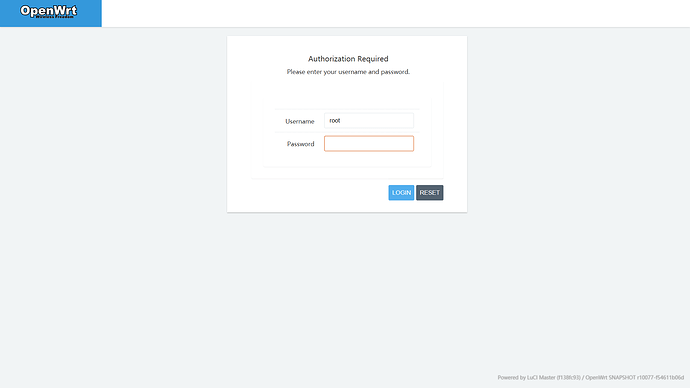
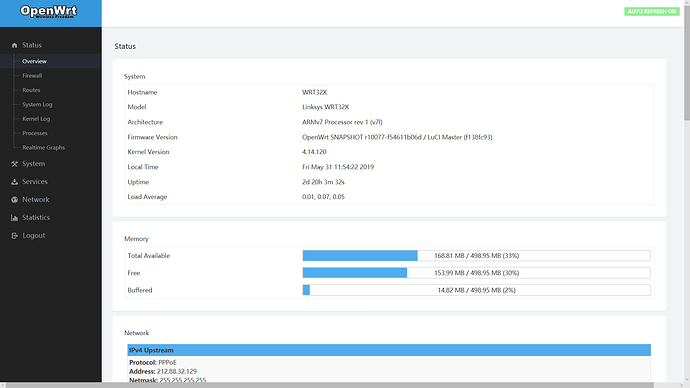
Was changed to luci-theme-atmaterial in this latest build. Rosy is still available if you want to use it.
I have this kind of issue even on low channels if use non-US zone in config.
I have an issue getting Wireguard to work. The connection between the two routers works, but after 10 seconds of the init, all traffic gets blocked between the two lans. Does Openwrt execute something after wg0 goes up which could cause this? I tried everything so far but nothing works. I can ping the br-lan devices from each lan fine, but any ping/traffic between the two lans behind the router wont work. Though they do work in the first 10 seconds after the wg handshake.
I just downloaded the latest build. What a nice theme that is 
Dear David
Hi Here updated with the last relase for a WRT3200
wifi 5ghz and 2.4Ghz all fine
all services up and running since 50hours w/o any issues or disconnection
logs looks clean
goood work thanks a lot
pascal
Dear mfka8,
Hello - I do not know that this will help you or not - but try checking out this - Solved: nordvpn OpenWrt wireguard client Hope it helps - if you give a few more details - are you using VPN provider - or rolled your own - and so on that would help others - assist you.
Peace
@directnupe Like I said, the wireguard connection works fine. Internet routed over it works fine. The only thing not working is, reaching lan to lan. The weird thing is, I can reach lan to lan in the first 10 seconds after the wireguard connection, and then it stops working. I can ping the br-lan devices from each lan, but I cant ping any lan behind the two routers. https://www.reddit.com/r/WireGuard/comments/bu81vd/cant_reach_lans_behind_wireguard_serverclient/
As if in the first 10 seconds, something gets executed that will block lan to lan traffic.
I have edited the theme even more just got to replace Router Model in the Branding area to OpenWRT's svg file. I have compiled the theme on my github page. Just remember to clear browser cache after installing else it will still show the old settings.
Dear solidus1983,
Thanks a ton in advance for your outstanding work on this theme.I seem not to be the only person who is excited and very grateful that you took the time, effort and dedication to continue to work to towards making this a true customized build. You accepted comments from the peanut gallery; I for one appreciate that acceptance on your behalf. However, I seem to not be able to exactly pin down the github page your are referring to. The one with the last preview - says that it has not been updated in 8 days. Could you provide a direct link if it isn't too much to ask.
Thanks again - and Peace
I will be finishing it off soon just been busy, the devel version 0.0.1 is the one with the Linksys colouring. It will be updated to swap the branding section to OpenWRT SVG file soon ISH, currently having to look after my grandmother which is taking most of my time right now.
Dear mfka8,
Hello - and I am sorry that the advice I pointed out to you did not remedy your issue. Honestly, I just use a straightforward WireGuard Client setup. I am using TorGuard and NordVPN - so this is above my pay grade. However, I am sure that things will work out. Here is an idea for you. Try just adding your your WireGuard Network in the Wan FireWall Zone - DO NOT create a separate FireWall Zone for your WireGuard Network in the Firewall Configuration. Like So :
Open the file:
nano /etc/config/firewall
config zone
option name 'wan'
list network 'wan'
list network 'wan6'
list network 'wg0' ## This is the line you need to add - and you are done
option input 'REJECT'
option output 'ACCEPT'
option forward 'REJECT'
option masq '1'
option mtu_fix '1'
Trendy helped me with this. read his advice here : and I quote:
Personally I would assign the wg0 interface in the wan firewall zone. Simpler and achieves the desired result. His answer demonstrated : Sure, in wan zone edit the line
option network 'wan wan6'
and add wg0 interface. Try it - it works like a charm for me. On the reddit page ; the firewall rules are not correct - try this simple solution. Try it on both routers. Also DNS is important on the WireGuard Interface - I use stubby and getdns - so I use 127.0.0.1, 1.0.0.1, and 1.1.1.1 - the same DNS Servers I use on my Wan Interface.
No rush my Brother - God will Bless The Merciful - take care of what is truly important life first - always - as prioritizing is the key to almost everything.
thanks again - and I hope that your Grandmother is well. my Mom is 91 so I fully understand and I am sure that you are a Blessing to her. thanks for taking the time to reply.
Peace
@directnupe That doesnt make any sense. I dont want wg0 to be part of wan, that is total nonsense. It is not part of wan and shouldnt be, I dant want to have any masq rules on wg0 obviously too. That would totally not work and mess everything up. My setup isnt so simple, that this would work. I have an OpenVPN line too and I want the wireguard client lan to run over wireguard to the server and then out the OpenVPN line, I use mangle rules for it, and it works fine. I also have rules that no lan can go out of wan as a "killswitch" if OpenVPN is down (reject all lan to wan, so this would totall mess all up). The only thing NOT working is reaching lan ips behind the router and I have no idea why, it should work. And it also works for about 10 seconds after the FIRST handshake, then it stops for whatever reason. wg0 should be part of LAN not WAN, or have its own zone. And then just allow forwardning, but it doesnt work for whatever reason.
Dear mfka8,
Try contacting Trendy - the guy who helped me out with my setup. He is very experienced knowledgeable and helpful albeit a bit terse at times. Here is his profile on OpenWRT Forum : https://forum.openwrt.org/u/trendy Sorry I could not help you, but maybe he can and will. BTW, among his many other certifications - Trendy is a Network engineer.
Peace
I just disabled https and then I can't login, but I can ssh, what's going wrong?
It seems that the cookie has secure set, so it won't get sent without ssl
@davidc502 @directnupe and everyone else that is loving the theme. I have made some new edits and commited them to the devel git ready for merge to master git.
If everyone could comment on if this i would be grateful.
BTW the up&down arrows seem missing for me, for example in network/firewall/rules.
@Immueggpain Do you have a screenshot of this?
As looking on mine arrows are showing in Port Forwarding and Traffic Rules in the Network > Firewall area.
I like the looks from the screenshot. Have you got a compiled .ipk of these latest changes? I could not find it yet on your Github. I checked in the 'devel' branch as well. Thank you for your continued work with this, great stuff.