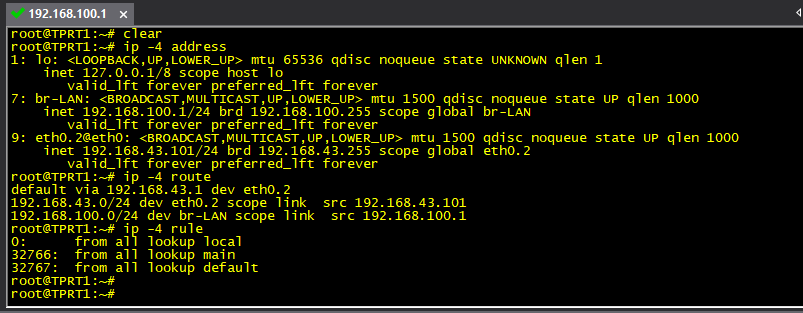
ip -4 addr; ip -4 ro ; ip -4 ru
?
Changed WC lan subnet to 192.168.100.x. Same result as earlier at the hotspot router. Router ignores the static route if 4g network is active!!
Remove these two lines under LAN
config interface 'LAN'
option gateway '10.0.0.1'
option dns '10.0.0.1'
That's valid when the WC lan subnet was 10.0.0.x subnet. Now the WC lan subnet is changed to 192.168.100.x subnet as per @mbo2o suggestion.
Then post again the whole network/wireless/firewall configs as well as ip -4 addr; ip -4 ro ; ip -4 ru
UPDATE:
/etc/config/network
config interface 'LAN'
option proto 'static'
option netmask '255.255.255.0'
option type 'bridge'
option ifname 'eth0.1'
option ipaddr '192.168.100.1'
option gateway '192.168.100.1'
option dns '192.168.100.1'
config interface 'WAN'
option ifname 'eth0.2'
option proto 'static'
option ipaddr '192.168.43.101'
option netmask '255.255.255.0'
option gateway '192.168.43.1'
/etc/config/firewall
config defaults
option syn_flood '1'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
config zone
option name 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
option network 'LAN'
config zone
option name 'wan'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option network 'WAN'
option input 'REJECT'
On WC router:
First remove those two.
config interface 'LAN'
option gateway '192.168.100.1'
option dns '192.168.100.1'
You'd also need a lan2wan and wan2lan rule in firewall.
Other than that everything is correct.
Ok. I did that. What next?
/etc/config/network
config interface 'LAN'
option proto 'static'
option netmask '255.255.255.0'
option type 'bridge'
option ifname 'eth0.1'
option ipaddr '192.168.100.1'
config interface 'WAN'
option ifname 'eth0.2'
option proto 'static'
option ipaddr '192.168.43.101'
option netmask '255.255.255.0'
option gateway '192.168.43.1'
https://oldwiki.archive.openwrt.org/doc/recipes/routedclient#using_routing
/etc/config/network
config defaults
option syn_flood '1'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
config zone
option name 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
option network 'LAN'
config zone
option name 'wan'
option network 'WAN'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option masq_dest '!192.168.43.1/24'
option mtu_fix 1
config forwarding
option src 'lan'
option dest 'wan'
config rule 'forward_from_WP'
option src wan
option dest lan
option src_ip '192.168.43.0/24'
option proto all
option target ACCEPT
After changing firewall config to this, the client side hosts cannot reach 192.168.43.x network. Otherthings remain as same as before.
I was a bit confused regarding which device you show is which.
Back to the config:
In Openwrt you don't need this:
config rule 'forward_from_WP'
option src wan
option dest lan
option src_ip '192.168.43.0/24'
option proto all
option target ACCEPT
Instead add the wan2lan forwarding, like you did with lan2wan.
Also remove the nat and mtu from the wan zone:
config zone
...
option masq '1'
option masq_dest '!192.168.43.1/24'
option mtu_fix 1
You will also need to add a nameserver in WAN interface (the Android or some google dns)
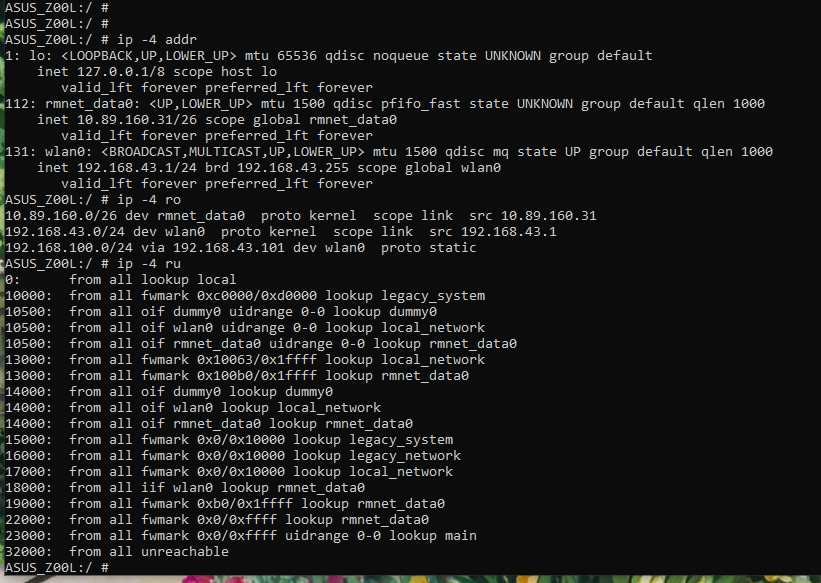
On Android run the following:
ip -4 addr; ip -4 ro ; ip -4 ru
/etc/config/firewall
config defaults
option syn_flood '1'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
config zone
option name 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
option network 'LAN'
config zone
option name 'wan'
option network 'WAN'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
config forwarding
option src 'lan'
option dest 'wan'
config forwarding
option src 'wan'
option dest 'lan'
The public nameservers are in /etc/config/dhcp under dnsmasq. That's ok.
Here's the screenshot from Android hotspot:
ip -4 addr; ip -4 ro ; ip -4 ru
It looks like your android is doing some policy routing.
Hence the different routes that are inconsistent with the static routes.
You can examine them by ip -4 ro list table table_name
ASUS_Z00L:/ # route
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
10.89.160.0 * 255.255.255.192 U 0 0 0 rmnet_data0
192.168.43.0 * 255.255.255.0 U 0 0 0 wlan0
192.168.100.0 192.168.43.101 255.255.255.0 UG 0 0 0 wlan0
That's the routing table in the android hotspot router. I noticed something strange regarding the packet forwarding.
When 4g network is on:
packets destined towards 192.168.100.0 always move to 10.89.160.0
When 4g network is off:
10.89.160.0 route is removed and packets destined towards 192.168.100.0 are forwared to 192.168.43.101 as per the route table.
Ok...
How can I solve this? :
The easy solution is to enable again NAT/MTU in firewall zone WAN. Exclude NAT for addresses
192.168.43.0/24. For each PC in 192.168.43.X add a static route for 192.168.100.0/24 via 192.168.43.101.
The hard way would be to search what Android is doing and adds these rules.
Actually I want to setup the things the right way 
My phone will be core upstream router/hotspot which serves internet to all the client devices on a different subnet and at the same time I would like to use the client side resources like ftp server, windows shares on laptops, play content on dlna tv... Usually these things work fine, when they all are on a same subnet. In my case, my phone and client side hosts are on different subnets. I want to make all these devices communicate with each other with the help of routers. I'm also eager to setup things that way 
Then you should use a proper router instead of an Android phone
Use the 192.168.43.1 AP as your main router and keep the hotspot as your internet connection via Wan