Continuing on this train of thought, I think we can do even simpler. ![]()
![]()
![]()
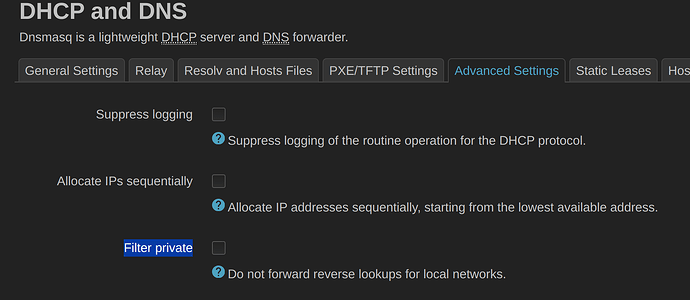
Step 1: Fix in-addr.arpa look-ups
Turns out the reverse DNS queries are just blocked by the "Filter Private" option under DNS settings. If you just uncheck this everything works AFAICT and your upstream private DNS server will respond. Can also delete the /in-addr.arpa/1.2.3.4 forwarder entry since it'll naturally do this unless you need to forward to a different DNS server.
In this case my upstream DNS server is private anyways and this isn't an Internet facing OpenWRT installation as the default is intended for:
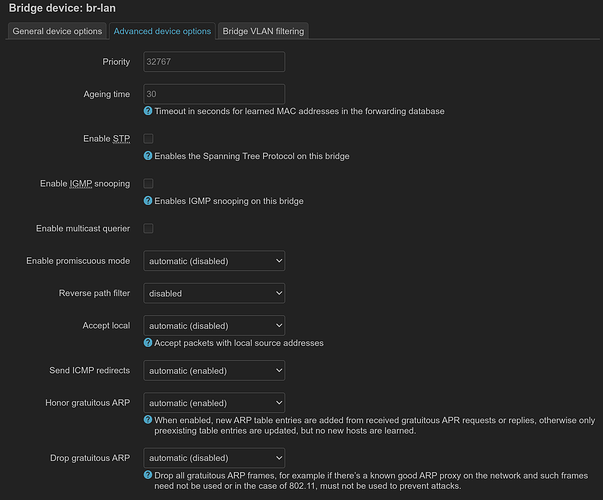
Step 2: Fill in the ARP table
Basically two options:
- Use gratuitous ARPs that happen automatically on the network by configuring it on the bridge which seems to be the default (maybe my v23.05-rc3 upgrade had bad state and I had to reset?), see here:
Less preferred, you can addnet.ipv4.conf.br-lan.arp_accept=1to/etc/sysctl.conf(test withsysctl -w net.ipv4.conf.br-lan.arp_accept=1) and just tell the kernel to accept them. This has a minor security implication, but unsolicited ARPs are probably pretty easy to overcome if someone is actually attacking your internal network with ARP spoofing. - Generate traffic periodically using
arp-scanandfping. You'll need to use both becausearp-scanwill find the devices, but since it usesRAWsockets and promiscuous mode, which means it'll by pass the kernel's networking stack and create entries in the ARP table (view withip neigh). This is why people then usefpingto then ping the same device again using the networking stack which generates the ARP entry. This is also why people witharp_accept=1can skip thefpingstep because they are already accepting gratuitous ARPs (see above).
For me personally, I'd rather not wake my sleeping battery powered IoT WiFi devices every few minutes to update a table, so I choose option (1) and don't generate any new traffic and to save battery life and save some RF air time. For security, I assume local network is inherently susceptible to someone doing bad things and depend more on higher level security (TLS) in the event someone ARP spoofs my home network.
Testing
Clear the ARP table which will cause all the host name and IP values to change to ? on reload under Associated Stations:
ip neigh flush all
The entries will then get re-populated via arp_accept, fping, or any standard traffic between the router and station.
May also need to restart dnsmasq if has cached reverse DNS lookups.