Brilliant! Thanks for the help.That fixed most of the issues.
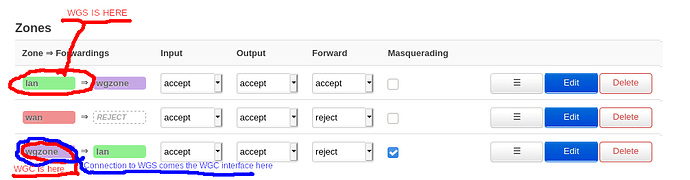
I now can connect to the network and browse internet as if I were at home. However, I still cannot connect to my raspberry pi via ssh when connected through the WGS. My RPi is located in the lan fw zone on the LAN interface. The RPi is on the 192.168.99.1/24 subnet while the WGS is on the 192.168.100.1/24 subnet (in the same fw zone), could this be related to the issue?
A few other followup questions as well.
What fw zone forwardings are necessary and which packages should I allow/disallow?
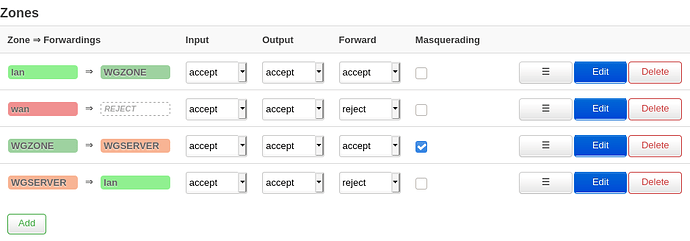
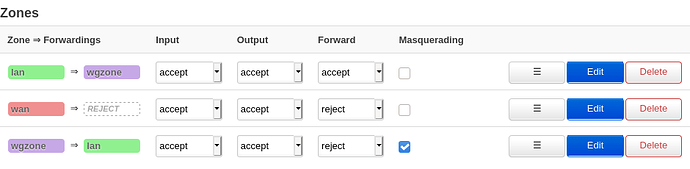
Now I configured it like this:
Output from the same command as previous post
{
"kernel": "4.14.195",
"hostname": "OpenWrt",
"system": "ARMv7 Processor rev 1 (v7l)",
"model": "Linksys WRT1900ACS",
"board_name": "linksys,shelby",
"release": {
"distribution": "OpenWrt",
"version": "19.07.4",
"revision": "r11208-ce6496d796",
"target": "mvebu/cortexa9",
"description": "OpenWrt 19.07.4 r11208-ce6496d796"
}
}
package network
config interface 'loopback'
option ifname 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fdbb:cb69:ed08::/48'
config interface 'lan'
option type 'bridge'
option ifname 'eth0.1'
option proto 'static'
option netmask '255.255.255.0'
option ip6assign '60'
option ipaddr '192.168.99.1'
config interface 'wan'
option ifname 'eth1.2'
option proto 'dhcp'
config interface 'wan6'
option ifname 'eth1.2'
option proto 'dhcpv6'
config switch
option name 'switch0'
option reset '1'
option enable_vlan '1'
config switch_vlan
option device 'switch0'
option vlan '1'
option ports '0 1 2 3 5t'
config switch_vlan
option device 'switch0'
option vlan '2'
option ports '4 6t'
config interface 'WGINTERFACE'
option proto 'wireguard'
option force_link '1'
option listen_port 'xxx
option private_key 'PRIVATEKEY'
list addresses 'xxx.xxx.xxx.xxx'
config wireguard_WGINTERFACE
option endpoint_port 'xxx'
list allowed_ips '0.0.0.0/0'
option route_allowed_ips '1'
option persistent_keepalive '25'
option public_key 'PUBLICKEY'
option endpoint_host 'xxx.xxx.xxx.xxx'
option description 'Mullvad xxx'
config interface 'WGSERVER'
option proto 'wireguard'
option private_key 'PRIVATEKEY'
option force_link '1'
option listen_port 'xxx'
list addresses '192.168.100.1/24'
config wireguard_WGSERVER
option persistent_keepalive '25'
option public_key 'PUBLICKEY'
option description 'HOME'
option route_allowed_ips '1'
option endpoint_port 'xxx'
list allowed_ips '192.168.100.70/32'
package dhcp
config dnsmasq
option domainneeded '1'
option localise_queries '1'
option rebind_protection '1'
option rebind_localhost '1'
option local '/lan/'
option domain 'lan'
option expandhosts '1'
option authoritative '1'
option readethers '1'
option leasefile '/tmp/dhcp.leases'
option resolvfile '/tmp/resolv.conf.auto'
option localservice '1'
option confdir '/tmp/dnsmasq.d'
config dhcp 'lan'
option interface 'lan'
option start '100'
option limit '150'
option leasetime '12h'
option dhcpv6 'server'
option ra 'server'
option ra_management '1'
list dhcp_option 'xxx'
config dhcp 'wan'
option interface 'wan'
option ignore '1'
config odhcpd 'odhcpd'
option maindhcp '0'
option leasefile '/tmp/hosts/odhcpd'
option leasetrigger '/usr/sbin/odhcpd-update'
option loglevel '4'
package firewall
config defaults
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
option synflood_protect '1'
config zone
option input 'ACCEPT'
option output 'ACCEPT'
option network 'lan WGSERVER'
option name 'lan'
option forward 'ACCEPT'
config zone
option name 'wan'
option forward 'REJECT'
option network 'wan wan6'
option output 'ACCEPT'
option input 'ACCEPT'
config rule
option name 'Allow-DHCP-Renew'
option src 'wan'
option proto 'udp'
option dest_port '68'
option target 'ACCEPT'
option family 'ipv4'
config rule
option name 'Allow-Ping'
option src 'wan'
option proto 'icmp'
option icmp_type 'echo-request'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-IGMP'
option src 'wan'
option proto 'igmp'
option family 'ipv4'
option target 'ACCEPT'
config rule
option name 'Allow-DHCPv6'
option src 'wan'
option proto 'udp'
option src_ip 'fc00::/6'
option dest_ip 'fc00::/6'
option dest_port '546'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-MLD'
option src 'wan'
option proto 'icmp'
option src_ip 'fe80::/10'
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Input'
option src 'wan'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
list icmp_type 'router-solicitation'
list icmp_type 'neighbour-solicitation'
list icmp_type 'router-advertisement'
list icmp_type 'neighbour-advertisement'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-ICMPv6-Forward'
option src 'wan'
option dest '*'
option proto 'icmp'
list icmp_type 'echo-request'
list icmp_type 'echo-reply'
list icmp_type 'destination-unreachable'
list icmp_type 'packet-too-big'
list icmp_type 'time-exceeded'
list icmp_type 'bad-header'
list icmp_type 'unknown-header-type'
option limit '1000/sec'
option family 'ipv6'
option target 'ACCEPT'
config rule
option name 'Allow-IPSec-ESP'
option src 'wan'
option proto 'esp'
option target 'ACCEPT'
option dest 'lan'
config rule
option name 'Allow-ISAKMP'
option src 'wan'
option dest_port '500'
option proto 'udp'
option target 'ACCEPT'
option dest 'lan'
config include
option path '/etc/firewall.user'
config zone
option output 'ACCEPT'
option mtu_fix '1'
option masq '1'
option network 'WGINTERFACE'
option name 'wgzone'
option forward 'REJECT'
option input 'ACCEPT'
config redirect 'adblock_dns_53'
option name 'Adblock DNS, port 53'
option proto 'tcp udp'
option src_dport '53'
option dest_port '53'
option target 'DNAT'
option src 'lan'
config redirect 'adblock_dns_853'
option name 'Adblock DNS, port 853'
option proto 'tcp udp'
option src_dport '853'
option dest_port '853'
option target 'DNAT'
option src 'lan'
config redirect 'adblock_dns_5353'
option name 'Adblock DNS, port 5353'
option proto 'tcp udp'
option src_dport '5353'
option dest_port '5353'
option target 'DNAT'
option src 'lan'
config forwarding
option src 'lan'
option dest 'wgzone'
config forwarding
option dest 'lan'
option src 'wgzone'
# This file is interpreted as shell script.
# Put your custom iptables rules here, they will
# be executed with each firewall (re-)start.
# Internal uci firewall chains are flushed and recreated on reload, so
# put custom rules into the root chains e.g. INPUT or FORWARD or into the
# special user chains, e.g. input_wan_rule or postrouting_lan_rule.
# Generated by iptables-save v1.8.3 on Wed Dec 2 13:30:36 2020
*nat
:PREROUTING ACCEPT [186:46608]
:INPUT ACCEPT [154:21944]
:OUTPUT ACCEPT [36:2533]
:POSTROUTING ACCEPT [17:1183]
:postrouting_lan_rule - [0:0]
:postrouting_rule - [0:0]
:postrouting_wan_rule - [0:0]
:postrouting_wgzone_rule - [0:0]
:prerouting_lan_rule - [0:0]
:prerouting_rule - [0:0]
:prerouting_wan_rule - [0:0]
:prerouting_wgzone_rule - [0:0]
:zone_lan_postrouting - [0:0]
:zone_lan_prerouting - [0:0]
:zone_wan_postrouting - [0:0]
:zone_wan_prerouting - [0:0]
:zone_wgzone_postrouting - [0:0]
:zone_wgzone_prerouting - [0:0]
[225:49658] -A PREROUTING -m comment --comment "!fw3: Custom prerouting rule chain" -j prerouting_rule
[87:29381] -A PREROUTING -i br-lan -m comment --comment "!fw3" -j zone_lan_prerouting
[32:1971] -A PREROUTING -i WGSERVER -m comment --comment "!fw3" -j zone_lan_prerouting
[105:18130] -A PREROUTING -i eth1.2 -m comment --comment "!fw3" -j zone_wan_prerouting
[1:176] -A PREROUTING -i WGINTERFACE -m comment --comment "!fw3" -j zone_wgzone_prerouting
[81:25129] -A POSTROUTING -m comment --comment "!fw3: Custom postrouting rule chain" -j postrouting_rule
[10:672] -A POSTROUTING -o br-lan -m comment --comment "!fw3" -j zone_lan_postrouting
[0:0] -A POSTROUTING -o WGSERVER -m comment --comment "!fw3" -j zone_lan_postrouting
[0:0] -A POSTROUTING -o eth1.2 -m comment --comment "!fw3" -j zone_wan_postrouting
[64:23946] -A POSTROUTING -o WGINTERFACE -m comment --comment "!fw3" -j zone_wgzone_postrouting
[10:672] -A zone_lan_postrouting -m comment --comment "!fw3: Custom lan postrouting rule chain" -j postrouting_lan_rule
[119:31352] -A zone_lan_prerouting -m comment --comment "!fw3: Custom lan prerouting rule chain" -j prerouting_lan_rule
[0:0] -A zone_lan_prerouting -p tcp -m tcp --dport 53 -m comment --comment "!fw3: Adblock DNS, port 53" -j REDIRECT --to-ports 53
[37:2513] -A zone_lan_prerouting -p udp -m udp --dport 53 -m comment --comment "!fw3: Adblock DNS, port 53" -j REDIRECT --to-ports 53
[0:0] -A zone_lan_prerouting -p tcp -m tcp --dport 853 -m comment --comment "!fw3: Adblock DNS, port 853" -j REDIRECT --to-ports 853
[0:0] -A zone_lan_prerouting -p udp -m udp --dport 853 -m comment --comment "!fw3: Adblock DNS, port 853" -j REDIRECT --to-ports 853
[0:0] -A zone_lan_prerouting -p tcp -m tcp --dport 5353 -m comment --comment "!fw3: Adblock DNS, port 5353" -j REDIRECT --to-ports 5353
[2:537] -A zone_lan_prerouting -p udp -m udp --dport 5353 -m comment --comment "!fw3: Adblock DNS, port 5353" -j REDIRECT --to-ports 5353
[0:0] -A zone_wan_postrouting -m comment --comment "!fw3: Custom wan postrouting rule chain" -j postrouting_wan_rule
[105:18130] -A zone_wan_prerouting -m comment --comment "!fw3: Custom wan prerouting rule chain" -j prerouting_wan_rule
[64:23946] -A zone_wgzone_postrouting -m comment --comment "!fw3: Custom wgzone postrouting rule chain" -j postrouting_wgzone_rule
[64:23946] -A zone_wgzone_postrouting -m comment --comment "!fw3" -j MASQUERADE
[1:176] -A zone_wgzone_prerouting -m comment --comment "!fw3: Custom wgzone prerouting rule chain" -j prerouting_wgzone_rule
COMMIT
# Completed on Wed Dec 2 13:30:36 2020
# Generated by iptables-save v1.8.3 on Wed Dec 2 13:30:36 2020
*mangle
:PREROUTING ACCEPT [7852:1829500]
:INPUT ACCEPT [4395:1140572]
:FORWARD ACCEPT [3431:683810]
:OUTPUT ACCEPT [3882:1223598]
:POSTROUTING ACCEPT [7313:1907408]
[16:984] -A FORWARD -o WGINTERFACE -p tcp -m tcp --tcp-flags SYN,RST SYN -m comment --comment "!fw3: Zone wgzone MTU fixing" -j TCPMSS --clamp-mss-to-pmtu
[16:936] -A FORWARD -i WGINTERFACE -p tcp -m tcp --tcp-flags SYN,RST SYN -m comment --comment "!fw3: Zone wgzone MTU fixing" -j TCPMSS --clamp-mss-to-pmtu
COMMIT
# Completed on Wed Dec 2 13:30:36 2020
# Generated by iptables-save v1.8.3 on Wed Dec 2 13:30:36 2020
*filter
:INPUT ACCEPT [0:0]
:FORWARD DROP [0:0]
:OUTPUT ACCEPT [0:0]
:forwarding_lan_rule - [0:0]
:forwarding_rule - [0:0]
:forwarding_wan_rule - [0:0]
:forwarding_wgzone_rule - [0:0]
:input_lan_rule - [0:0]
:input_rule - [0:0]
:input_wan_rule - [0:0]
:input_wgzone_rule - [0:0]
:output_lan_rule - [0:0]
:output_rule - [0:0]
:output_wan_rule - [0:0]
:output_wgzone_rule - [0:0]
:reject - [0:0]
:syn_flood - [0:0]
:zone_lan_dest_ACCEPT - [0:0]
:zone_lan_forward - [0:0]
:zone_lan_input - [0:0]
:zone_lan_output - [0:0]
:zone_lan_src_ACCEPT - [0:0]
:zone_wan_dest_ACCEPT - [0:0]
:zone_wan_dest_REJECT - [0:0]
:zone_wan_forward - [0:0]
:zone_wan_input - [0:0]
:zone_wan_output - [0:0]
:zone_wan_src_ACCEPT - [0:0]
:zone_wgzone_dest_ACCEPT - [0:0]
:zone_wgzone_dest_REJECT - [0:0]
:zone_wgzone_forward - [0:0]
:zone_wgzone_input - [0:0]
:zone_wgzone_output - [0:0]
:zone_wgzone_src_ACCEPT - [0:0]
[126:11802] -A INPUT -i lo -m comment --comment "!fw3" -j ACCEPT
[4269:1128770] -A INPUT -m comment --comment "!fw3: Custom input rule chain" -j input_rule
[4073:1104661] -A INPUT -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
[8:492] -A INPUT -p tcp -m tcp --tcp-flags FIN,SYN,RST,ACK SYN -m comment --comment "!fw3" -j syn_flood
[49:4003] -A INPUT -i br-lan -m comment --comment "!fw3" -j zone_lan_input
[17:984] -A INPUT -i WGSERVER -m comment --comment "!fw3" -j zone_lan_input
[129:18946] -A INPUT -i eth1.2 -m comment --comment "!fw3" -j zone_wan_input
[1:176] -A INPUT -i WGINTERFACE -m comment --comment "!fw3" -j zone_wgzone_input
[3431:683810] -A FORWARD -m comment --comment "!fw3: Custom forwarding rule chain" -j forwarding_rule
[3368:659990] -A FORWARD -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
[25:21324] -A FORWARD -i br-lan -m comment --comment "!fw3" -j zone_lan_forward
[38:2496] -A FORWARD -i WGSERVER -m comment --comment "!fw3" -j zone_lan_forward
[0:0] -A FORWARD -i eth1.2 -m comment --comment "!fw3" -j zone_wan_forward
[0:0] -A FORWARD -i WGINTERFACE -m comment --comment "!fw3" -j zone_wgzone_forward
[0:0] -A FORWARD -m comment --comment "!fw3" -j reject
[126:11802] -A OUTPUT -o lo -m comment --comment "!fw3" -j ACCEPT
[3756:1211796] -A OUTPUT -m comment --comment "!fw3: Custom output rule chain" -j output_rule
[3727:1209774] -A OUTPUT -m conntrack --ctstate RELATED,ESTABLISHED -m comment --comment "!fw3" -j ACCEPT
[0:0] -A OUTPUT -o br-lan -m comment --comment "!fw3" -j zone_lan_output
[0:0] -A OUTPUT -o WGSERVER -m comment --comment "!fw3" -j zone_lan_output
[0:0] -A OUTPUT -o eth1.2 -m comment --comment "!fw3" -j zone_wan_output
[29:2022] -A OUTPUT -o WGINTERFACE -m comment --comment "!fw3" -j zone_wgzone_output
[0:0] -A reject -p tcp -m comment --comment "!fw3" -j REJECT --reject-with tcp-reset
[0:0] -A reject -m comment --comment "!fw3" -j REJECT --reject-with icmp-port-unreachable
[8:492] -A syn_flood -p tcp -m tcp --tcp-flags FIN,SYN,RST,ACK SYN -m limit --limit 25/sec --limit-burst 50 -m comment --comment "!fw3" -j RETURN
[0:0] -A syn_flood -m comment --comment "!fw3" -j DROP
[28:1896] -A zone_lan_dest_ACCEPT -o br-lan -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_lan_dest_ACCEPT -o WGSERVER -m comment --comment "!fw3" -j ACCEPT
[63:23820] -A zone_lan_forward -m comment --comment "!fw3: Custom lan forwarding rule chain" -j forwarding_lan_rule
[63:23820] -A zone_lan_forward -m comment --comment "!fw3: Zone lan to wgzone forwarding policy" -j zone_wgzone_dest_ACCEPT
[0:0] -A zone_lan_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[28:1896] -A zone_lan_forward -m comment --comment "!fw3" -j zone_lan_dest_ACCEPT
[66:4987] -A zone_lan_input -m comment --comment "!fw3: Custom lan input rule chain" -j input_lan_rule
[46:3607] -A zone_lan_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[20:1380] -A zone_lan_input -m comment --comment "!fw3" -j zone_lan_src_ACCEPT
[0:0] -A zone_lan_output -m comment --comment "!fw3: Custom lan output rule chain" -j output_lan_rule
[0:0] -A zone_lan_output -m comment --comment "!fw3" -j zone_lan_dest_ACCEPT
[15:1080] -A zone_lan_src_ACCEPT -i br-lan -m conntrack --ctstate NEW,UNTRACKED -m comment --comment "!fw3" -j ACCEPT
[5:300] -A zone_lan_src_ACCEPT -i WGSERVER -m conntrack --ctstate NEW,UNTRACKED -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_wan_dest_ACCEPT -o eth1.2 -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_wan_dest_REJECT -o eth1.2 -m comment --comment "!fw3" -j reject
[0:0] -A zone_wan_forward -m comment --comment "!fw3: Custom wan forwarding rule chain" -j forwarding_wan_rule
[0:0] -A zone_wan_forward -p esp -m comment --comment "!fw3: Allow-IPSec-ESP" -j zone_lan_dest_ACCEPT
[0:0] -A zone_wan_forward -p udp -m udp --dport 500 -m comment --comment "!fw3: Allow-ISAKMP" -j zone_lan_dest_ACCEPT
[0:0] -A zone_wan_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[0:0] -A zone_wan_forward -m comment --comment "!fw3" -j zone_wan_dest_REJECT
[129:18946] -A zone_wan_input -m comment --comment "!fw3: Custom wan input rule chain" -j input_wan_rule
[0:0] -A zone_wan_input -p udp -m udp --dport 68 -m comment --comment "!fw3: Allow-DHCP-Renew" -j ACCEPT
[0:0] -A zone_wan_input -p icmp -m icmp --icmp-type 8 -m comment --comment "!fw3: Allow-Ping" -j ACCEPT
[24:816] -A zone_wan_input -p igmp -m comment --comment "!fw3: Allow-IGMP" -j ACCEPT
[0:0] -A zone_wan_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[105:18130] -A zone_wan_input -m comment --comment "!fw3" -j zone_wan_src_ACCEPT
[0:0] -A zone_wan_output -m comment --comment "!fw3: Custom wan output rule chain" -j output_wan_rule
[0:0] -A zone_wan_output -m comment --comment "!fw3" -j zone_wan_dest_ACCEPT
[105:18130] -A zone_wan_src_ACCEPT -i eth1.2 -m conntrack --ctstate NEW,UNTRACKED -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_wgzone_dest_ACCEPT -o WGINTERFACE -m conntrack --ctstate INVALID -m comment --comment "!fw3: Prevent NAT leakage" -j DROP
[64:23946] -A zone_wgzone_dest_ACCEPT -o WGINTERFACE -m comment --comment "!fw3" -j ACCEPT
[0:0] -A zone_wgzone_dest_REJECT -o WGINTERFACE -m comment --comment "!fw3" -j reject
[0:0] -A zone_wgzone_forward -m comment --comment "!fw3: Custom wgzone forwarding rule chain" -j forwarding_wgzone_rule
[0:0] -A zone_wgzone_forward -m comment --comment "!fw3: Zone wgzone to lan forwarding policy" -j zone_lan_dest_ACCEPT
[0:0] -A zone_wgzone_forward -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port forwards" -j ACCEPT
[0:0] -A zone_wgzone_forward -m comment --comment "!fw3" -j zone_wgzone_dest_REJECT
[1:176] -A zone_wgzone_input -m comment --comment "!fw3: Custom wgzone input rule chain" -j input_wgzone_rule
[0:0] -A zone_wgzone_input -m conntrack --ctstate DNAT -m comment --comment "!fw3: Accept port redirections" -j ACCEPT
[1:176] -A zone_wgzone_input -m comment --comment "!fw3" -j zone_wgzone_src_ACCEPT
[29:2022] -A zone_wgzone_output -m comment --comment "!fw3: Custom wgzone output rule chain" -j output_wgzone_rule
[29:2022] -A zone_wgzone_output -m comment --comment "!fw3" -j zone_wgzone_dest_ACCEPT
[1:176] -A zone_wgzone_src_ACCEPT -i WGINTERFACE -m conntrack --ctstate NEW,UNTRACKED -m comment --comment "!fw3" -j ACCEPT
COMMIT
# Completed on Wed Dec 2 13:30:36 2020
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
7: br-lan: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
inet 192.168.99.1/24 brd 192.168.99.255 scope global br-lan
valid_lft forever preferred_lft forever
9: eth1.2@eth1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
inet 192.168.0.55/24 brd 192.168.0.255 scope global eth1.2
valid_lft forever preferred_lft forever
10: WGSERVER: <POINTOPOINT,NOARP,UP,LOWER_UP> mtu 1420 qdisc noqueue state UNKNOWN group default qlen 1000
inet 192.168.100.1/24 brd 192.168.100.255 scope global WGSERVER
valid_lft forever preferred_lft forever
13: WGINTERFACE: <POINTOPOINT,NOARP,UP,LOWER_UP> mtu 1420 qdisc noqueue state UNKNOWN group default qlen 1000
inet xxx.xxx.xxx.xxx/32 brd 255.255.255.255 scope global WGINTERFACE
valid_lft forever preferred_lft forever
default dev WGINTERFACE proto static scope link
192.168.0.0/24 dev eth1.2 proto kernel scope link src 192.168.0.55
192.168.99.0/24 dev br-lan proto kernel scope link src 192.168.99.1
192.168.100.0/24 dev WGSERVER proto kernel scope link src 192.168.100.1
192.168.100.70 dev WGSERVER proto static scope link
xxx.xxx.xxx.xxx via 192.168.0.1 dev eth1.2 proto static
local xxx.xxx.xxx.xxx dev WGINTERFACE table local proto kernel scope host src xxx.xxx.xxx.xxx
broadcast 127.0.0.0 dev lo table local proto kernel scope link src 127.0.0.1
local 127.0.0.0/8 dev lo table local proto kernel scope host src 127.0.0.1
local 127.0.0.1 dev lo table local proto kernel scope host src 127.0.0.1
broadcast 127.255.255.255 dev lo table local proto kernel scope link src 127.0.0.1
broadcast 192.168.0.0 dev eth1.2 table local proto kernel scope link src 192.168.0.55
local 192.168.0.55 dev eth1.2 table local proto kernel scope host src 192.168.0.55
broadcast 192.168.0.255 dev eth1.2 table local proto kernel scope link src 192.168.0.55
broadcast 192.168.99.0 dev br-lan table local proto kernel scope link src 192.168.99.1
local 192.168.99.1 dev br-lan table local proto kernel scope host src 192.168.99.1
broadcast 192.168.99.255 dev br-lan table local proto kernel scope link src 192.168.99.1
broadcast 192.168.100.0 dev WGSERVER table local proto kernel scope link src 192.168.100.1
local 192.168.100.1 dev WGSERVER table local proto kernel scope host src 192.168.100.1
broadcast 192.168.100.255 dev WGSERVER table local proto kernel scope link src 192.168.100.1
0: from all lookup local
32766: from all lookup main
32767: from all lookup default
Forwarding wgzone to lan. And then accepting input and output from wgzone.
Is this necessary?
Would it wake sense to move the WGC to the lan zone or do I want to keep it separate because of MSS Clamping and masquerading settings?
Thank you!