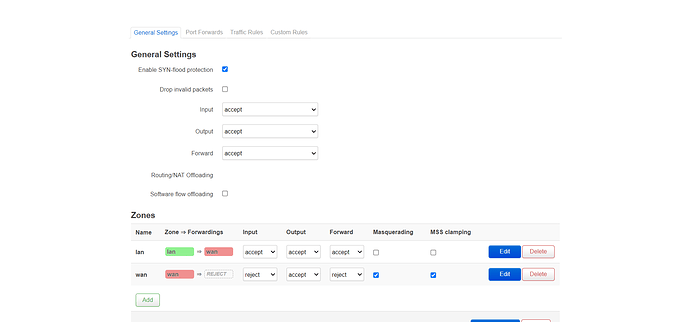
Allow forwarding from WAN to LAN and disabling Masquerading would be my guess.
Though the wan looks configured right as it is.(except the Masquerading)
Also I'm not familiar with MSS clamping, but I've heard that it can bring some problems with it.
I tried all these things but got no answer
Did you try to ping an address or how did you test?
Yes, I tested and checked with tcpdump
But I do not understand where the problem comes from and in which part there is a problem
Basically I have to send my requests to the isp network with ip 94.x.x.x without nat
When nat is disabled I manually create the root bye
How do I route Lan to wan ?
Can you do a traceroute and post the result?
C:\Users\x>tracert 8.8.8.8
Tracing route to 8.8.8.8 over a maximum of 30 hops
1 <1 ms <1 ms <1 ms openwrt.lan [94.x.x.153]
2 29 ms 200 ms * 172.20.40.184
3 29 ms 33 ms 25 ms 172.20.40.181
4 51 ms 53 ms 57 ms 172.20.40.74
5 * * * Request timed out.
6 * ^C
Is this with Masquerading enabled?
Yes exactly
If disable not respond after lan ip
And do you reach 8.8.8.8 in the end, with masquerading enabled?
No timeout until the end
In both cases
If masq is active when I sent the trace, if it is not, it will be out after lan timeout
I can think of the following problems.
- When you deactivate Masquerading you have to allow forwarding from WAN to LAN which might be an issue
- Your ISP has a firewall at hop 6 which is blocking stuff
- The route to your public subnet is unknown
Can you make a traceroute with the forwarding from wan to lan and masquerading disabled?
Also I can test if I can reach your router (subnet), if you are comfortable with sharing your public IP with me (via Private Message).
I'm wondering about:
- reverse path filtering
- DHCP proxy-ing
- ARP proxy and nd proxy
- Masquerade vs SNAT
- /32 interface assignments.
The described intended setup is very similar to what folks do with odhcpd and IPv6; when their ISP gives them as many /64 as they have hosts requesting those IPs, but people want all their traffic to go through a router. ISP sees all the IPs as being on the router, router knows where they actually are. Then you complicate it further with dynamically allocated IPs, and firewalls and the fact you're using ipv4 that supports a limited number of IPs.
I did not get you
Do you know where the problem comes from and what exactly should I do?
I agree with @ASFP . next step should definitely be to check if ISP is forwarding packets to you correctly.
run $ tcpdump -ni eth0.2 icmp or arp on the router (after installing tcpdump if you haven't already) and wait for it to show you ping packets coming in. While waiting ping one or several of your public IPs e.g. from your phone over LTE to see if they're coming in.
If your ISP is giving you a /32 via dhcp - this is a scheme to save IPV4 addresses.
The IP given to you will be the IP you're meant to configure on your end, the broadcast address should be your own ip, the netmask will be 255.255.255.255 (/32 basically) and the gateway will be the address of the other endpoint.
Additionally you'll need to have a route to the gateway upstream of your router ... because of the /32 - it's not on the same subnet, .. you'd do this by doing ip route add 172.20.40.74 dev eth0.2 ... I think this may be done ok for you. .. because of that traceroute.
check tcpdump and check ping, if that works you can also check tcpdump on eth0.1 to see if your router is sending ping requests out on the lan interface ... and then whether the host on the lan interface is replying. (my point is there's 4 packets you should be able to capture going in/out/in/out of your router for a single ping request). .. check it, see where things are getting lost.
@komeilkma This is probably the problem. I tested it with a /24 network so i had a gateway in the same subnet. Beside my assumption with the routing error.
Thank you very much, I will test now
This is absolutely a misunderstanding. NAT is NOT a firewall, and the firewall still operates whether you use NAT or not. For example IPv6 gives you public IPs on LAN and still has a firewall.
This turns off your firewall and should not be done.
So what should be done to solve this problem?