I have no clue, it seems like the nameserver lookup to dns.google works normally with or without the firewall port 443 traffic reject rule, but I think that's just normal behaviour, the corresponding IP's to dns.google should be found normally through my normal DNS provider (I'm using AdGuard's DNS, 176.103.130.130 and 176.103.130.131). So the nameserver lookups are probably done through these IP's.
I also set up the DNS interception, but koffiezetapparaat.lan stays unpingable (except for when I explicitly set 192.168.1.1 as DNS in in the query settings).
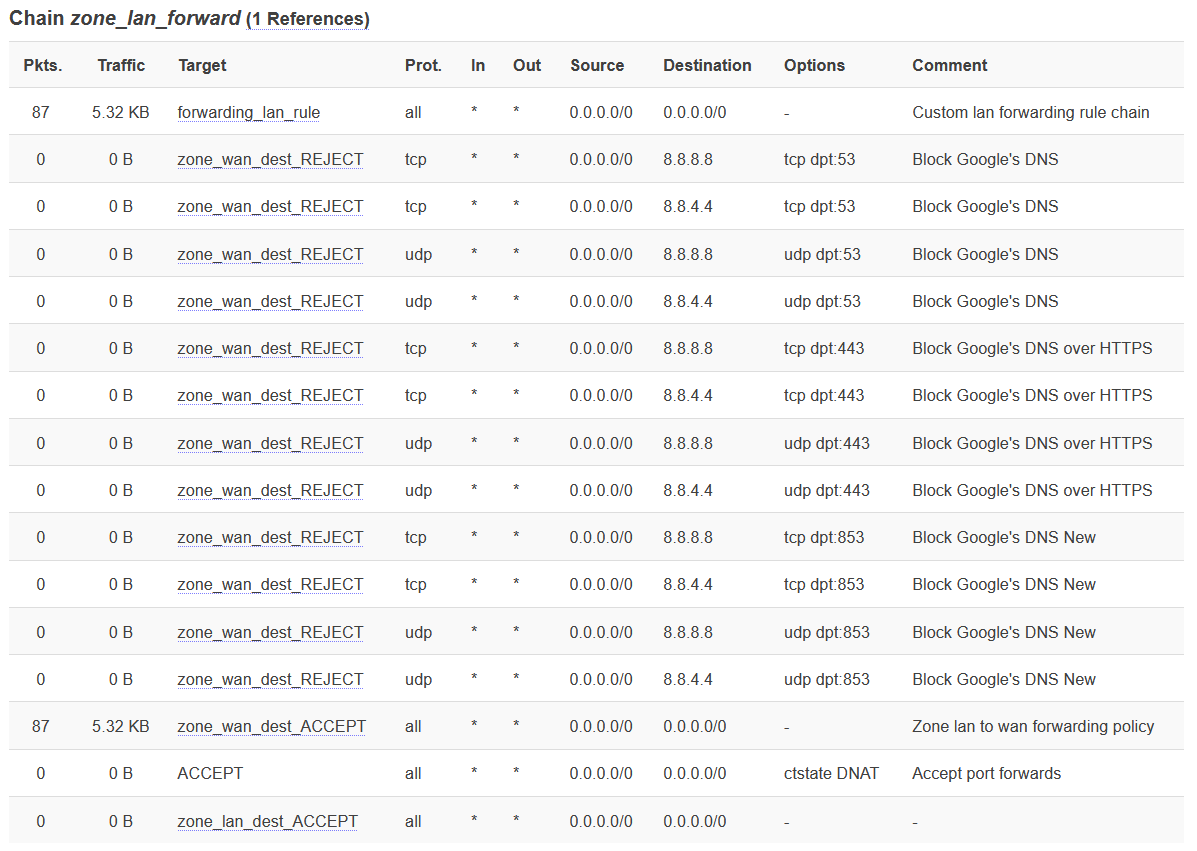
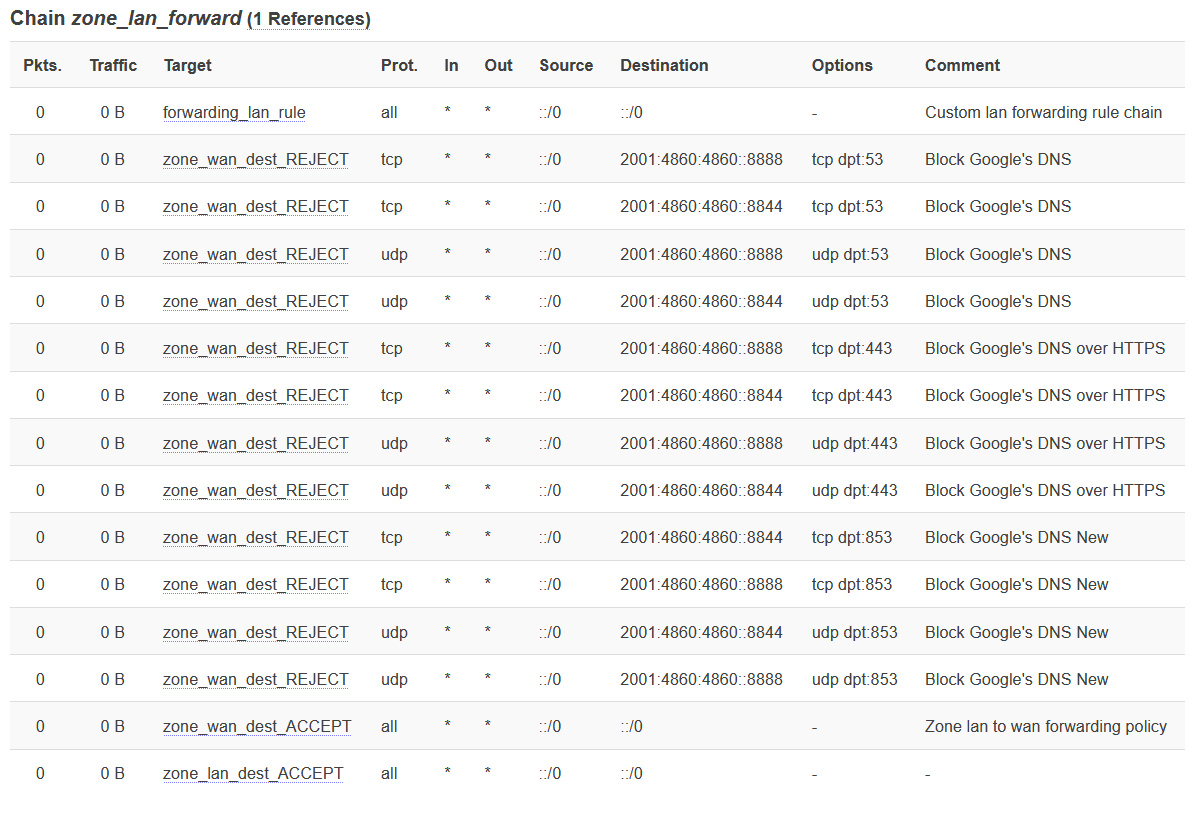
I also set up the firewall settings to block all traffic to Google's IPv4 and IPv6 servers over ports 53 an 443 without result:
You also need to block UDP/53
Better post the configuration than screenshots.
uci export firewall
root@openwrt:~# uci export firewall
package firewall
config defaults
option syn_flood '1'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
config zone
option name 'lan'
list network 'lan'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'ACCEPT'
config zone
option name 'wan'
list network 'wan'
list network 'wan6'
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
config forwarding
option src 'lan'
option dest 'wan'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option src_ip 'fc00::/6'
option dest_ip 'fc00::/6'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option dest 'lan'
option proto 'esp'
option target 'ACCEPT'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest 'lan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
config include
option path '/etc/firewall.user'
config include 'nat6'
option path '/etc/firewall.nat6'
option reload '1'
config rule
option dest 'wan'
option src 'lan'
option name 'Block Google'\''s DNS'
option dest_port '53'
option target 'REJECT'
list dest_ip '8.8.8.8'
list dest_ip '8.8.4.4'
list dest_ip '2001:4860:4860::8888'
list dest_ip '2001:4860:4860::8844'
list proto 'tcp'
list proto 'udp'
config redirect 'dns_int'
option name 'Intercept-DNS'
option src 'lan'
option src_dport '53'
option proto 'tcp udp'
option target 'DNAT'
config rule
option dest_port '443'
option src 'lan'
option name 'Block Google'\''s DNS over HTTPS'
option dest 'wan'
list dest_ip '8.8.8.8'
list dest_ip '8.8.4.4'
list dest_ip '2001:4860:4860::8888'
list dest_ip '2001:4860:4860::8844'
option target 'REJECT'
list proto 'tcp'
list proto 'udp'
root@openwrt:~# cat /etc/firewall.nat6
iptables-save -t nat \
| sed -e "/\s[DS]NAT\s/d;/\sMASQUERADE$/d;/\s--match-set\s\S*/s//\06/" \
| ip6tables-restore -T nat
You need to intercept plain DNS aka 53/udp and 53/tcp, so don't block it.
The DNAT is taking place earlier in prerouting chain of nat table, so it should not be affected by a blocking rule in forward chain of filter table.
trendy, vgaetera:
OK, so AFAIK, my rules are set up correctly now, yet, my Android phone can't resolve koffiezetapparaat.lan. Any idea on what might be going on?
Check from the LAN client:
nslookup koffiezetapparaat.lan 8.8.8.8
This should be intercepted and resolved correctly.
This is so strange, it seems to work correctly from e.g. my laptop:
$ nslookup koffiezetapparaat.lan 8.8.8.8
Server: 8.8.8.8
Address: 8.8.8.8#53
Name: koffiezetapparaat.lan
Address: 192.168.1.190
and even with different DNS servers:
$ nslookup koffiezetapparaat.lan 1.1.1.1
Server: 1.1.1.1
Address: 1.1.1.1#53
Name: koffiezetapparaat.lan
Address: 192.168.1.190
but still not on my Android phone.
I looked it a bit up and it seems that there are other people with (kind of) the same problem. For instance, this topic on Android stack exchange: https://android.stackexchange.com/questions/49188/how-to-get-mdns-working-for-chrome-on-android
Manually setting the primary (and secondary) DNS server to 192.168.1.1 didn't change anything either. I have no clue on how to go from here, really.
It seems the only way out is to buy a public domain. 
guys? has anyone tried my suggestion yet? Force Android phone to use local DNS for local domain name resolving
For me Network Analyzer can resolve and ping a host in the lan, but maybe it has to do with the Android version. I have just a hijack rule to send all queries to my Piholes.
Newer Androids using port 853 by default for name resolution on IPv6. If IPv6 service is not available the fallback is hardcoded for 8.8.8.8/4.4 port 53 in any case. A public resolver will never resolve a local domain.
For me it sounds you have missconfigured dnsmasq/firewall. Like dnsmasq is bypassed. oO
What happen if you edit /etc/hosts and enter a new line with "192.168.1.190 koffiezetapparaat koffiezetapparaat.lan"? Is it getting resolved now?
What is the output of: "uci show dhcp"?
That's pretty cool, this actually works:
I still hope to find a solution which is less of a workaround, but if I don't find it, I will use this app!
Try to block both DoH and DoT ports for Google DNS:
What happen (...) resolved now?
# cat /etc/hosts
127.0.0.1 localhost
::1 localhost ip6-localhost ip6-loopback
ff02::1 ip6-allnodes
ff02::2 ip6-allrouters
192.168.1.190 koffiezetapparaat koffiezetapparaat.lan
Then I issued /etc/init.d/dnsmasq restart but still ended up with 'Failed to resolve IP address'.
What is the output of: "uci show dhcp"?
root@openwrt:~# uci show dhcp
dhcp.@dnsmasq[0]=dnsmasq
dhcp.@dnsmasq[0].domainneeded='1'
dhcp.@dnsmasq[0].localise_queries='1'
dhcp.@dnsmasq[0].rebind_protection='1'
dhcp.@dnsmasq[0].rebind_localhost='1'
dhcp.@dnsmasq[0].local='/lan/'
dhcp.@dnsmasq[0].domain='lan'
dhcp.@dnsmasq[0].expandhosts='1'
dhcp.@dnsmasq[0].authoritative='1'
dhcp.@dnsmasq[0].readethers='1'
dhcp.@dnsmasq[0].leasefile='/tmp/dhcp.leases'
dhcp.@dnsmasq[0].resolvfile='/tmp/resolv.conf.auto'
dhcp.@dnsmasq[0].localservice='1'
dhcp.lan=dhcp
dhcp.lan.interface='lan'
dhcp.lan.start='100'
dhcp.lan.limit='150'
dhcp.lan.dhcpv6='server'
dhcp.lan.ra='server'
dhcp.lan.ra_management='1'
dhcp.lan.leasetime='2h'
dhcp.lan.force='1'
dhcp.wan=dhcp
dhcp.wan.interface='wan'
dhcp.wan.ignore='1'
dhcp.odhcpd=odhcpd
dhcp.odhcpd.maindhcp='0'
dhcp.odhcpd.leasefile='/tmp/hosts/odhcpd'
dhcp.odhcpd.leasetrigger='/usr/sbin/odhcpd-update'
dhcp.odhcpd.loglevel='4'
dhcp.@host[0]=host
dhcp.@host[0].mac='[mqtt-mac]'
dhcp.@host[0].dns='1'
dhcp.@host[0].ip='192.168.1.4'
dhcp.@host[0].name='mqtt'
dhcp.@host[1]=host
dhcp.@host[1].mac='[openwrt-mac]'
dhcp.@host[1].name='openwrt'
dhcp.@host[1].dns='1'
dhcp.@host[1].ip='192.168.1.1'
dhcp.@host[2]=host
dhcp.@host[2].mac='[second openwrt-mac]'
dhcp.@host[2].name='openwrt-boven'
dhcp.@host[2].dns='1'
dhcp.@host[2].ip='192.168.1.2'
dhcp.@host[3]=host
dhcp.@host[3].mac='[third openwrt-mac]'
dhcp.@host[3].name='openwrt-kelder'
dhcp.@host[3].dns='1'
dhcp.@host[3].ip='192.168.1.3'
dhcp.@host[4]=host
dhcp.@host[4].name='openhab'
dhcp.@host[4].dns='1'
dhcp.@host[4].ip='192.168.1.5'
dhcp.@host[4].mac='[openhab-mac]'
I have added this part to the firewall:
firewall.@rule[11]=rule
firewall.@rule[11].dest_port='853'
firewall.@rule[11].src='lan'
firewall.@rule[11].name='Block Google'\''s DNS New'
firewall.@rule[11].dest='wan'
firewall.@rule[11].target='REJECT'
firewall.@rule[11].dest_ip='8.8.8.8' '8.8.4.4' '2001:4860:4860::8844' '2001:4860:4860::8888'
firewall.@rule[11].proto='tcp' 'udp'
However, koffiezetapparaat doesn't get resolved with this new rule.
What might be interesting: I took a look at /cgi-bin/luci/admin/status/iptables and saw that there hasn't been any traffic on those rules until now:
Perhaps I should set something up in OpenWrt to see what addresses (and ports) my Android device tries to communicate with?
Make sure to reconnect your phone to apply changes.
Reloading OpenWrt firewall most likely doesn't break established connections.
Hmm... If hosts file does not bite then I would assume that your phone is not asking DNSmasq for DNS. On my phone I can set WLAN settings manually. If I do so it is pre-filled with 8.8.8.8 and 8.8.4.4 (Android 9) for DNS resolution. If I replace it with a dummy dns (does not resolve anything) I can see that the device itself is still using an huawei dns resolver to get in touch with his own services (dns.hi-cloud.cn; cannot remember the exact name anymore; tcpdump showed me the traffic).
So I decided for myself to intercept any 53,853,5353 traffic redirecting to LAN IP respectivly I've blocked 853 and 5353 completely. In addition I've blocked the main DoH IPs/Servers including Huawei DNS. I cannot be sure if I got all because there is a lot 443 traffic to other Huawei domains also.
If you setup all correctly (esp. your firewall rules) then Android is using your DNS resolver for sure. It is remarking this if you connect your phone to a WLAN with this hard redirects with an "!" beside of the Wifi picture in headline at the beginning of the connection was initiated (like no connection available).
But beside all that it (in my experience) it is more likely that the program which you are using to access your LAN location is not using the defaults from Android and is using its own DNS resolution method. I can see this on my device also. Some Apps are able to use local names others are not. Which means that I have to use plain IP instead.
And Android 9+ has an option to explicit set an DNS (called "Private DNS"). You could try to set DNS here globally (at least for Android)
.
So the best bet is to analyse with tcpdump first to see what is going on and/or to try another program to see if things are changing. If I look at your LSC Smart .... App I would say that it is more an App issue.
My 2 cents, have you double checked the DHCP server properties (you may force the DNS in DHCP options, and add a custom local domain)...
Do you also use a local suffix domain ?
Lan / Local / other...
Sometimes, short (local or lan) resolutions do not work correctly, but a full local domain may fix this behavior...