is your WAN ip address in the 100.64.0.0/10 range? i.e. 100.64.x.x thru to 100.127.x.x?
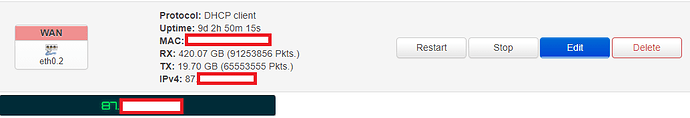
No, it is in the range of 87.xx.xx.xx/21.
And it is the same IP that the port scan sites report?
If you have a true public IP (not CG-NAT which is what the 100.x ones are), next ask your ISP if they block incoming connections.
Yes, same IP address. How can they block incoming connections? I mean, I can use the internet without any issues?
Using the internet is an outbound connection, not an inbound one.
Just to be sure again, the IP you get from https://ipleak.net/ is the exact same as the one your openwrt WAN reports, right?
Typically, the firewall can differentiate the connections by their state.
New incoming connections are recognized as NEW and incoming replies to outgoing connections as ESTABLISHED or RELATED, so they can safely block the former and allow the latter.
iptables-save -t nat -c | grep 44193
If there are hits, the rule is working.
Thank you all for your answers, I appreciate it!
Just to be sure again, the IP you get from https://ipleak.net/ is the exact same as the one your openwrt WAN reports, right?
The last digits are identical.
Typically, the firewall can differentiate the connections by their state.
New incoming connections are recognized asNEWand incoming replies to outgoing connections asESTABLISHEDorRELATED, so they can safely block the former and allow the latter.
Got it, thanks!
iptables-save -t nat -c | grep 44193
If there are hits, the rule is working.
I executed this command through the OpenWrt shell, but nothing came up. I ran the port checker tool after running the command, and then executed it again, but still no changes. What is this supposed to do?
That's weird.
iptables-save -t nat
What does it say?
# Generated by iptables-save v1.8.3 on Fri Jul 24 23:25:38 2020
*nat
:PREROUTING ACCEPT [153764:30516984]
:INPUT ACCEPT [31557:2097984]
:OUTPUT ACCEPT [44997:3138616]
:POSTROUTING ACCEPT [97:16856]
:MINIUPNPD - [0:0]
:MINIUPNPD-POSTROUTING - [0:0]
:postrouting_lan_rule - [0:0]
:postrouting_rule - [0:0]
:postrouting_wan_rule - [0:0]
:prerouting_lan_rule - [0:0]
:prerouting_rule - [0:0]
:prerouting_wan_rule - [0:0]
:zone_lan_postrouting - [0:0]
:zone_lan_prerouting - [0:0]
:zone_wan_postrouting - [0:0]
:zone_wan_prerouting - [0:0]
-A PREROUTING -m comment --comment "!fw3: Custom prerouting rule chain" -j prerouting_rule
-A PREROUTING -i br-lan -m comment --comment "!fw3" -j zone_lan_prerouting
-A PREROUTING -i eth0.2 -m comment --comment "!fw3" -j zone_wan_prerouting
-A POSTROUTING -m comment --comment "!fw3: Custom postrouting rule chain" -j postrouting_rule
-A POSTROUTING -o br-lan -m comment --comment "!fw3" -j zone_lan_postrouting
-A POSTROUTING -o eth0.2 -m comment --comment "!fw3" -j zone_wan_postrouting
-A zone_lan_postrouting -m comment --comment "!fw3: Custom lan postrouting rule chain" -j postrouting_lan_rule
-A zone_lan_prerouting -m comment --comment "!fw3: Custom lan prerouting rule chain" -j prerouting_lan_rule
-A zone_wan_postrouting -m comment --comment "!fw3: Custom wan postrouting rule chain" -j postrouting_wan_rule
-A zone_wan_postrouting -j MINIUPNPD-POSTROUTING
-A zone_wan_postrouting -m comment --comment "!fw3" -j MASQUERADE
-A zone_wan_prerouting -m comment --comment "!fw3: Custom wan prerouting rule chain" -j prerouting_wan_rule
-A zone_wan_prerouting -j MINIUPNPD
COMMIT
# Completed on Fri Jul 24 23:25:38 2020
It looks like you have removed the port forwarding.
Sorry, my bad. I enabled the port forward again and ran the first command you posted. This is the output. The part where it says "XX" is the last digits of my public IP.
[0:0] -A zone_lan_postrouting -s 192.168.1.0/24 -d 192.168.1.137/32 -p tcp -m tcp --dport 44193 -m comment --comment "!fw3: P2P (reflection)" -j SNAT --to-source 192.168.1.1
[0:0] -A zone_lan_postrouting -s 192.168.1.0/24 -d 192.168.1.137/32 -p udp -m udp --dport 44193 -m comment --comment "!fw3: P2P (reflection)" -j SNAT --to-source 192.168.1.1
[0:0] -A zone_lan_prerouting -s 192.168.1.0/24 -d 87.XX.XX.XX/32 -p tcp -m tcp --dport 44193 -m comment --comment "!fw3: P2P (reflection)" -j DNAT --to-destination 192.168.1.137:44193
[0:0] -A zone_lan_prerouting -s 192.168.1.0/24 -d 87.XX.XX.XX/32 -p udp -m udp --dport 44193 -m comment --comment "!fw3: P2P (reflection)" -j DNAT --to-destination 192.168.1.137:44193
[0:0] -A zone_wan_prerouting -p tcp -m tcp --dport 44193 -m comment --comment "!fw3: P2P" -j DNAT --to-destination 192.168.1.137:44193
[0:0] -A zone_wan_prerouting -p udp -m udp --dport 44193 -m comment --comment "!fw3: P2P" -j DNAT --to-destination 192.168.1.137:44193
It told me to let others respond...
I was gonna respond earlier...
..".because they're your Internet Service Provider."
All zeroes, nothing is reaching your router at this port.
So is this because I configured something wrong or is it because my ISP are blocking incoming connections?
OpenWrt is correctly configured.
I don't know if you should configure something on the ISP box.
If you are not sure, better consult your ISP.
What are the first numbers of your WAN IP address? You are smart not announcing your full IP address here, but the first three numbers shouldn't be an issue. That way we're sure you have a real public IP address.
I had the same problem when I had to set up port forwarding. It seems there's a bug in LuCI and it does not create all the ufw/iptables rules needed for port forwarding to work.
The workaround is to edit /etc/config/firewall to add a ufw SNAT rule manually, or just add the iptables rules directly through the custom rules page under LuCI > network > firewall.
See this thread.
Starts with: 87.7x.xx.xx
I pasted this in /etc/config/firewall and restarted the firewall:
config nat
option proto tcp
option src lan
option dest_ip 192.168.1.137
option dest_port 44193
option snat_ip 192.168.1.1
option target SNAT
It didn't work.