Hello Greetings again friend:
I carried out the tests that you entrusted me again and I make a summary of the result, I will also attach below the requested configurations.
I just wanted to make a clarification that may serve to diagnose the problem.
As I mentioned, it is essential that the devices that are connected by WIFI Guest have access to the internet and to this particular URL https://secure.etecsa.net:8443
but in the same way if I ask for this IP http://1.1.1.1 this web responds to me https://secure.etecsa.net:8443 now what I wanted to clarify is that I don't know why when I ping https: // secure .etecsa.net: 8443 the IP 10.180.0.30 answers me. otherwise the IP 1.1.1.1 is protected and does not respond to ping.
Summary: if I ping from Putty or Luci from Diagnostics
Result: ping 10.180.0.30 ok
Ping secure.etecsa.net - bad address 'secure.etecsa.net'
From WIFI Guest
Result: ping 10.180.0.30 ok
Ping secure.etecsa.net - bad address 'secure.etecsa.net'
Now if I ping from PC1 and WAN bridge WIFI Test
Result: ping 10.180.0.30 ok
Ping secure.etecsa.net - ok
Conclusions: if I cannot ping secure.etecsa.net I cannot access the site https://secure.etecsa.net:8443
root@OpenWrt:~# uci export network; uci export wireless; \
>
package network
config interface 'loopback'
option ifname 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fd05:2d31:65c0::/48'
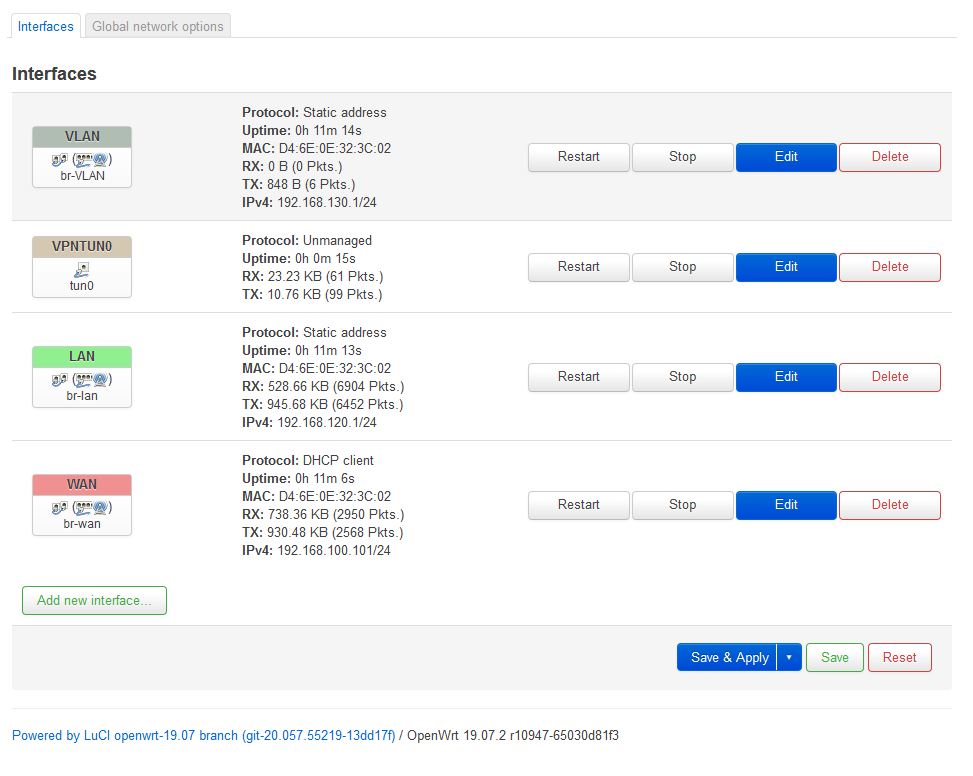
config interface 'lan'
option type 'bridge'
option ifname 'eth0.1'
option proto 'static'
option netmask '255.255.255.0'
option ipaddr '192.168.120.1'
config interface 'wan'
option ifname 'eth0.2'
option proto 'dhcp'
option type 'bridge'
option delegate '0'
config switch
option name 'switch0'
option reset '1'
option enable_vlan '1'
config switch_vlan
option device 'switch0'
option vlan '1'
option vid '1'
option ports '0t 4'
config switch_vlan
option device 'switch0'
option vlan '2'
option vid '2'
option ports '0t 5'
config interface 'VPNtun0'
option ifname 'tun0'
option proto 'none'
config switch_vlan
option device 'switch0'
option vlan '3'
option vid '3'
option ports '0t 4t'
config interface 'VLAN'
option ifname 'eth0.3'
option proto 'static'
option netmask '255.255.255.0'
option ipaddr '192.168.130.1'
option type 'bridge'
package wireless
config wifi-device 'radio0'
option type 'mac80211'
option hwmode '11g'
option path 'platform/ar934x_wmac'
option htmode 'HT20'
option txpower '23'
option country 'US'
option channel '6'
config wifi-iface 'wifinet1'
option device 'radio0'
option mode 'ap'
option key '123456789'
option encryption 'psk2'
option network 'wan'
option ssid 'test'
config wifi-iface 'wifinet2'
option encryption 'psk2'
option device 'radio0'
option mode 'ap'
option network 'lan'
option key '12346587'
option ssid 'myjob'
config wifi-iface 'wifinet3'
option encryption 'none'
option device 'radio0'
option mode 'ap'
option network 'VLAN'
option ssid 'Guest'
root@OpenWrt:~# uci export dhcp; uci export firewall; \
>
package dhcp
config dnsmasq
option domainneeded '1'
option localise_queries '1'
option rebind_protection '1'
option rebind_localhost '1'
option local '/lan/'
option domain 'lan'
option expandhosts '1'
option authoritative '1'
option readethers '1'
option leasefile '/tmp/dhcp.leases'
option localservice '1'
option logqueries '1'
option resolvfile '/tmp/resolv.conf.auto'
config dhcp 'lan'
option interface 'lan'
option start '100'
option limit '150'
option dhcpv6 'server'
option ra 'server'
option ra_management '1'
option leasetime '12h'
config dhcp 'wan'
option interface 'wan'
option ignore '1'
config odhcpd 'odhcpd'
option maindhcp '0'
option leasefile '/tmp/hosts/odhcpd'
option leasetrigger '/usr/sbin/odhcpd-update'
option loglevel '4'
config dhcp 'LAN1'
option interface 'LAN1'
option start '100'
option leasetime '12h'
option limit '150'
config dhcp 'VLAN1'
option start '100'
option leasetime '12h'
option limit '150'
option interface 'VLAN1'
config dhcp 'VLAN'
option start '100'
option leasetime '12h'
option limit '150'
option interface 'VLAN'
package firewall
config defaults
option syn_flood '1'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
config zone
option name 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
option network 'lan'
config zone
option name 'wan'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
option input 'ACCEPT'
option network 'wan'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option src_ip 'fc00::/6'
option dest_ip 'fc00::/6'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config include
option path '/etc/firewall.user'
config zone
option network 'VPN_zone VPNtun0'
option name 'VPN_zone'
option mtu_fix '1'
option input 'REJECT'
option forward 'REJECT'
option masq '1'
option output 'ACCEPT'
config forwarding
option dest 'VPN_zone'
option src 'lan'
config forwarding
option dest 'VPN_zone'
option src 'wan'
config forwarding
option dest 'wan'
option src 'VLAN'
config forwarding
option dest 'wan'
option src 'VLAN1'
config forwarding
option dest 'VLAN1'
option src 'Wan'
config zone
option name 'VLAN_zona'
option input 'ACCEPT'
option network 'VLAN_zona VLAN'
option output 'ACCEPT'
option forward 'ACCEPT'
option masq '1'
config forwarding
option dest 'wan'
option src 'VLAN_zona'
config zone
option name 'WAN'
option input 'ACCEPT'
option network 'WAN wan'
option output 'ACCEPT'
option forward 'ACCEPT'
option masq '1'
config forwarding
option dest 'VLAN_zona'
option src 'wan'
config forwarding
option dest 'VLAN_zona'
option src 'WAN'
root@OpenWrt:~# head -n -0 /etc/firewall.user; \
>
# This file is interpreted as shell script.
# Put your custom iptables rules here, they will
# be executed with each firewall (re-)start.
# Internal uci firewall chains are flushed and recreated on reload, so
# put custom rules into the root chains e.g. INPUT or FORWARD or into the
# special user chains, e.g. input_wan_rule or postrouting_lan_rule.
root@OpenWrt:~#
root@OpenWrt:~# ip -4 addr ; ip -4 ro li tab all ; ip -4 ru; \
>
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1000
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
4: br-VLAN: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP qlen 1000
inet 192.168.130.1/24 brd 192.168.130.255 scope global br-VLAN
valid_lft forever preferred_lft forever
6: br-lan: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP qlen 1000
inet 192.168.120.1/24 brd 192.168.120.255 scope global br-lan
valid_lft forever preferred_lft forever
8: br-wan: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP qlen 1000
inet 192.168.100.101/24 brd 192.168.100.255 scope global br-wan
valid_lft forever preferred_lft forever
default via 192.168.100.100 dev br-wan src 192.168.100.101
192.168.100.0/24 dev br-wan scope link src 192.168.100.101
192.168.120.0/24 dev br-lan scope link src 192.168.120.1
192.168.130.0/24 dev br-VLAN scope link src 192.168.130.1
broadcast 127.0.0.0 dev lo table local scope link src 127.0.0.1
local 127.0.0.0/8 dev lo table local scope host src 127.0.0.1
local 127.0.0.1 dev lo table local scope host src 127.0.0.1
broadcast 127.255.255.255 dev lo table local scope link src 127.0.0.1
broadcast 192.168.100.0 dev br-wan table local scope link src 192.168.100.101
local 192.168.100.101 dev br-wan table local scope host src 192.168.100.101
broadcast 192.168.100.255 dev br-wan table local scope link src 192.168.100.101
broadcast 192.168.120.0 dev br-lan table local scope link src 192.168.120.1
local 192.168.120.1 dev br-lan table local scope host src 192.168.120.1
broadcast 192.168.120.255 dev br-lan table local scope link src 192.168.120.1
broadcast 192.168.130.0 dev br-VLAN table local scope link src 192.168.130.1
local 192.168.130.1 dev br-VLAN table local scope host src 192.168.130.1
broadcast 192.168.130.255 dev br-VLAN table local scope link src 192.168.130.1
0: from all lookup local
32766: from all lookup main
32767: from all lookup default
root@OpenWrt:~# ip -6 addr ; ip -6 ro li tab all ; ip -6 ru; \
>
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 state UNKNOWN qlen 1000
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 state UP qlen 1000
inet6 fe80::d66e:eff:fe32:3c02/64 scope link
valid_lft forever preferred_lft forever
4: br-VLAN: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 state UP qlen 1000
inet6 fe80::d66e:eff:fe32:3c02/64 scope link
valid_lft forever preferred_lft forever
6: br-lan: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 state UP qlen 1000
inet6 fe80::d66e:eff:fe32:3c02/64 scope link
valid_lft forever preferred_lft forever
8: br-wan: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 state UP qlen 1000
inet6 fe80::d66e:eff:fe32:3c02/64 scope link
valid_lft forever preferred_lft forever
10: wlan0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 state UP qlen 1000
inet6 fe80::d66e:eff:fe32:3c02/64 scope link
valid_lft forever preferred_lft forever
11: wlan0-1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 state UP qlen 1000
inet6 fe80::d46e:eff:fe32:3c02/64 scope link
valid_lft forever preferred_lft forever
12: wlan0-2: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 state UP qlen 1000
inet6 fe80::d06e:eff:fe32:3c02/64 scope link
valid_lft forever preferred_lft forever
unreachable fd05:2d31:65c0::/48 dev lo metric 2147483647 error -148
fe80::/64 dev eth0 metric 256
fe80::/64 dev br-lan metric 256
fe80::/64 dev br-wan metric 256
fe80::/64 dev br-VLAN metric 256
fe80::/64 dev wlan0 metric 256
fe80::/64 dev wlan0-1 metric 256
fe80::/64 dev wlan0-2 metric 256
local ::1 dev lo table local metric 0
anycast fe80:: dev br-lan table local metric 0
anycast fe80:: dev eth0 table local metric 0
anycast fe80:: dev br-wan table local metric 0
anycast fe80:: dev br-VLAN table local metric 0
anycast fe80:: dev wlan0 table local metric 0
anycast fe80:: dev wlan0-2 table local metric 0
anycast fe80:: dev wlan0-1 table local metric 0
local fe80::d06e:eff:fe32:3c02 dev wlan0-2 table local metric 0
local fe80::d46e:eff:fe32:3c02 dev wlan0-1 table local metric 0
local fe80::d66e:eff:fe32:3c02 dev br-lan table local metric 0
local fe80::d66e:eff:fe32:3c02 dev eth0 table local metric 0
local fe80::d66e:eff:fe32:3c02 dev br-wan table local metric 0
local fe80::d66e:eff:fe32:3c02 dev br-VLAN table local metric 0
local fe80::d66e:eff:fe32:3c02 dev wlan0 table local metric 0
ff00::/8 dev eth0 table local metric 256
ff00::/8 dev br-lan table local metric 256
ff00::/8 dev br-wan table local metric 256
ff00::/8 dev br-VLAN table local metric 256
ff00::/8 dev wlan0 table local metric 256
ff00::/8 dev wlan0-1 table local metric 256
ff00::/8 dev wlan0-2 table local metric 256
0: from all lookup local
32766: from all lookup main
4200000001: from all iif lo lookup unspec 12
4200000004: from all iif br-VLAN lookup unspec 12
4200000006: from all iif br-lan lookup unspec 12
4200000008: from all iif br-wan lookup unspec 12
root@OpenWrt:~# ls -l /etc/resolv.* /tmp/resolv.*; head -n -0 /etc/resolv.* /tmp/resolv.*
lrwxrwxrwx 1 root root 16 Feb 27 16:05 /etc/resolv.conf -> /tmp/resolv.conf
-rw-r--r-- 1 root root 32 May 7 20:33 /tmp/resolv.conf
-rw-r--r-- 1 root root 70 May 7 20:33 /tmp/resolv.conf.auto
==> /etc/resolv.conf <==
search lan
nameserver 127.0.0.1
==> /tmp/resolv.conf <==
search lan
nameserver 127.0.0.1
==> /tmp/resolv.conf.auto <==
# Interface wan
nameserver 192.168.100.100
nameserver 192.168.100.100
root@OpenWrt:~# iptables-save -c;
# Generated by iptables-save v1.8.3 on Thu May 7 22:01:56 2020
*nat
:PREROUTING ACCEPT [1201:114250]
:INPUT ACCEPT [216:14649]
:OUTPUT ACCEPT [409:29183]
:POSTROUTING ACCEPT [101:6897]
:postrouting_VLAN_zona_rule - [0:0]
:postrouting_VPN_zone_rule - [0:0]
:postrouting_WAN_rule - [0:0]
:postrouting_lan_rule - [0:0]
:postrouting_rule - [0:0]
:postrouting_wan_rule - [0:0]
:prerouting_VLAN_zona_rule - [0:0]
:prerouting_VPN_zone_rule - [0:0]
:prerouting_WAN_rule - [0:0]
:prerouting_lan_rule - [0:0]
:prerouting_rule - [0:0]
:prerouting_wan_rule - [0:0]
:zone_VLAN_zona_postrouting - [0:0]
:zone_VLAN_zona_prerouting - [0:0]
:zone_VPN_zone_postrouting - [0:0]
:zone_VPN_zone_prerouting - [0:0]
:zone_WAN_postrouting - [0:0]
:zone_WAN_prerouting - [0:0]
:zone_lan_postrouting - [0:0]
:zone_lan_prerouting - [0:0]
:zone_wan_postrouting - [0:0]
:zone_wan_prerouting - [0:0]
[1201:114250] -A PREROUTING -m comment --comment "!fw3: Custom prerouting rule chain" -j prerouting_rule
[0:0] -A PREROUTING -i br-lan -m comment --comment "!fw3" -j zone_lan_prerouting
[421:52555] -A PREROUTING -i br-wan -m comment --comment "!fw3" -j zone_wan_prerouting
[0:0] -A PREROUTING -i tun0 -m comment --comment "!fw3" -j zone_VPN_zone_prerouting
[780:61695] -A PREROUTING -i br-VLAN -m comment --comment "!fw3" -j zone_VLAN_zona_prerouting
[421:52555] -A PREROUTING -i br-wan -m comment --comment "!fw3" -j zone_WAN_prerouting
[852:65723] -A POSTROUTING -m comment --comment "!fw3: Custom postrouting rule chain" -j postrouting_rule
[0:0] -A POSTROUTING -o br-lan -m comment --comment "!fw3" -j zone_lan_postrouting
[748:58110] -A POSTROUTING -o br-wan -m comment --comment "!fw3" -j zone_wan_postrouting
[0:0] -A POSTROUTING -o tun0 -m comment --comment "!fw3" -j zone_VPN_zone_postrouting
[3:716] -A POSTROUTING -o br-VLAN -m comment --comment "!fw3" -j zone_VLAN_zona_postrouting
[0:0] -A POSTROUTING -o br-wan -m comment --comment "!fw3" -j zone_WAN_postrouting
[3:716] -A zone_VLAN_zona_postrouting -m comment --comment "!fw3: Custom VLAN_zona postrouting rule chain" -j postrouting_VLAN_zona_rule
[3:716] -A zone_VLAN_zona_postrouting -m comment --comment "!fw3" -j MASQUERADE
[780:61695] -A zone_VLAN_zona_prerouting -m comment --comment "!fw3: Custom VLAN_zona prerouting rule chain" -j prerouting_VLAN_zona_rule
[0:0] -A zone_VPN_zone_postrouting -m comment --comment "!fw3: Custom VPN_zone postrouting rule chain" -j postrouting_VPN_zone_rule
[0:0] -A zone_VPN_zone_postrouting -m comment --comment "!fw3" -j MASQUERADE
[0:0] -A zone_VPN_zone_prerouting -m comment --comment "!fw3: Custom VPN_zone prerouting rule chain" -j prerouting_VPN_zone_rule
[0:0] -A zone_WAN_postrouting -m comment --comment "!fw3: Custom WAN postrouting rule chain" -j postrouting_WAN_rule
[0:0] -A zone_WAN_postrouting -m comment --comment "!fw3" -j MASQUERADE
[421:52555] -A zone_WAN_prerouting -m comment --comment "!fw3: Custom WAN prerouting rule chain" -j prerouting_WAN_rule
[0:0] -A zone_lan_postrouting -m comment --comment "!fw3: Custom lan postrouting rule chain" -j postrouting_lan_rule
[0:0] -A zone_lan_prerouting -m comment --comment "!fw3: Custom lan prerouting rule chain" -j prerouting_lan_rule
[748:58110] -A zone_wan_postrouting -m comment --comment "!fw3: Custom wan postrouting rule chain" -j postrouting_wan_rule
[748:58110] -A zone_wan_postrouting -m comment --comment "!fw3" -j MASQUERADE
[421:52555] -A zone_wan_prerouting -m comment --comment "!fw3: Custom wan prerouting rule chain" -j prerouting_wan_rule
COMMIT
# Completed on Thu May 7 22:01:56 2020
# Generated by iptables-save v1.8.3 on Thu May 7 22:01:56 2020
*mangle
:PREROUTING ACCEPT [3984:526783]
:INPUT ACCEPT [2305:357595]
:FORWARD ACCEPT [1137:106127]
:OUTPUT ACCEPT [2460:592940]
:POSTROUTING ACCEPT [3600:700075]
[761:39668] -A FORWARD -o br-wan -p tcp -m tcp --tcp-flags SYN,RST SYN -m comment --comment "!fw3: Zone wan MTU fixing" -j TCPMSS --clamp-mss-to-pmtu
[0:0] -A FORWARD -o tun0 -p tcp -m tcp --tcp-flags SYN,RST SYN -m comment --comment "!fw3: Zone VPN_zone MTU fixing" -j TCPMSS --clamp-mss-to-pmtu
COMMIT
# Completed on Thu May 7 22:01:56 2020
# Generated by iptables-save v1.8.3 on Thu May 7 22:01:56 2020
*filter
:INPUT ACCEPT [0:0]
:FORWARD DROP [0:0]
:OUTPUT ACCEPT [0:0]
:forwarding_VLAN_zona_rule - [0:0]
:forwarding_VPN_zone_rule - [0:0]
:forwarding_WAN_rule - [0:0]
:forwarding_lan_rule - [0:0]
:forwarding_rule - [0:0]
:forwarding_wan_rule - [0:0]
:input_VLAN_zona_rule - [0:0]
:input_VPN_zone_rule - [0:0]
:input_WAN_rule - [0:0]
:input_lan_rule - [0:0]
:input_rule - [0:0]
:input_wan_rule - [0:0]
:output_VLAN_zona_rule - [0:0]
:output_VPN_zone_rule - [0:0]
:output_WAN_rule - [0:0]
:output_lan_rule - [0:0]
:output_rule - [0:0]
:output_wan_rule - [0:0]
:reject - [0:0]
:syn_flood - [0:0]
:zone_VLAN_zona_dest_ACCEPT - [0:0]
:zone_VLAN_zona_forward - [0:0]
:zone_VLAN_zona_input - [0:0]
:zone_VLAN_zona_output - [0:0]
:zone_VLAN_zona_src_ACCEPT - [0:0]
:zone_VPN_zone_dest_ACCEPT - [0:0]
:zone_VPN_zone_dest_REJECT - [0:0]
:zone_VPN_zone_forward - [0:0]
:zone_VPN_zone_input - [0:0]
:zone_VPN_zone_output - [0:0]
:zone_VPN_zone_src_REJECT - [0:0]
:zone_WAN_dest_ACCEPT - [0:0]
:zone_WAN_forward - [0:0]
:zone_WAN_input - [0:0]
:zone_WAN_output - [0:0]
:zone_WAN_src_ACCEPT - [0:0]
:zone_lan_dest_ACCEPT - [0:0]
:zone_lan_forward - [0:0]
:zone_lan_input - [0:0]
:zone_lan_output - [0:0]
:zone_lan_src_ACCEPT - [0:0]
:zone_wan_dest_ACCEPT - [0:0]
:zone_wan_dest_REJECT - [0:0]
:zone_wan_forward - [0:0]
:zone_wan_input - [0:0]
:zone_wan_output - [0:0]
:zone_wan_src_ACCEPT - [0:0]
[458:79826] -A INPUT -i lo -m comment --comment "!fw3" -j ACCEPT
[1850:277889] -A INPUT -m comment --comment "!fw3: Custom input rule chain" -j input_rule
[1428:244395] -A INPUT -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
[78:4056] -A INPUT -p tcp -m tcp --tcp-flags FIN,SYN,RST,ACK SYN -m comment --comment "!fw3" -j syn_flood
[0:0] -A INPUT -i br-lan -m comment --comment "!fw3" -j zone_lan_input
[176:14110] -A INPUT -i br-wan -m comment --comment "!fw3" -j zone_wan_input
[0:0] -A INPUT -i tun0 -m comment --comment "!fw3" -j zone_VPN_zone_input
[246:19384] -A INPUT -i br-VLAN -m comment --comment "!fw3" -j zone_VLAN_zona_input
[0:0] -A INPUT -i br-wan -m comment --comment "!fw3" -j zone_WAN_input
[1137:106127] -A FORWARD -m comment --comment "!fw3: Custom forwarding rule chain" -j forwarding_rule
[174:40575] -A FORWARD -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
[0:0] -A FORWARD -i br-lan -m comment --comment "!fw3" -j zone_lan_forward
[0:0] -A FORWARD -i br-wan -m comment --comment "!fw3" -j zone_wan_forward
[0:0] -A FORWARD -i tun0 -m comment --comment "!fw3" -j zone_VPN_zone_forward
[963:65552] -A FORWARD -i br-VLAN -m comment --comment "!fw3" -j zone_VLAN_zona_forward
[0:0] -A FORWARD -i br-wan -m comment --comment "!fw3" -j zone_WAN_forward
[0:0] -A FORWARD -m comment --comment "!fw3" -j reject
[650:110458] -A OUTPUT -o lo -m comment --comment "!fw3" -j ACCEPT
[1815:483454] -A OUTPUT -m comment --comment "!fw3: Custom output rule chain" -j output_rule
[1433:455881] -A OUTPUT -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
[0:0] -A OUTPUT -o br-lan -m comment --comment "!fw3" -j zone_lan_output
[378:26517] -A OUTPUT -o br-wan -m comment --comment "!fw3" -j zone_wan_output
[0:0] -A OUTPUT -o tun0 -m comment --comment "!fw3" -j zone_VPN_zone_output
[4:1056] -A OUTPUT -o br-VLAN -m comment --comment "!fw3" -j zone_VLAN_zona_output
[0:0] -A OUTPUT -o br-wan -m comment --comment "!fw3" -j zone_WAN_output
[0:0] -A reject -p tcp -m comment --comment "!fw3" -j REJECT --reject-with tcp-reset
[0:0] -A reject -m comment --comment "!fw3" -j REJECT --reject-with icmp-port-unreachable
[78:4056] -A syn_flood -p tcp -m tcp --tcp-flags FIN,SYN,RST,ACK SYN -m limit --limit 25/sec --limit-burst 50 -m comment --comment "!fw3" -j RETURN
[0:0] -A syn_flood -m comment --comment "!fw3" -j DROP
[0:0] -A zone_VLAN_zona_dest_ACCEPT -o br-VLAN -m conntrack --ctstate INVALID -m comment --comment "!fw3: Prevent NAT leakage" -j DROP
[4:1056] -A zone_VLAN_zona_dest_ACCEPT -o br-VLAN -m comment --comment "!fw3" -j ACCEPT
[963:65552] -A zone_VLAN_zona_forward -m comment --comment "!fw3: Custom VLAN_zona forwarding rule chain" -j forwarding_VLAN_zona_rule
[963:65552] -A zone_VLAN_zona_forward -m comment --comment "!fw3: Zone VLAN_zona to wan forwarding policy" -j zone_wan_dest_ACCEPT
[0:0] -A zone_VLAN_zona_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[0:0] -A zone_VLAN_zona_forward -m comment --comment "!fw3" -j zone_VLAN_zona_dest_ACCEPT
[246:19384] -A zone_VLAN_zona_input -m comment --comment "!fw3: Custom VLAN_zona input rule chain" -j input_VLAN_zona_rule
[0:0] -A zone_VLAN_zona_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[246:19384] -A zone_VLAN_zona_input -m comment --comment "!fw3" -j zone_VLAN_zona_src_ACCEPT
[4:1056] -A zone_VLAN_zona_output -m comment --comment "!fw3: Custom VLAN_zona output rule chain" -j output_VLAN_zona_rule
[4:1056] -A zone_VLAN_zona_output -m comment --comment "!fw3" -j zone_VLAN_zona_dest_ACCEPT
[246:19384] -A zone_VLAN_zona_src_ACCEPT -i br-VLAN -m conntrack --ctstate NEW,UNTRACKED -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_VPN_zone_dest_ACCEPT -o tun0 -m conntrack --ctstate INVALID -m comment --comment "!fw3: Prevent NAT leakage" -j DROP
[0:0] -A zone_VPN_zone_dest_ACCEPT -o tun0 -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_VPN_zone_dest_REJECT -o tun0 -m comment --comment "!fw3" -j reject
[0:0] -A zone_VPN_zone_forward -m comment --comment "!fw3: Custom VPN_zone forwarding rule chain" -j forwarding_VPN_zone_rule
[0:0] -A zone_VPN_zone_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[0:0] -A zone_VPN_zone_forward -m comment --comment "!fw3" -j zone_VPN_zone_dest_REJECT
[0:0] -A zone_VPN_zone_input -m comment --comment "!fw3: Custom VPN_zone input rule chain" -j input_VPN_zone_rule
[0:0] -A zone_VPN_zone_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[0:0] -A zone_VPN_zone_input -m comment --comment "!fw3" -j zone_VPN_zone_src_REJECT
[0:0] -A zone_VPN_zone_output -m comment --comment "!fw3: Custom VPN_zone output rule chain" -j output_VPN_zone_rule
[0:0] -A zone_VPN_zone_output -m comment --comment "!fw3" -j zone_VPN_zone_dest_ACCEPT
[0:0] -A zone_VPN_zone_src_REJECT -i tun0 -m comment --comment "!fw3" -j reject
[0:0] -A zone_WAN_dest_ACCEPT -o br-wan -m conntrack --ctstate INVALID -m comment --comment "!fw3: Prevent NAT leakage" -j DROP
[0:0] -A zone_WAN_dest_ACCEPT -o br-wan -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_WAN_forward -m comment --comment "!fw3: Custom WAN forwarding rule chain" -j forwarding_WAN_rule
[0:0] -A zone_WAN_forward -m comment --comment "!fw3: Zone WAN to VLAN_zona forwarding policy" -j zone_VLAN_zona_dest_ACCEPT
[0:0] -A zone_WAN_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[0:0] -A zone_WAN_forward -m comment --comment "!fw3" -j zone_WAN_dest_ACCEPT
[0:0] -A zone_WAN_input -m comment --comment "!fw3: Custom WAN input rule chain" -j input_WAN_rule
[0:0] -A zone_WAN_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[0:0] -A zone_WAN_input -m comment --comment "!fw3" -j zone_WAN_src_ACCEPT
[0:0] -A zone_WAN_output -m comment --comment "!fw3: Custom WAN output rule chain" -j output_WAN_rule
[0:0] -A zone_WAN_output -m comment --comment "!fw3" -j zone_WAN_dest_ACCEPT
[0:0] -A zone_WAN_src_ACCEPT -i br-wan -m conntrack --ctstate NEW,UNTRACKED -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_lan_dest_ACCEPT -o br-lan -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_lan_forward -m comment --comment "!fw3: Custom lan forwarding rule chain" -j forwarding_lan_rule
[0:0] -A zone_lan_forward -m comment --comment "!fw3: Zone lan to VPN_zone forwarding policy" -j zone_VPN_zone_dest_ACCEPT
[0:0] -A zone_lan_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[0:0] -A zone_lan_forward -m comment --comment "!fw3" -j zone_lan_dest_ACCEPT
[0:0] -A zone_lan_input -m comment --comment "!fw3: Custom lan input rule chain" -j input_lan_rule
[0:0] -A zone_lan_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[0:0] -A zone_lan_input -m comment --comment "!fw3" -j zone_lan_src_ACCEPT
[0:0] -A zone_lan_output -m comment --comment "!fw3: Custom lan output rule chain" -j output_lan_rule
[0:0] -A zone_lan_output -m comment --comment "!fw3" -j zone_lan_dest_ACCEPT
[0:0] -A zone_lan_src_ACCEPT -i br-lan -m conntrack --ctstate NEW,UNTRACKED -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_wan_dest_ACCEPT -o br-wan -m conntrack --ctstate INVALID -m comment --comment "!fw3: Prevent NAT leakage" -j DROP
[1341:92069] -A zone_wan_dest_ACCEPT -o br-wan -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_wan_dest_REJECT -o br-wan -m comment --comment "!fw3" -j reject
[0:0] -A zone_wan_forward -m comment --comment "!fw3: Custom wan forwarding rule chain" -j forwarding_wan_rule
[0:0] -A zone_wan_forward -p esp -m comment --comment "!fw3: Allow-IPSec-ESP" -j zone_lan_dest_ACCEPT
[0:0] -A zone_wan_forward -p udp -m udp --dport 500 -m comment --comment "!fw3: Allow-ISAKMP" -j zone_lan_dest_ACCEPT
[0:0] -A zone_wan_forward -m comment --comment "!fw3: Zone wan to VPN_zone forwarding policy" -j zone_VPN_zone_dest_ACCEPT
[0:0] -A zone_wan_forward -m comment --comment "!fw3: Zone wan to VLAN_zona forwarding policy" -j zone_VLAN_zona_dest_ACCEPT
[0:0] -A zone_wan_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[0:0] -A zone_wan_forward -m comment --comment "!fw3" -j zone_wan_dest_REJECT
[176:14110] -A zone_wan_input -m comment --comment "!fw3: Custom wan input rule chain" -j input_wan_rule
[4:1272] -A zone_wan_input -p udp -m udp --dport 68 -m comment --comment "!fw3: Allow-DHCP-Renew" -j ACCEPT
[0:0] -A zone_wan_input -p icmp -m icmp --icmp-type 8 -m comment --comment "!fw3: Allow-Ping" -j ACCEPT
[0:0] -A zone_wan_input -p igmp -m comment --comment "!fw3: Allow-IGMP" -j ACCEPT
[0:0] -A zone_wan_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[172:12838] -A zone_wan_input -m comment --comment "!fw3" -j zone_wan_src_ACCEPT
[378:26517] -A zone_wan_output -m comment --comment "!fw3: Custom wan output rule chain" -j output_wan_rule
[378:26517] -A zone_wan_output -m comment --comment "!fw3" -j zone_wan_dest_ACCEPT
[172:12838] -A zone_wan_src_ACCEPT -i br-wan -m conntrack --ctstate NEW,UNTRACKED -m comment --comment "!fw3" -j ACCEPT
COMMIT
Ivan