Where is a good place to share common exposures that are being ignored by the threat reporting community?
Context is everything. This forum is focused on OpenWrt, so posting general security concerns that are unrelated (or only tangentially so) is probably not really appropriate here. But obviously concerns or thoughts regarding OpenWrt specific security would be welcomed.
What were you thinking about specifically?
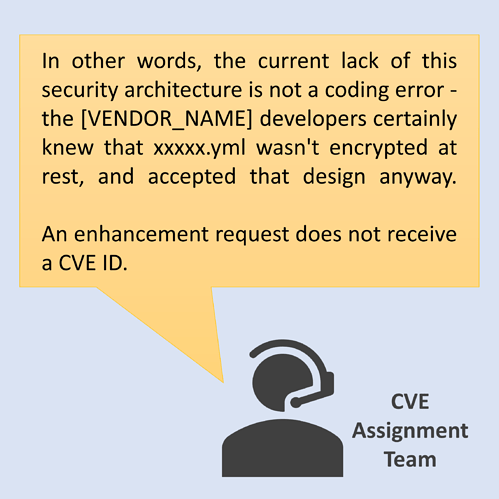
Both the GitHub CLI and the AWS CLI/SDK have exposures which are easily exploited.
If the GitHub CLI and/or any tools using the AWS CLI or SDK are used as part of the development or CI/CD process for OpenWRT it might be a good idea to make sure these tools are made secure.
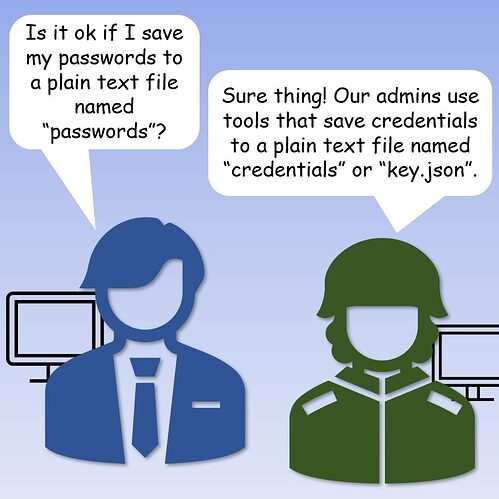
Specifically both store credentials in plain text files (yml for GitHub CLI and "credentials" for AWS SDK/CLI)
Both tools can be exploited by any local process to execute commands available to the respective account.
Here is a link to the AWS official docs: "Loading credentials in Node.js from the shared credentials file - AWS SDK for JavaScript". Seriously, that's the literal page name.
It would be remarkably easy for an actor to exploit the GitHub CLI to execute a code manipulation including PR and merge.
Check your tools please.
I'd put this in the developers section as a question: "Does OpenWrt use the AWS CLI/SDK?" -- if so, a security warning...
The developers are likely to be able to answer and address the concern (or to say that it is not relevant because of whatever reasons).