I just had some time and fired up a Vm with the latest OpenWrt snapshot to help and do some debugging.
First of all I’m a pretty noob when I comes to nftables…
Got the same error messages as the others. Like @dave14305 explained there is an issue because it wants to create a table inside of a table, but I think you don’t have to create an extra table “dscptag”. Just create a chain dscptag in the table fw4.
For testing purposes I removed:
table inet dscptag {
…. and the error disappeared
But I got a lot of other errors (even more afterwards):
[details="Summary"]
This text will be hidden
[/details]
root@OpenWrt:~# service firewall restart
In file included from /dev/stdin:20:2-33:
/etc/nftables.d/dscptagNEW.nft:23:12-16: Error: syntax error, unexpected string
ip proto udp udp sport $udpbulkport ip dscp set cs1
^^^^^
In file included from /dev/stdin:20:2-33:
/etc/nftables.d/dscptagNEW.nft:26:12-16: Error: syntax error, unexpected string
ip proto udp udp dport $udpbulkport ip dscp set cs1
^^^^^
In file included from /dev/stdin:20:2-33:
/etc/nftables.d/dscptagNEW.nft:29:12-16: Error: syntax error, unexpected string
ip proto tcp tcp sport $tcpbulkport ip dscp set cs1
^^^^^
In file included from /dev/stdin:20:2-33:
/etc/nftables.d/dscptagNEW.nft:31:12-16: Error: syntax error, unexpected string
ip proto tcp tcp dport $tcpbulkport ip dscp set cs1
^^^^^
In file included from /dev/stdin:20:2-33:
/etc/nftables.d/dscptagNEW.nft:35:12-16: Error: syntax error, unexpected string
ip proto tcp tcp flags & ack meta length < 100 add @vfast4ack {ip daddr . ip saddr . tcp dport . tcp sport limit rate over 30000/second} random mod 1000 > 5 drop
^^^^^
In file included from /dev/stdin:20:2-33:
/etc/nftables.d/dscptagNEW.nft:36:12-16: Error: syntax error, unexpected string
ip proto tcp tcp flags & ack meta length < 100 add @fast4ack {ip daddr . ip saddr . tcp dport . tcp sport limit rate over 3000/second} random mod 1000 > 50 drop
^^^^^
In file included from /dev/stdin:20:2-33:
/etc/nftables.d/dscptagNEW.nft:37:12-16: Error: syntax error, unexpected string
ip proto tcp tcp flags & ack meta length < 100 add @med4ack {ip daddr . ip saddr . tcp dport . tcp sport limit rate over 300/second} random mod 1000 > 500 drop
^^^^^
In file included from /dev/stdin:20:2-33:
/etc/nftables.d/dscptagNEW.nft:38:12-16: Error: syntax error, unexpected string
ip proto tcp tcp flags & ack meta length < 100 add @slow4ack {ip daddr . ip saddr . tcp dport . tcp sport limit rate over 300/second} random mod 1000 > 500 drop
^^^^^
In file included from /dev/stdin:20:2-33:
/etc/nftables.d/dscptagNEW.nft:41:12-16: Error: syntax error, unexpected string
ip proto udp udp dport $vidconfports ip dscp set cs4
^^^^^
In file included from /dev/stdin:20:2-33:
/etc/nftables.d/dscptagNEW.nft:44:12-16: Error: syntax error, unexpected string
ip proto udp udp daddr $realtime4 ip dscp set cs5
Here are some findings:
I think “proto” has to be “protocol”
“udp udp daddr” has to be “udp ip daddr”
For Port ranges you have to use “-”
….
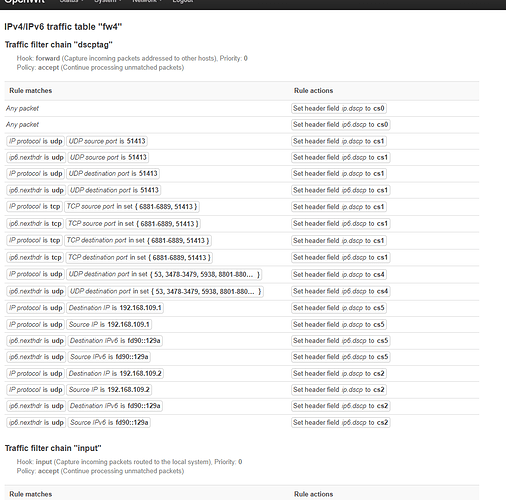
Here is a minimalistic script with no error you can compare with yours:
define udpbulkport = {51413}
define tcpbulkport = {51413,6881-6889}
define vidconfports = {10000,3478-3479,8801-8802,19302-19309,5938,53}
define realtime4 = {192.168.109.1} # example, just add all your game console here
define realtime6 = {fd90::129a} ## example only replace with game console
define lowpriolan4 = {192.168.109.2} # example, add your low priority lan machines here
define lowpriolan6 = {fd90::129a} ## example, add your low priority lan ipv6 PUBLIC addr here
define ackrate = 300
define downrate = 15000 # kbits/sec ... CHANGE ME
define uprate = 15000 # kbits/sec ... CHANGE ME
chain dscptag {
type filter hook forward priority 0; policy accept;
# wash all the DSCP to begin with ... you can comment this out
ip dscp set cs0
ip6 dscp set cs0
ip protocol udp udp sport $udpbulkport ip dscp set cs1
ip6 nexthdr udp udp sport $udpbulkport ip6 dscp set cs1
ip protocol udp udp dport $udpbulkport ip dscp set cs1
ip6 nexthdr udp udp dport $udpbulkport ip6 dscp set cs1
ip protocol tcp tcp sport $tcpbulkport ip dscp set cs1
ip6 nexthdr tcp tcp sport $tcpbulkport ip6 dscp set cs1
ip protocol tcp tcp dport $tcpbulkport ip dscp set cs1
ip6 nexthdr tcp tcp dport $tcpbulkport ip6 dscp set cs1
## ack limit rate to about 150 pps by decimating the quantity of pure acks being sent
#ip protocol tcp tcp flags & ack meta length < 100 add @vfast4ack {ip daddr . ip saddr . tcp dport . tcp sport limit rate over 30000/second} random mod 1000 > 5 drop
#ip protocol tcp tcp flags & ack meta length < 100 add @fast4ack {ip daddr . ip saddr . tcp dport . tcp sport limit rate over 3000/second} random mod 1000 > 50 drop
#ip protocol tcp tcp flags & ack meta length < 100 add @med4ack {ip daddr . ip saddr . tcp dport . tcp sport limit rate over 300/second} random mod 1000 > 500 drop
#ip protocol tcp tcp flags & ack meta length < 100 add @slow4ack {ip daddr . ip saddr . tcp dport . tcp sport limit rate over 300/second} random mod 1000 > 500 drop
## for almost everyone we won't send more than 150 acks/second
ip protocol udp udp dport $vidconfports ip dscp set cs4
ip6 nexthdr udp udp dport $vidconfports ip6 dscp set cs4
ip protocol udp ip daddr $realtime4 ip dscp set cs5
ip protocol udp ip saddr $realtime4 ip dscp set cs5
ip6 nexthdr udp ip6 daddr $realtime6 ip6 dscp set cs5
ip6 nexthdr udp ip6 saddr $realtime6 ip6 dscp set cs5
ip protocol udp ip daddr $lowpriolan4 ip dscp set cs2
ip protocol udp ip saddr $lowpriolan4 ip dscp set cs2
ip6 nexthdr udp ip6 daddr $lowpriolan6 ip6 dscp set cs2
ip6 nexthdr udp ip6 saddr $lowpriolan6 ip6 dscp set cs2
#downgrade udp going faster than 450 pps, probably not realtime traffic
#ip protocol udp ip dscp > cs2 add @udp_meter4 {ip saddr . ip daddr . udp sport . udp dport limit rate over 450/second} counter ip dscp set cs2
#ip6 nexthdr udp ip6 dscp > cs2 add @udp_meter6 {ip6 saddr . ip6 daddr . udp sport . udp dport limit rate over 450/second} counter ip dscp set cs2
# down prioritize the first 500ms of tcp packets
#ip protocol tcp ct bytes > $downrate * 500/8 ip dscp < cs4 ip dscp set cs2
# downgrade tcp that has transferred more than 10 seconds worth of packets
#ip protocol tcp ct bytes >
[details="Summary"]
This text will be hidden
[/details]
$downrate * 10000/8 ip dscp < cs4 ip dscp set cs1
## tcp with less than 150 pps gets upgraded to cs4
#ip protocol tcp add @slowtcp4 {ip saddr . ip daddr . udp sport . udp dport limit 150/second burst 150} ip dscp set cs4
#ip6 nexthdr tcp add @slowtcp6 {ip6 saddr . ip6 daddr . udp sport . udp dport limit 150/second burst 150} ip dscp set cs4
}
I commented out all lines where I got and error and did not find a fast answer!!
Looks good: