I'm on an adventure to get IPv6 working, but so far OpenWrt seems unable to reach IPv6 hosts on the WAN connection.
My goal is to have my LAN working with both IPv4 and IPv6.
# ping6 -c2 -I eth0.2 www.google.com
PING www.google.com (2a00:1450:400e:807::2004): 56 data bytes
--- www.google.com ping statistics ---
2 packets transmitted, 0 packets received, 100% packet loss
# ping -c2 -I eth0.2 www.google.com
PING www.google.com (172.217.17.132): 56 data bytes
64 bytes from 172.217.17.132: seq=0 ttl=58 time=3.054 ms
64 bytes from 172.217.17.132: seq=1 ttl=58 time=2.814 ms
--- www.google.com ping statistics ---
2 packets transmitted, 2 packets received, 0% packet loss
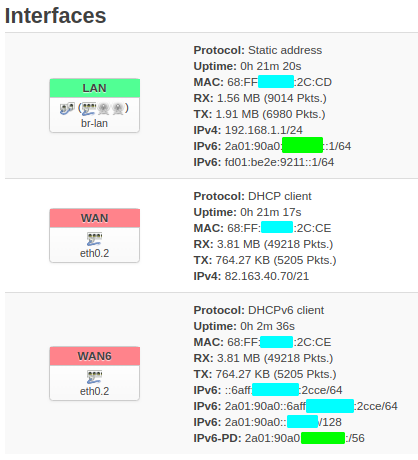
The interface is connected:
Device: eth0.2
Uptime: 2h 40m 22s
MAC: 68:FF:7B:2B:2C:CE
RX: 167.30 MB (714022 Pkts.)
TX: 12.41 MB (87381 Pkts.)
IPv6: ::6aff:[...]:2cce/64
IPv6: 2a01:90a0::6aff:[...]:2cce/64
IPv6-PD: 2a01:90a0:1ff:fb00::/56
Network layout
[ISP] -> bridged ISP router -> OpenWrt router -> [LAN]
The ISP supports IPv6, has their own IPv6 DNS, and configures this via DHCP.
The OpenWrt router is a TP-link Archer C7 with OpenWrt 18.06.4 .
What I've tried
- reset the router to factory default
- checked if the wan6 interface was connected. It is. Gets IPv6, DNS and everything.
- checked for any blocking firewall rules
-
ping6 www.google.comfrom the router (ssh login). This did resolve to an IPv6 address, but was unable to reach the host - checked configs and routing tables. It looks okay to me, but this is where I get confused, as I don't really know what an IPv6 config should look like.
- connected my laptop directly to the bridged ISP router. This worked perfectly. I got an IPv6 address, and the test at http://v6.testmyipv6.com/ showed a triumph, huge success, so the IPv6 connection from the bridged router is working fine.
- searching the web, comparing settings, trying out different settings (mostly through LuCi)
Configs
Not sure exactly what you need, but maybe these help. I'm happy to provide more specific info.
ifstatus
# ifstatus wan6
{
"up": true,
"pending": false,
"available": true,
"autostart": true,
"dynamic": false,
"uptime": 1147,
"l3_device": "eth0.2",
"proto": "dhcpv6",
"device": "eth0.2",
"metric": 0,
"dns_metric": 0,
"delegation": true,
"ipv4-address": [
],
"ipv6-address": [
{
"address": "::6aff:[...]:2cce",
"mask": 64,
"preferred": 604322,
"valid": 2591522
},
{
"address": "2a01:90a0::6aff:[...]:2cce",
"mask": 64,
"preferred": 604521,
"valid": 2591721
}
],
"ipv6-prefix": [
{
"address": "2a01:90a0:1ff:fb00::",
"mask": 56,
"preferred": 376853,
"valid": 603653,
"class": "wan6",
"assigned": {
"lan": {
"address": "2a01:90a0:1ff:fb00::",
"mask": 60
}
}
}
],
"ipv6-prefix-assignment": [
],
"route": [
{
"target": "::",
"mask": 64,
"nexthop": "::",
"metric": 256,
"valid": 2591522,
"source": "::\/0"
},
{
"target": "2a01:90a0::",
"mask": 64,
"nexthop": "::",
"metric": 256,
"valid": 2591721,
"source": "::\/0"
},
{
"target": "::",
"mask": 0,
"nexthop": "fe80::1",
"metric": 512,
"valid": 1700,
"source": "2a01:90a0:1ff:fb00::\/56"
},
{
"target": "::",
"mask": 0,
"nexthop": "fe80::1",
"metric": 512,
"valid": 1700,
"source": "::6aff:[...]:2cce\/64"
},
{
"target": "::",
"mask": 0,
"nexthop": "fe80::1",
"metric": 512,
"valid": 1700,
"source": "2a01:90a0::6aff:[...]:2cce\/64"
}
],
"dns-server": [
"2a03:[...]::6",
"2a03:[...]::7",
"fe80::1"
],
"dns-search": [
],
"inactive": {
"ipv4-address": [
],
"ipv6-address": [
],
"route": [
],
"dns-server": [
],
"dns-search": [
]
},
"data": {
"passthru": "001700202a0381801001017400000000000000062a038180140100bb0000000000000007"
}
}
ip route and ip rule
# ip -6 route
default from ::/64 via fe80::1 dev eth0.2 metric 512
default from 2a01:90a0::/64 via fe80::1 dev eth0.2 metric 512
default from 2a01:90a0:1ff:fb00::/56 via fe80::1 dev eth0.2 metric 512
::/64 dev eth0.2 metric 256
2a01:90a0::/64 dev eth0.2 metric 256
2a01:90a0:1ff:fb00::/64 dev br-lan metric 1024
unreachable 2a01:90a0:1ff:fb00::/56 dev lo metric 2147483647 error -148
fddb:b901:3a6f::/64 dev br-lan metric 1024
unreachable fddb:b901:3a6f::/48 dev lo metric 2147483647 error -148
fe80::/64 dev eth0 metric 256
fe80::/64 dev eth0.2 metric 256
fe80::/64 dev br-lan metric 256
unreachable default dev lo metric -1 error -128
ff00::/8 dev eth0 metric 256
ff00::/8 dev br-lan metric 256
ff00::/8 dev eth0.2 metric 256
unreachable default dev lo metric -1 error -128
# ip -6 rule
0: from all lookup local
32766: from all lookup main
4200000000: from 2a01:90a0:1ff:fb00::1/60 iif br-lan lookup unspec unreachable
4200000001: from all iif lo lookup unspec 12
4200000005: from all iif br-lan lookup unspec 12
4200000007: from all iif eth0.2 lookup unspec 12
4200000007: from all iif eth0.2 lookup unspec 12
/etc/config/network
config interface 'loopback'
option ifname 'lo'
option proto 'static'
option ipaddr '127.0.0.1'
option netmask '255.0.0.0'
config globals 'globals'
option ula_prefix 'fddb:b901:3a6f::/48'
config interface 'lan'
option type 'bridge'
option ifname 'eth0.1'
option proto 'static'
option ipaddr '192.168.1.1'
option netmask '255.255.255.0'
option ip6assign '60'
config interface 'wan'
option ifname 'eth0.2'
option proto 'dhcp'
config device 'wan_dev'
option name 'eth0.2'
option macaddr '68:ff:7b:2b:2c:ce'
config interface 'wan6'
option ifname 'eth0.2'
option proto 'dhcpv6'
option reqaddress 'none'
option reqprefix 'auto'
config switch
option name 'switch0'
option reset '1'
option enable_vlan '1'
config switch_vlan
option device 'switch0'
option vlan '1'
option ports '2 3 4 5 0t'
config switch_vlan
option device 'switch0'
option vlan '2'
option ports '1 0t'
/etc/config/firewall
config defaults
option syn_flood 1
option input ACCEPT
option output ACCEPT
option forward REJECT
# Uncomment this line to disable ipv6 rules
# option disable_ipv6 1
config zone
option name lan
list network 'lan'
option input ACCEPT
option output ACCEPT
option forward ACCEPT
config zone
option name wan
list network 'wan'
list network 'wan6'
option input REJECThelps
option output ACCEPT
option forward REJECT
option masq 1
option mtu_fix 1
config forwarding
option src lan
option dest wan
# We need to accept udp packets on port 68,
# see https://dev.openwrt.org/ticket/4108
config rule
option name Allow-DHCP-Renew
option src wan
option proto udp
option dest_port 68
option target ACCEPT
option family ipv4
# Allow IPv4 ping
config rule
option name Allow-Ping
option src wan
option proto icmp
option icmp_type echo-request
option family ipv4
option target ACCEPT
config rule
option name Allow-IGMP
option src wan
option proto igmp
option family ipv4
option target ACCEPT
# Allow DHCPv6 replies
# see https://dev.openwrt.org/ticket/10381
config rule
option name Allow-DHCPv6
option src wan
option proto udp
option src_ip fc00::/6
option dest_ip fc00::/6
option dest_port 546
option family ipv6
option target ACCEPT
config rule
option name Allow-MLD
option src wan
option proto icmp
option src_ip fe80::/10
list icmp_type '130/0'
list icmp_type '131/0'
list icmp_type '132/0'
list icmp_type '143/0'
option family ipv6
option target ACCEPT
# Allow essential incoming IPv6 ICMP traffic
config rule
option name Allow-ICMPv6-Input
option src wan
option proto icmp
list icmp_type echo-request
list icmp_type echo-reply
list icmp_type destination-unreachable
list icmp_type packet-too-big
list icmp_type time-exceeded
list icmp_type bad-header
list icmp_type unknown-header-type
list icmp_type router-solicitation
list icmp_type neighbour-solicitation
list icmp_type router-advertisement
list icmp_type neighbour-advertisement
option limit 1000/sec
option family ipv6
option target ACCEPT
# Allow essential forwarded IPv6 ICMP traffic
config rule
option name Allow-ICMPv6-Forward
option src wan
option dest *
option proto icmp
list icmp_type echo-request
list icmp_type echo-reply
list icmp_type destination-unreachable
list icmp_type packet-too-big
list icmp_type time-exceeded
list icmp_type bad-header
list icmp_type unknown-header-type
option limit 1000/sec
option family ipv6
option target ACCEPT
config rule
option name Allow-IPSec-ESP
option src wan
option dest lan
option proto esp
option target ACCEPT
config rule
option name Allow-ISAKMP
option src wan
option dest lan
option dest_port 500
option proto udp
option target ACCEPT
# include a file with users custom iptables rules
config include
option path /etc/firewall.user
/etc/config/dhcp
config dnsmasq
option domainneeded '1'
option boguspriv '1'
option filterwin2k '0'
option localise_queries '1'
option rebind_protection '1'
option rebind_localhost '1'
option local '/lan/'
option domain 'lan'
option expandhosts '1'
option nonegcache '0'
option authoritative '1'
option readethers '1'
option leasefile '/tmp/dhcp.leases'
option resolvfile '/tmp/resolv.conf.auto'
option nonwildcard '1'
option localservice '1'
config dhcp 'lan'
option interface 'lan'
option start '100'
option limit '150'
option leasetime '12h'
option dhcpv6 'server'
option ra 'server'
config dhcp 'wan'
option interface 'wan'
option ignore '1'
config odhcpd 'odhcpd'
option maindhcp '0'
option leasefile '/tmp/hosts/odhcpd'
option leasetrigger '/usr/sbin/odhcpd-update'
option loglevel '4'
Any idea what I could be missing here?
I'm perfectly comfortable with Linux and IPv4 networks, but I'm new at OpenWrt, and IPv6 seems to be more complicated than I thought.