Hi folks.
Configuring my router and digging that issue further.
7) Get rid (block) these "broadcast messages" from Router 1 (ISP's FrizBox)
Can anybody help me with firewall rule creation please? I'd like to block these broadcast messages from FritzBox
tcpdump -i lan5 -c 100 'ether broadcast' -vvvv
tcpdump: listening on lan5, link-type EN10MB (Ethernet), snapshot length 262144 bytes
14:30:12.539633 dc:39:6f:25:f5:ee (oui Unknown) > Broadcast, ethertype Unknown (0x88e1), length 60:
0x0000: 0000 a000 b052 1ca2 fbb6 0000 0000 0000 .....R..........
0x0010: 0000 0000 0000 0000 0000 0000 0000 0000 ................
0x0020: 0000 0000 0000 0000 0000 0000 0000 ..............
14:30:12.539673 dc:39:6f:25:f5:ee (oui Unknown) > Broadcast, ethertype Unknown (0x8912), length 60:
0x0000: 0170 a000 0000 1f84 a2a3 97a2 5553 bef1 .p..........US..
0x0010: fcf9 796b 5214 13e9 e200 0000 0000 0000 ..ykR...........
0x0020: 0000 0000 0000 0000 0000 0000 0000 ..............
From what I understood, firewall4 can't help me. I even tried to allow TCP/UDP/ICMP and block everything after this rule. But it didn't help.
Next to it, I tried to implement this rule for nftable
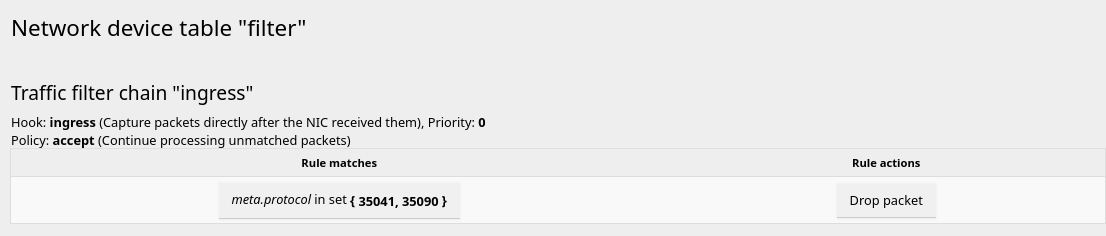
table netdev filter {
chain ingress {
type filter hook ingress device lan5 priority 0; policy accept;
meta protocol {0x8912, 0x88e1} drop
}
}
but I can't understand where and how to use that rule properly in case of OpenWRT.
I added new rule to /etc/config/firewall
config include
option type 'nftables'
option path '/etc/my_custom_firewall_rules.nft'
option position 'chain-pre'
option chain 'drop_to_wan'
to this file /etc/my_custom_firewall_rules.nft I added
meta protocol {0x8912, 0x88e1} counter drop comment "!fw4: dropping Fritz spam
then restarted FW
service firewall restart && service firewall status
Then checked up rules
fw4 -q check
But there is no new rule in a drop_to_wan chain
fw4 print | grep "chain drop_to_wan {" -A 4
and in LuCI interface too.
After that I created file
#!/usr/sbin/nft -f
table netdev filter {
chain ingress {
type filter hook ingress device lan5 priority 0; policy accept;
meta protocol {0x8912, 0x88e1} drop
}
}
applied it and now I can see that rule in a LuCI interface
but tcpdums is showing, that these broadcast packages are here. And quantity of dropped packets is growing.
Don't know how to drop these packets. Any ideas?
Thanks in advance.