? Ans No, IPv4 enough.
For learning, yes its good to know both but when question is to implement, its all depends on "Requirement". If there is no Necessity of IPv6 why should we implement the same? Its about how to keep things. Simple/Complicate. Which is obviously a choice.
Can you try rephrasing that post? It doesn't make much sense.
I've got the implementation part, but don't worry, you don't have to implement anything as a user, you just have to turn off all IPv6 related options available in LuCI.
Now, each network admin needs to decide for their own network and set the desired policy. But in this context I would argue that going DualStack will allow IPv4-usage as already well known while also allowing small experiments with IPv6 so that once IPv6 becomes less optional the SOHO network does not need to do a cold transition. But again that is a matter of subjective taste and not of right or wrong.
What I personally like about IPv6 is that allowing remote access does not require any port games (one can restrict access to specific ports but one does not need to do so).
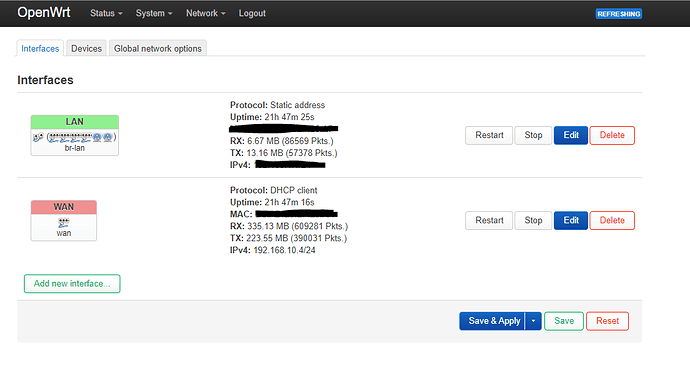
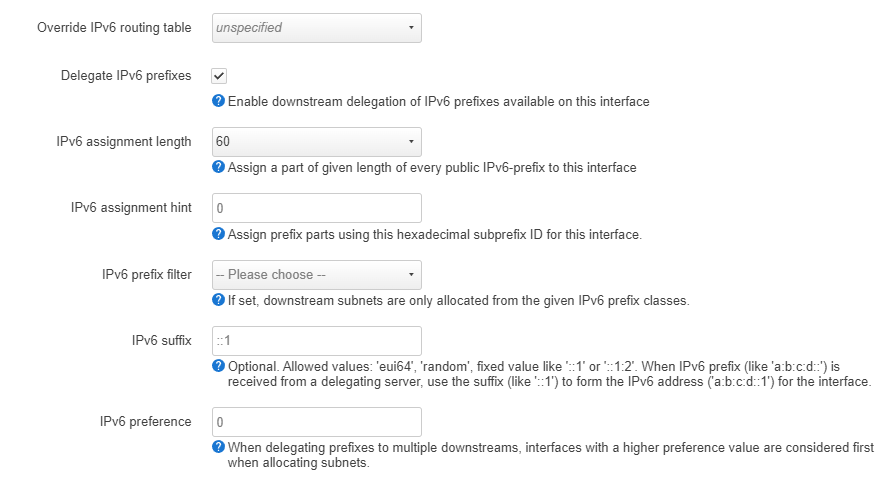
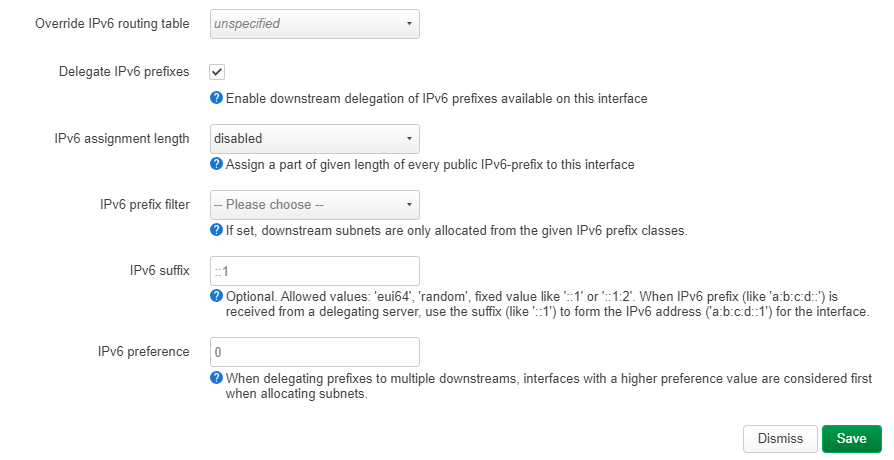
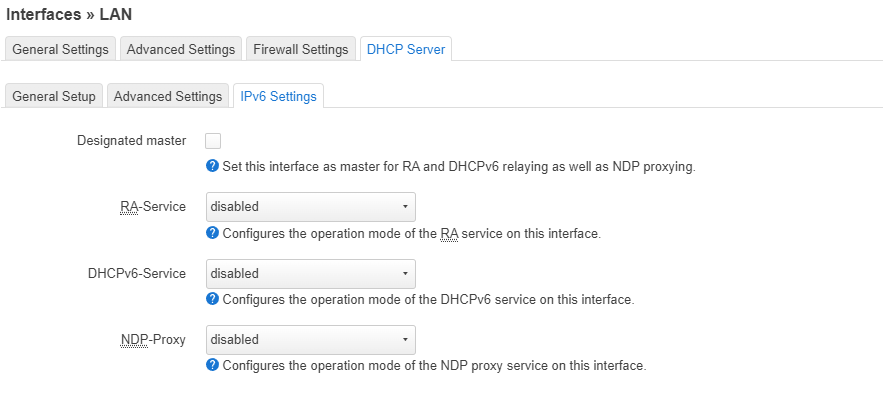
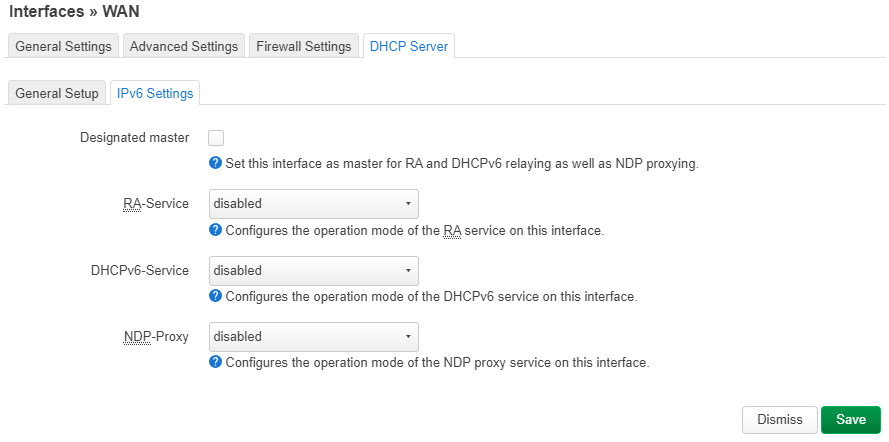
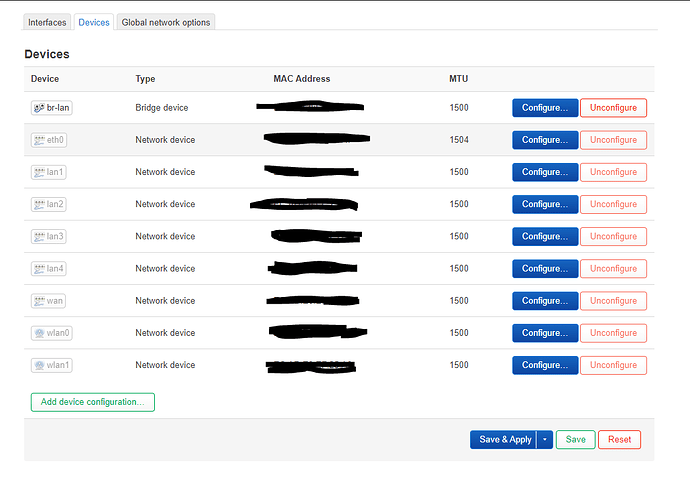
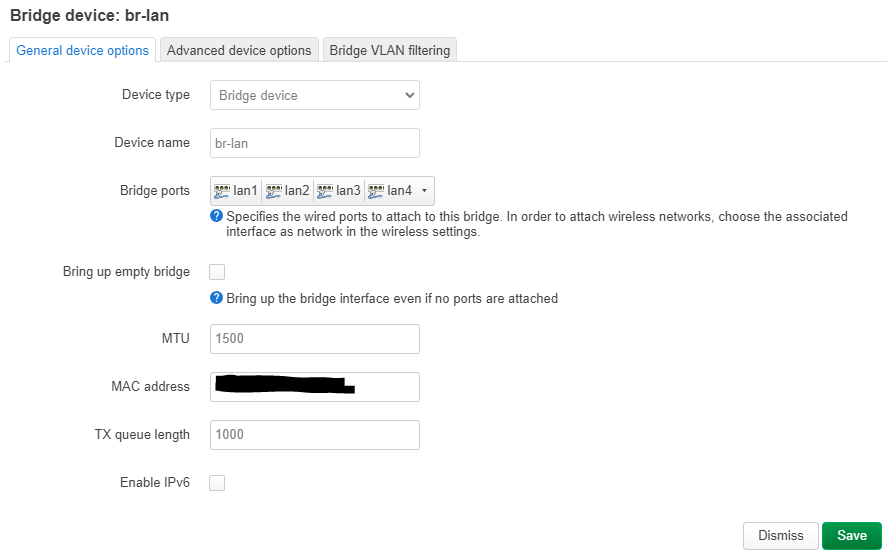
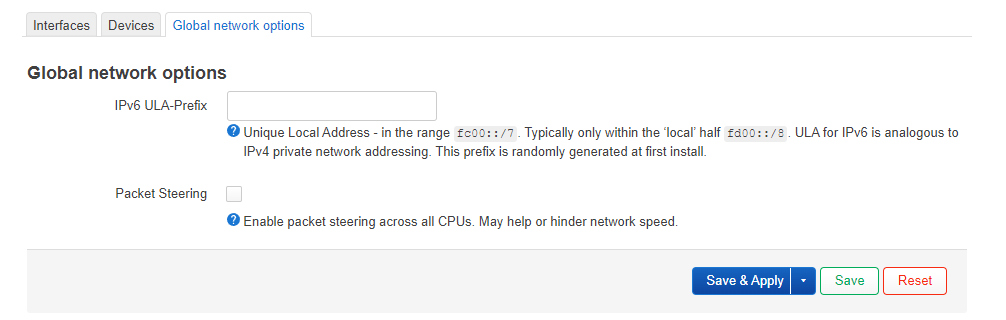
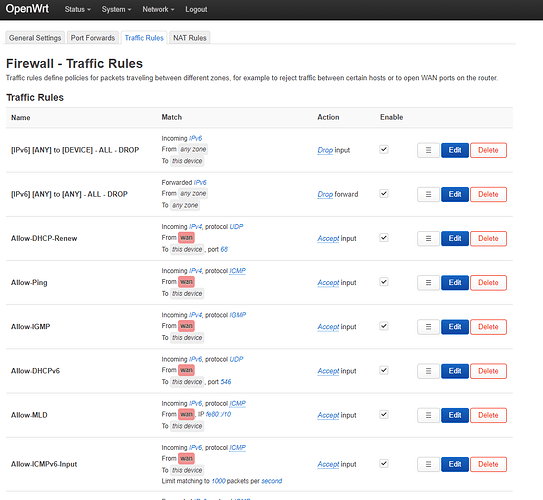
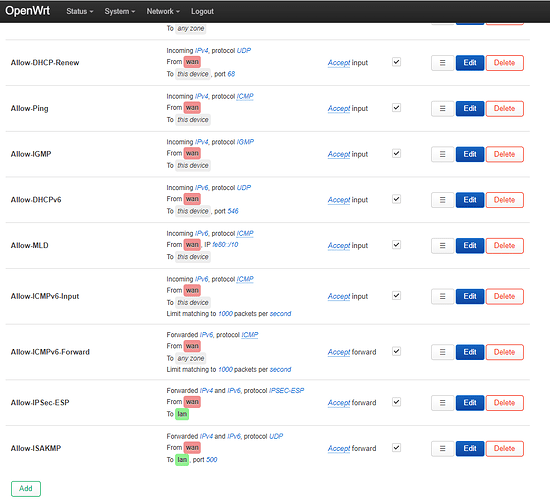
Already unchecked IPv6 and also added FW4 rules as per suggested by @open.nya
This is the current settings.
Now only thing is even after this configuration still this is remain.
ip add | grep t6
inet6 ::1/128 scope host
inet6 fe80::exad:e0ff:fxxf:25a7/64 scope link
inet6 fe80::exad:e0ff:fxxf:25aa/64 scope link
inet6 fe80::exad:e0ff:fxxf:25a9/64 scope link
inet6 fe80::exad:e0ff:fxxf:25a8/64 scope link
Hope someone gets you an IPv6 painting/t-shirt/something for your b-day.
Those are link local addresses, you can search on how you can disable link local address generation, if they bother you that much.
ISP Router is locked from ISP vendor.
NO to IPv6 haa. ![]()
never had luck get rid of ipv56 on new versions...phones still somehow push ipv6 traffic attempts
maybe they pull
Try this practical approach. The idea is that lan interface is usually stable. Once the v6 on lan is disabled that should cut off any v6 towards wan.
ip -6 add flush dev br-lan
No.
"For just 10 computers, IPv4 is enough". But that was back around end of 1970 we only had 10 computers on internet.
And IPv6 isn't used to solve the problem in your LAN, it is to solve problems over all.
And if you don't want to router IPv4, then turn of routeing of IPv4. If you want to connect to Internet, then you really should have IPv6. If you don't want or can't route IPv6, then just don't set global IPv6, and turn of IPv6 routing.
Short. There are NON real reason to turn of IPv6 in a router, whatever I have ever seen. If your device doesn't have IPv6, then it will use IPv4 without any problems. If it have IPv6, then it will use that without any problems. And a device with both IPv4 and IPv6 will use what needs to be used to reach other computers.
And IoT will be all IPv6, as that is the standards based on. And IPv4 is just a hack on top of those standards. So they don't need to implement IPv4, but they have to implement IPv6 to be a full fledged IoT device.
Ok, your points.
a) No, IPv6 is useful on any network, LAN and WAN. And most devices are dual stack.
b) It does work for both IPv4 and IPv6, so have you set it up for IPv4 then you also have that for IPv6. And you can always add mDNS your computers, and all are well. Both for IPv4 and IPv6.
b) Well, static IPv6 addresses can be made as easy to remember as IPv4.
That said, that your arguments are moot. Yes, you can just ignore IPv6, and you are done. Especially as devices are dual stack and can talk both IPv6 and IPv4.
But if you want to build your own version of OpenStack, then please do. Your computers and your time. But I should suggest that you just turn of routing of IPv6 and your are in all practical ways without IPv6 in your network.
No. If you turn of routing in your router, you will have no security problems with IPv6.
And all IPv6 can be ignored, you can use IPv4 addresses as you will.
Yes, ALL modern OS and devices uses IPv6 in the LAN, they are supposed and designed to do that. So yes, there are REALLY no reason to remove IPv6 support in OpenWRT. As that will complicate for everyone, including for you.
BUT if you use MS Windows, and remove IPv6 as you say, your MS Window machine can start to tunnel IPv6 for you.
Yes, in the router, do disable net.ipv6.conf.all.forwarding in sysctrl in Linux. Then it will not let out IPv6, and no need to look at IPv6 routing/firewall etc. All IPv6 will be local to your LAN.
Given the more or less unmitigated cluster-fsck that is IoT security (remember it is the s in IoT that stands for secure) this is actually an argument for IPv4 only....
Personally, I consider neither matter nor thread as a viable way forward to increase IoT security to an acceptable level, most of the involved industry players have great form in orphaning/abandoning working hard- and software products of theirs, so the likelihood of these players supporying either IoT hard- and/or software platforms for the lifetime of the IoT hardware is pretty small. This looks far from sustainable and environmentally sound....
Sorry for the rant, otherwise I agree that IPv4 only is not that wise a way forward.