I'm sure there exist eaiser methods, I for one could just drop a pre made "network" file into /etc/config/network and restart. But it was a fun challenge and I learned something. When the other options pop up; I'll learn more! Enjoy your journey. @RuralRoots I have the suggestion saved to learn along with jq curl cat Thank you.
#!/bin/sh
echo "Running at $(date)"
uci reorder network.@[13]=12
uci commit network
/etc/init.d/network restart
logger -t yourIFname ":$(date) connection established"
## Undo examples:
## uci reorder network.@[13]=12
## uci reorder network.@[12]=13
## uci reorder network.@[13]=11
## uci reorder network.@[11]=13
## uci reorder network.@[13]=10
## uci reorder network.@[10]=13
## uci reorder network.@[13]=9
## uci reorder network.@[9]=13
####################################################################################
# MULTIPLE PEER(2) NETWORKS CAN BE ADDED TO LUCI AND SWAPPED BY .sh
# These networks are known by the notations below. Goal is to find peer(2).
# Plug in a number, or examine your "network" file ~ vi , nano, gui ~
# Count the unique "config" entries to find your first and last peer(2) entry
#
# (uci show network.@[]) #example will show first top entry /etc/config/network
# (uci show network.@[0]) #example will also show first top entry /etc/config/network
# (uci show network.@[1]) #example will show second entry /etc/config/network
# (uci show network.@[2]) #example will show third entry /etc/config/netork
# ....
# (uci show network.@[13] #example ~~ 13th entry /etc/config/network
# last peer=wg0 current tunnel us-nyc!
######################### Visual ##############################
#root@Dachshund:~# uci show network.@[]
#network.loopback=interface
#network.loopback.ifname='lo'
#network.loopback.proto='static'
#network.loopback.ipaddr='127.0.0.1'
#network.loopback.netmask='255.0.0.0'
#root@Dachshund:~# uci show network.@[0]
#network.loopback=interface
#network.loopback.ifname='lo'
#network.loopback.proto='static'
#network.loopback.ipaddr='127.0.0.1'
#network.loopback.netmask='255.0.0.0'
#root@Dachshund:~# uci show network.@[1]
#network.globals=globals
#network.globals.ula_prefix='0:0:0:0::/0'
#root@Dachshund:~# uci show network.@[13]
#network.cfg0e6912=wireguard_SSWG
#network.cfg0e6912.public_key='rhuoCmHdyYrh0zW3J0YXZK4aN3It7DD26TXlACuWnwU='
#network.cfg0e6912.peersistent_keepalive='25'
#network.cfg0e6912.endpoint_port='51820'
#network.cfg0e6912.allowed_ips='0.0.0.0/0' '::/0'
#network.cfg0e6912.route_allowed_ips='1'
#network.cfg0e6912.endpoint_host='us-nyc.prod.surfshark.com'
#network.cfg0e6912.description='nyc-prod'
#
# Per OpenWrt - CFGID's are assigned to WireGuard Peers in order a~z.
# Shown below as cfg0(a)6912, cfg0(b)6912, etcetera
# Static entries insofar as peers do not move in order, unless commanded to. This sh's goal.
# The command: (uci reorder network.'cfg0a6912'=) will move that peer <NOTE:AVOID>
# to the very top of your /etc/config/network file and the CFGID's will change!
# The command: (uci reorder network.@[9]=) will move that peer <NOTE:AVOID>
# to the very top of your /etc/config/network file and the CFGID's will change!
# These CFGID can be found by either using a web browser's inspect tool
# upon the peer in the setup section of the Peer Tab in Luci, or
# invoking a save and then inspecting the "unsaved changes" section,
# or uci reorder network.@[#] where # represents number (see above [1]) of config line entry
# in your 'network' file, and then using (uci changes) to view the cfg0xxxxxx
# or using (uci show network.'cfgxxxxxx') if you happen to know xxxxxx
# Last entry will become path>wg0 tunnel. In this ex. cfg0e6912 is path.
# This example demonstrate five peers added via uci or Luci.
#
# cfg0a6912 #example cfg0a6912 is fr-bod
# cfg0b6912 #example cfg0a6912 is jp-tok
# cfg0c6912 #example cfg0a6912 is it-rom
# cfg0d6912 #example cfg0a6912 is pl-waw
# cfg0e6912 #example cfg0a6912 is us-nyc
#
# ***Issuing a reorder command to move from us-nyc onto pl-waw***
# Since us-nyc is the 13th config line [13] and currently cfg0e6912
# Since pl-waw is the 12th config line [12] and currently cfg0d6912
# uci the following...
#
#root@Dachshund:~# uci reorder network.@[13]=12
#root@Dachshund:~# uci changes
#network.cfg0e6912='12'
#uci: Entry not found
#uci: Entry not found
#uci: Entry not found
#uci: Entry not found
#uci: Entry not found
#root@Dachshund:~# uci export network
#package network
#
#config interface 'loopback'
# option ifname 'lo'
# option proto 'static'
# option ipaddr '127.0.0.1'
# option netmask '255.0.0.0'
#
#config globals 'globals'
# option ula_prefix '0:0:0:0::/0'
#
#### TRUNCATED ####
#
#config wireguard_SSWG
# option public_key 'rhuoCmHdyYrh0zW3J0YXZK4aN3It7DD26TXlACuWnwU='
# option peersistent_keepalive '25'
# option endpoint_port '51820'
# list allowed_ips '0.0.0.0/0'
# list allowed_ips '::/0'
# option route_allowed_ips '1'
# option endpoint_host 'us-nyc.prod.surfshark.com'
# option description 'nyc-prod'
#
#config wireguard_SSWG
# option public_key 'vBa3HK7QXietG64rHRLm085VMS2cAX2paeAaphB/SEU='
# option persistent_keepalive '25'
# option endpoint_port '51820'
# list allowed_ips '0.0.0.0/0'
# list allowed_ips '::/0'
# option route_allowed_ips '1'
# option endpoint_host 'pl-waw.prod.surfshark.com'
# option description 'waw-prod'
#
#root@Dachshund:~# uci commit ; /etc/init.d/network restart
#
# Now pl-waw takes the CFGID of cfg0e6912 and position of 13th and is VPN tun.
# Now us-nyc takes the CFGID of cfg0d6912 and position of 12th.
# Changes will be reflected in the Peer Tab of Setup and the WireGuard Status page.
###################################################################################
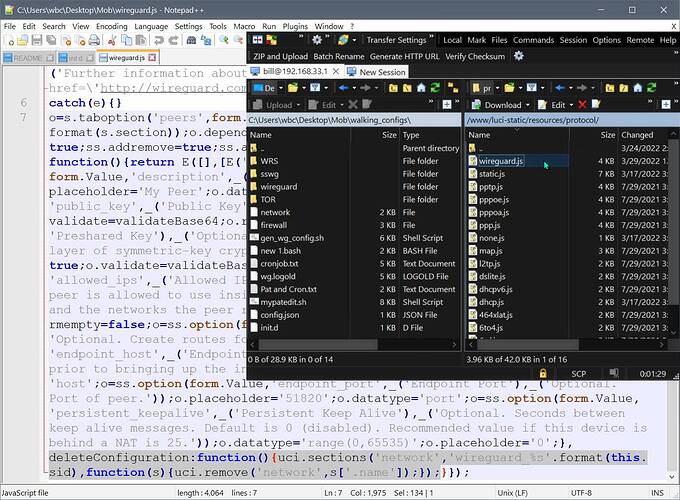
 © Copyright 2015-2022 Jason A. Donenfeld. All Rights Reserved. "WireGuard" and the "WireGuard" logo are registered trademarks of Jason A. Donenfeld.
© Copyright 2015-2022 Jason A. Donenfeld. All Rights Reserved. "WireGuard" and the "WireGuard" logo are registered trademarks of Jason A. Donenfeld.